CryptoWire ransomware virus is a threat that infects users’ computers making almost all of the stored data unusable. It uses the strong AES encryption algorithm that changes the file structure and then generates a key for the decryption. The creators of this offensive crypto-virus aim to extort a ransom payoff by the victims. The ransom payment should be paid in BitCoin value. However, we advise all victims to skip the ransom payment. This article provides information about the threat, instructions how to remove it and ways to stay protected in future.
| Name |
CryptoWire |
| File infix |
.encrypted. |
| Ransom |
$200 in BTC |
| Solution #1 |
CryptoWire ransomware can be removed easily with the help of an anti-malware tool, a program that will clean your computer from the virus, remove any additional cyber-security threats, and protect you in the future. |
|
Solution #2 |
CryptoWire ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Email Spam, and exploit kits. |
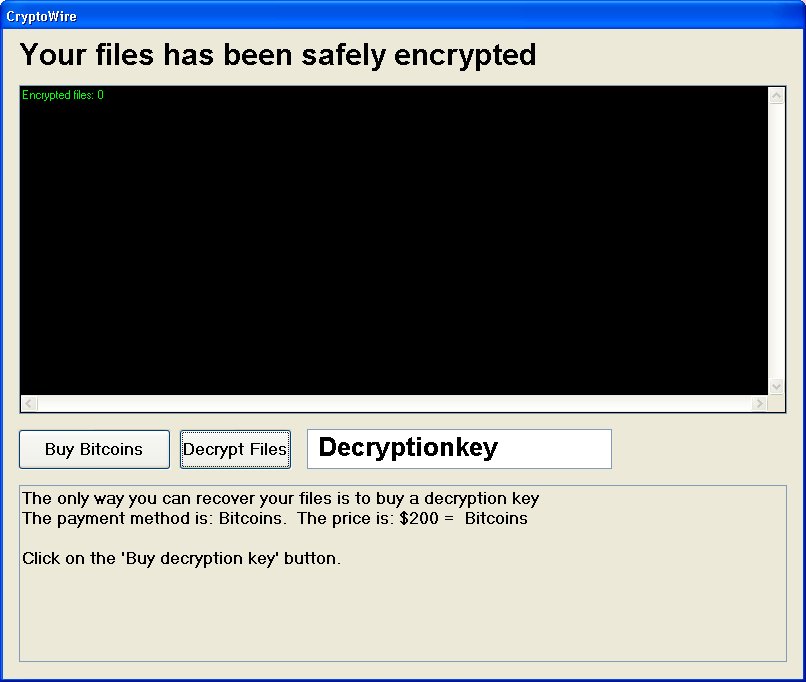
Image source: Twitter – @struppigel
Details of CryptoWire Ransomware Virus
CryptoWire ransomware uses RSA 256 encryption algorithm to lock the files. When CryptoWire crypto-virus ends the encoding process, it inserts the string .encrypted in the names of the infected files. The technique used by this ransomware is different as the chain is not appended as an extension at the end of the file names but inserted in the middle instead. The encryption template is original_file_name.encrypted.original_file_extension. So if you are a victim of CryptoWire your files are probably looking similar to this one:
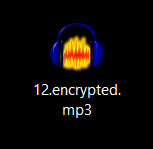
There are no specific file extensions targeted by CryptoWire, so it may encrypt all file types on the system. Furthermore, all data stored on the internal disks, external disks, network drives, USB drives, Dropbox and any cloud service that is running on the computer might be encrypted by CryptoWire ransomware once it infects the machine.
The threat is probably intended for English-speaking users. And its name is given by its creators. When the files are locked CryptoWire blocks the computer screen by displaying a window. The text in this window reads:
“Your files have been safely encrypted
/Number of encrypted records and details about their exact location /
The only way you can recover your data is to buy a decryption key
The payment method is: Bitcoins. The price is: $200 = 0,29499335 Bitcoins
Click on the “Buy decryption key” button.“
There are also two buttons and a field where should be entered the decryption key. The first button offers to buy Bitcoins by clicking it and the second is to decrypt the files once the decryption key is entered.
Spread Techniques
The ransomware is probably distributed in spam emails that have malicious links in the text body or attachments that have malicious files or scripts in them. Fake update notifications for software applications may also be used to spread the threat. Sometimes it could be distributed with links posted on social media posts or messages.
Removal Help of All CryptoWire Victims
The analysis of the threat code continues, and in case there is new information about it or a free decryption solution expect us to update this article and offer you further help. Until then we advise all victims to search for all files created by CryptoWire on the computer and delete them. The ways to do this are two. The first one is following the steps below and complete the removal manually. Try to find CryptoWire.exe file and look for other exe files that seem suspicious. The threat changes and adds some registry values that should also be completely removed. Only then the computer will normally work again. The second way is to use the help of anti-malware software. The removal process will be automatic and probably shorter.
Once all files and objects created by CryptoWire are removed we advise you to make a backup of all encrypted data and wait for a solution by the security experts. Paying the ransom will serve as an investment in further malicious actions of CryptoWire creators.
Furthermore, don’t forget to think about your security because as long as your devices are connected to the Internet they are exposed to risk of PUP or malware intrusion.
Feel free to leave us a comment whenever you need help for any security related issue.
CryptoWire Ransomware Removal
For a faster solution, you can run a scan with an advanced malware removal tool and delete CryptoWire completely with a few mouse clicks.
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely CryptoWire Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Encrypted Files
-
1) Use present backups
2) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

STEP VII: Preventive Security Measures
-
1) Enable and properly configure your Firewall.
2) Install and maintain reliable anti-malware software.
3) Secure your web browser.
4) Check regularly for available software updates and apply them.
5) Disable macros in Office documents.
6) Use strong passwords.
7) Don’t open attachments or click on links unless you’re certain they’re safe.
8) Backup regularly your data.



