An infection with the dangerous XTBL ransomware virus leads to serious security issues. Victims can restore and protect their computers by following our complete removal guide.
Manual Removal Guide
Recover XTBL- Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Distribution of XTBL Ransomware Virus
XTBL virus is a new data locker ransomware that has been released in attack campaigns against computer users worldwide. The threat could be utilizing widely used tactics of distribution to infect computer systems.
One of the easiest ways for the criminals to spread the payload of XTBL ransomware is by attaching it to email messages that are later released in active attack campaigns. The method allows hackers to send the virus to large lists of potential victims. The attachments to malicious email spam messages usually have Word documents or other types of files which users open without hesitation. Once opened on a target host these compromised files trigger the ransomware payload and infect the device with XTBL crypto virus. Other infection tactic related to emails is hyperlink inserted in the content of the messages. The links are usually labeled as leading to a familiar website or a file of user interest.
Computer criminals behind this new ransomware can be using malicious sites or download portals to distribute malware of different kinds, including XTBL virus. A popular option is the use of infected documents which may be of different types ‒ spreadsheets, rich text documents, presentations and databases. They are modified to initiate the virus once the built-in scripts are run. Usually when the files are opened a notification will ask the users to run the macros (scripts). If this is done the infection follows.
The hacker-controlled sites are specialist portals that have been created either manually or automatically by the criminals behind XTBL virus. They can either directly distribute the threat by initiating various scripts or automated operations or link to such instances. Redirects are usually caused by email interaction, ad networks or other browsing activity. However one of the main sources is the availability of browser hijackers. They are malicious add-ons made for the most popular web browsers ‒ Mozilla Firefox, Google Chrome, Internet Explorer, Opera, Microsoft Edge and Safari. Once installed they not only infect the users with the malware, but also redirect the victims to a hacker-controlled site. Depending on the configuration the browser hijackers can also steal sensitive information such as any stored passwords, account credentials, history, bookmarks, form data and settings.
Impact of XTBL Ransomware Virus
The XTBL virus is a new Scarab level strain that is being distributed against users worldwide. It appears to be another customization that is based on Scarab’s original code. It is possible that the code has been obtained from the hacker underground forums or markets. No information is available about the individual hacker or criminal collective behind it. The only meta data found in the malware files reads “Extensible Associatewith Kek Addresses Rutinely Buttons” and the false copyright reads “2006-2014 RonyaSoft”.
The new strains can begin the infection by starting up a data harvesting module. It is programmed to harvest specific strings that are categorized into two main categories:
- Personal Information — It can be used to directly identify the victim’s identity. By scanning the computers the XTBL virus can retrieve the users’s name, address, location, telephone number, interests, passwords and account credentials.
- Anonymous Data — It is mainly used by the criminals to judge how effective their campaign is. It includes harvested strings such as operating system settings and hardware data.
Using the obtained information the XTBL malware engine can launch a stealth protection component. It can scan the system for any available software that can intefere with the correct execution. Examples include anti-virus products, sandbox environments and debug environments. Further changes may impact the operating system itself.
Advanced copies of the XTML virus can add entries or modify existing ones in the Windows Registry. As a result the users will not be able to run certain applications or services. Overall computer performance can be impacted and the virus can also run in a persistent state of execution. This means that it can modify the system in such a way to make it impossible to remove by manual methods. Some strains have been found to remove the shadow volume copies of the users data. This makes recovery very difficult unlesss a special program is used. Refer to our instructions for further information.
The security analysis reveals that it also creates a network connection to a remote hacker-controlled server. As a result the criminals can spy on the victims in real time, as well as take over control of the victim machines. This Trojan-like behavior can also be used to spread additional malware to the compromised machines.
The XTBL virus is known to cause dangerous modifications to the installed web browsers similar to browser hijackers. They are made compatible with the most popular web applications: Mozilla Firefox, Google Chrome, Safari, Opera, Microsoft Edge and Internet Explorer and their goal is to redirect the users to a hacker-controlled page. This is done by changing the default settings: new tabs page, search engine and home page.
