An infection with the dangerous .RansomMine virus leads to serious security issues. Victims can restore and protect their computers by following our complete removal guide.
Remove .RansomMine virus and Restore PC
Manual Removal Guide
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Distribution of .RansomMine virus
The .RansomMine virus is a new virus which has been sighted in a limited attack campaign. At the moment the security researchers cannot determine the primary infection strategy. We presume that the most widely used tactics are going to be employed.
Among them are the email messages created in an automated way and sent to large lists of potential victims. The .RansomMine virus can be directly attached to the messages. This is one of the easiest way for the criminals to attempt the infection. However a lot of email hosting providers usually capture the signatures of the virus and as such discard such messages or label them as dangerous or spam. Other infection methods related to this one is the option of inserting hyperlinks in the body content of the messages. The links are usually labeled as leading to a familiar website or a file of user interest. Redirects can redirect to hacker-controlled sites, infected payloads or other instances that can lead to an .RansomMine virus infection.
The computer criminals behind the malware can create malicious sites or download portals which distribute malware of different kinds, including the .RansomMine virus. A popular option is the use of infected documents which may be of different types ‒ spreadsheets, rich text documents, presentations and databases. They are modified to initiate the virus once the built-in scripts are run. Usually when the files are opened a notification will ask the users to run the macros (scripts). If this is done the infection follows.
The hacker-controlled sites are specialist portals that have been created either manually or automatically by the criminals behind the .RansomMine virus. They can either directly distribute the threat by initiating various scripts or automated operations or link to such instances. Redirects are usually caused by email interaction, ad networks or other browsing activity. However one of the main sources is the availability of browser hijackers. They are malicious addons made for the most popular web browsers ‒ Mozilla Firefox, Google Chrome, Internet Explorer, Opera, Microsoft Edge and Safari. Once installed they not only infect the users with the malware, but also redirect the victims to a hacker-controlled site. Depending on the configuration the browser hijackers can also steal sensitive information such as any stored passwords, account credentials, history, bookmarks, form data and settings.
Impact of .RansomMine virus
A new Hidden Tear based ransomware has been spotted known under the name of .RansomMine virus. As a derivative of the famous malware family it follows the same behavior patterns as its origins. The initial security analysis detectes that it includes only the base infection module at the moment. Furthermore no information is available of the hackers identity — it may either be a criminal collective or a malicious criminal.
Once it infects the target computers the ransomware process is immediately launched. However the security researchers note that it can be updated further with other modules as well.
The .RansomMine virus can be updated with the additions such as a Trojan module which gives the operators the ability to spy on the victims in real time. Advanced versions of the instances allow the malware operators to record the victim’s keystrokes and mouse movement, as well as take over control of the machine at any time.
Hidden Tear variants like the .RansomMine virus are popular for delivering additional threats as well. Such scenarios effectively transform the infection into an efficient two-stage delivery device. The first would be to deploy the .RansomMine virus, make necessary system changes and then install the secondary virus. Any configuration changes made by the infection engine can cause a persistent installation. Such measures effectively monitor the users actions and counter any manual removal attempts.
When all prerequisite steps have been taken the encryption phase is initiated. Like other related strains the .RansomMine virus uses a built-in list of target file type extensions. Other Hidden Tear strains tend to target the most commonly used data: archives, documents, images, music, videos, databases and configuration files. All processed files are renamed with the .RansomMine extension.
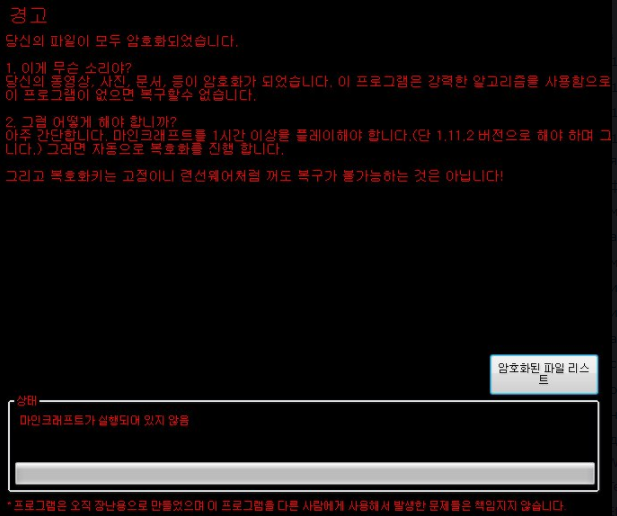
To blackmail the users a ransomware lockscreen is instituted on the victim computers. It effectively blocks all computer interaction until the virus is completely removed. This particular strain bundles a ransomware note in Korean which reads the following:
경고
답스외 파일이 모두 암호화되었습니다.
1. 이게 무슨 소리야?
당신외 동영상, 사진, 문서, 등이 암호화가 되었습니다. 이 프로그램은 갑력한 알고리즘을 사용함으로 이 프로그램이 없으면 복구할수 없습니다.
2. 그럼 어떻게 히I야합니까?
아주간단합니다. 마인크래프트를 1시간이상욺 플레이해야합니다.(단 1.11.2버전으로해야하며 그니다.) 그러면 자동으로 복호화틀 진 합니다.
그리고 목호화키는 고정이니 련선웨어처럼 꺼도 복구가 8가능하는 것은 아닙니다!
[암호화된 파일 리스르] -상타l-
마인크래프트가 실행도이 있지 않음
—
‘프로그은오직 장난용으로만뚤었으며 이 프로그임을다른사&01게 사용체서 발생한문제들은책임지지 않
A machine-translated version reads the following:
warning
Answer All external files are encrypted.
1. What is this?
Your videos, photos, documents, etc. have been encrypted. This program uses a violent algorithm and can not be recovered without this program.
2. How then do I?
It is very simple. You must play Minecraft for at least 1 hour (but only version 1.11.2) and it will automatically decode.
And the neck key is fixed, but it does not mean that it can be recovered even if it is turned off like a hardware warship!
[Encrypted file lease] -Santa l-
MineCraft does not run
—
‘The program is only for jokes and is not responsible for any problems that occur with other programs.
We recommend that all users abstain from communicating with the hackers and use our full .RansomMine virus removal guide below to recover their data and delete the active infections.
Remove .RansomMine virus and Restore PC
WARNING! Manual removal of the .RansomMine virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
.RansomMine virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Remove .RansomMine from Windows
Here’s a way to remove the program. This method will work regardless if you’re on Windows 10, 8, 7, Vista or XP. Simply selecting the program and pressing delete won’t work, as it’ll leave a lot of small files. That’s bad because these leftovers can linger on and cause all sorts of problems. The best way to delete a program is to uninstall it. Here’s how you can do that:
1. Hold the “Windows” button (It’s between CTRL and Alt on most keyboards) and press “R”. You’ll see a pop-up window.

