The Random6 virus is a ransomware that renames victim files and it can be easily eliminated by reading our complete recovery guide.
Manual Removal Guide
Recover Random6 Virus Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How Does Random6 Virus Infiltrate the System?
There are only a limited set of captured malware samples and so far only an attack originating from Malaysia has been suspected as a main method.
The infections can be made using different methods. One of them involves the use of social engineering tricks in email messages. The hackers can use templates to make counterfeit emails to a large number of potential victims. They utilize text and graphics that resemble well-known companies and thereby confusing the users into falling for the trap. The Random6 virus can be either attached to the message directly or linked in the body contents.
It can also be delivered through payloads. They are usually infected documents (rich text documents, spreadsheets and etc.) or software installers. The developers modify the original applications code and insert the virus code into popular free or trial versions of software. They are then distributed on hacker-controlled download sites and P2P networks, especially BitTorrent trackers.
Browser hijackers can also result in an active Random6 ransomware infection. They are dangerous add-ons made for the most popular web browsers: Safari, Mozilla Firefox, Microsoft Edge, Opera, Internet Explorer and Google Chrome. Once they are installed important settings are modified including the default home page, new tabs page and search engine. They redirect the users to a hacker-specified site where the virus samples can be found. In addition they threaten the privacy of the victims by extracting sensitive data that is transferred over to the criminals: browser history, cookies, bookmarks, settings, passwords and account credentials.
Other forms of web redirects can also lead to a virus infection: malicious ad networks, scripts and etc. In some cases automated attacks are also possible.
Related: Karo Virus, CryptoDark Virus
Infection Flow of Random6 Virus
The Random6 virus is a newly discovered ransomware that is made by an unknown developer. Our research shows that it does not contain any code derived from the famous malware families or their offspring. The identity of the developers behind it is not known at the moment. We presume that it is an independent hacker or a criminal collective.
The Random6 ransomware at the moment contains only a basic encryption engine that is started automatically after the infection has been made. Like other similar viruses it uses a predefined list of target file type extensions. Random6 virus follows the tradition of targeting the most popular ones: documents, archives, backups, music, photos, videos and etc. When this process is complete a randomly-generated six-character string is appended to each affected file.
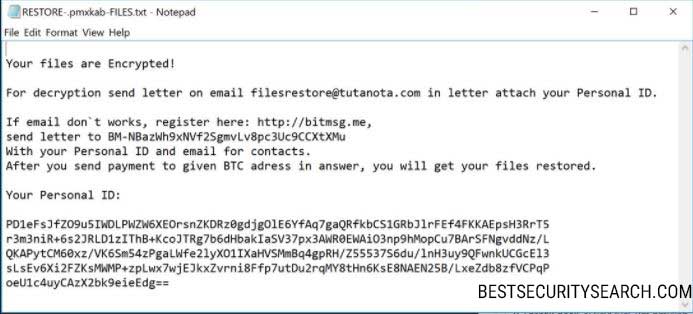
The Random6 virus engine then crafts a ransomware note based on a predefined template: “RESTORE-{6-character random extension}-FILES.txt”. It reads the following message:
Your Files are Encrypted!
For decryption send letter on email [email protected] in letter attach your Personal ID.
If email don’t works, register here: http://bitmsg.me,
send letter to BM-NBazWh9xNVf2SgmvL8pc3Uc9CCxtXMu
With your Personal ID and email for contacts.
After you send payment to given BTC adress in answer, you will get your files restored.Your Personal ID:
PD1eFsJfZO9u5IWDLPWZ6XEOrsnZKDRz0gdjgO1E6YfAq7gaQRfkbCS1GRbJ1rFEf4FKKAEpsH3RrT5
r3m3niR+6s2JRLD1zIThB+KcoJTRg7b6dHbaIaSV37px3AWR0EWAiO3np9hMopCU7BArSFNgvddNz/L
QKAPytCM60xz/VK6Sm54zPgaLWfe21yXO1IXaHVSMmBq4gpRH/Z55537S6du/1nH3uy9QFwnkUCGcE13
sLsEv6Xi2FZKsMWMP+zpLwx7wjEJkxZvrni8Ffp7utDu2rqMY8tHn6KsE8NAEN25B/LxeZdb8zfVCPqP
oeU1c4uyCazX2bk9eieEdg==
The hackers behind the Random6 virus do not specify a fixed sum in their note. The victims are instructed to contact via email. The contact address may be used by the criminals as a redirect for further privacy considerations.
This is widely used tactic that allows the criminals to blackmail the victims into paying them a fee that is adjusted based on the quality and quantity of the compromised data.
We suspect that the initial malware samples associated with the Random6 virus can be updated in upcoming larger attacks. The newer iterations can include added functionality such as:
- A Trojan component that can provide the hackers with the means of remote controlling the infected computers in real time.
- A file downloader that would allow the criminals to steal arbitrary files of their choice using the Random6 virus.
- An updated version of the Random6 virus can be used to deliver additional malware to the infected computers.
Victims can recover their computers by using a quality ant-spyware solution to remove the infections. Data can be restored by utilizing the professional-grade data recovery software listed in our instructions below.
Remove Random6 Virus and Restore Data
WARNING! Manual removal of Random6 Virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Random6 Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover Random6 Virus Files
WARNING! All files and objects associated with Random6 Virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
DOWNLOAD Random6 Virus Removal ToolSpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