The ransomware component is started once all prerequisite steps have been taken. It uses a strong cipher in order to target sensitive user data:
- Archives
- Documents
- Music
- Videos
- Photos
- Backups
- Databases
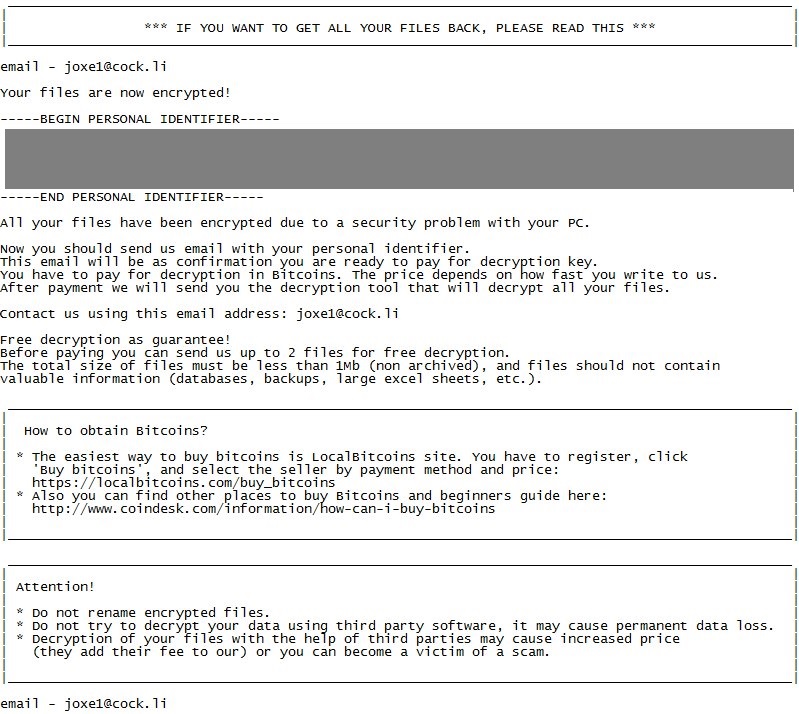
The encrypted files are renamed wit the .xtbl extension. A ransomware note is crafted in a file called IF YOU WANT TO GET ALL YOUR FILES BACK, PLEASE READ THIS.TXT. It reads the following:
*** IF YOU WANT TO GET ALL YOUR FILES BACK, PLEASE READ THIS ***
email – [email protected]
Your files are now encrypted!
—–BEGIN PERSONAL IDENTIFIER—–
XXXXXXXXXXXXXXXXXXXXXXXXX
XXXXXXXXXXXXXXXXXXXXXXxXX
XXXXXXXXXXXXXXXXXXXXXXXXX—–END PERSONAL IDENTIFIER——
All your files have been encrypted due to a security problem with your PC.
Now you should send us email with your personal identifier.
This email will be as confirmation you are ready to pay for decryption key.
You have to pay for decryption in Bitcoins. The price depends on how fast you write to us.
After payment we will send you the decryption tool that will decrypt all your files.Contact us using this email address: [email protected]
Free decryption as guarantee!
Before paying you can send us up to 3 files for free decryption.
The total size of files must be less than 1Mb (non archived), and files should not contain
valuable information (databases, backups, large excel sheets, etc.).Howto obtain bitcoins?
* The easiest way to buy bitcoins is Localbitcoins site. You have to register, click
‘Buy bitcoins’, and select the seller by payment method and price:
https://localbitcoins.com/buy_bitcoins
* Also you can find other places to buy Bitcoins and beinners guide here:
http://www.coindesk.com/information/how-can-i-buy-bitcoinsAttention!
* Do not rename encrypted files.
* Do not try to decrypt your data using third party software, it may cause permament data loss.
* Decryption of your files with the help of third parties may cause increased price
(they add their fee to our) or you can become a victim of a scam.email – [email protected]
Remove XTBL Ransomware Virus and Restore PC
Please note that paying the requested ransom fee to cyber criminals does not really solve your problem with XTBL crypto virus. In fact, you only encourage hackers to continue spreading ransomware of this kind. Instead, you must remove the threat immediately, and only then look for optional ways to recover your data.
WARNING! Manual removal of XTBL ransomware virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
DOWNLOAD Anti-Malware ToolXTBL Ransomware Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps below are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover XTBL- Files
WARNING! All files and objects associated with XTBL ransomware virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