2. In the textbox, type “appwiz.cpl”, then press“ Enter ”.

3. The “Programs and features” menu should now appear. It’s a list of all the programs installed on the PC. Here you can find the program, select it, and press “Uninstall“.

Remove .RansomMine Virus From Your Browser
Before resetting your browser’s settings, you should know that this action will wipe out all your recorded usernames, passwords, and other types of data. Make sure to save them in some way.
-
1. Start Mozilla Firefox. In the upper right corner, click on the Open menu icon and select “Add-ons“.

2. Inside the Add-ons Manager select “Extensions“. Search the list of extensions for suspicious entries. If you find any, select them and click “Remove“.

3. Click again on the Open menu icon, then click “Options“.

4. In the Options window, under “General” tab, click “Restore to Default“.

5. Select “Search” in the left menu, mark the unknown search engine and press “Remove”.

-
1. Start Google Chrome. On the upper-right corner, there a “Customize and Control” menu icon. Click on it, then click on “Settings“.

2. Click “Extensions” in the left menu. Then click on the trash bin icon to remove the suspicious extension.

3. Again in the left menu, under Chrome, Click on “Settings“. Go under “On Startup” and set a new page.

4. Afterward, scroll down to “Search“, click on “Manage search engines“.

5. In the default search settings list, find the unknown search engine and click on “X“. Then select your search engine of choice and click “Make default“. When you are ready click “Done” button in the right bottom corner.

2. In the “Manage add-ons” window, bellow “Add-on Types“, select “Toolbars and Extensions“. If you see a suspicious toolbar, select it and click “Remove“.

3. Then again in the “Manage Add-ons” window, in “Add-on Types“, Select “Search Providers“. Chose a search engine and click “Set as default“. Select the unknown search engine and click “Remove and Close”.

4. Open the Tools menu, select “Internet Options”.

5. In the “General” tab, in “Home page”, enter your preferred page. Click “Apply” and “OK”.

Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help



