Computer criminals have devised a new threat known as the Cerberos ransomware which can be removed by reading our in-depth guide.
Cerberos Ransomware Description
The hackers behind the infamous Cyber SpLiTTer Vbs ransomware have created a new custom malware threat. It is known as the Cerberos ransomware and it is based on their previous attempt. Fortunately it is not related to the Cerber family, even though it has a similar name.
The virus employs the typical infection strategy like most other ransomware. The initial security analysis has not identified any complex modules or other features that make it stand out from the most basic virus iterations. It is possible that the initial version is just a basis on which further evolved versions might come up.
Upon infection it follows the standard procedures that are attributed to such basic threats. The ransomware uses a built-in list of predefined file type extensions. At the moment we have still not acquired a copy of it, however we presume that it uses a similar list. The engine uses a strong cipher to target the most commonly used user data: documents, music, photos, archives, configuration files, backups and etc.
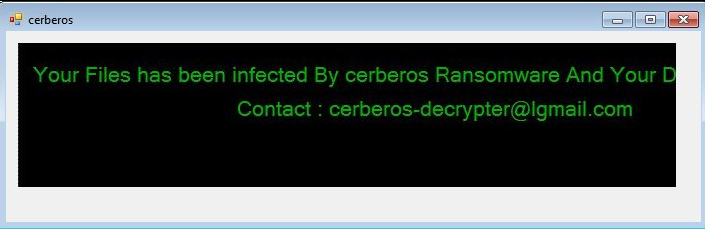
When this process is complete the ransomware note is displayed to the user in an application window titled “cerberos”. It contains the following message:
Your Files has been infected By cerberos Ransomware And Your Data has been crypted
Contact: [email protected]
The familiar extortionist tactic of not specifying a fixed ransomware sum is employed in this iteration. This is a trick of further pressuring the victims into paying a fee that is adjusted by the hackers depending on the “sensitivity” of the compromised data.
Having this in mind we expect to see evolved versions of it soon that include screenlockers or other modules. Possible upgrades can counter the effects of some of the traditional anti-virus solutions by using stealth protection techniques and persistent environments.
Cerberos Ransomware Distribution
The identified malware samples are fairy small and from the limited amount of available data we suspect that the attacks have been made to test the basic features of the Cerberos ransomware. The virus strain itself is placed in a double extensions file which poses as a PDF document.
Probably the most common strategy is the use of infected spam email messages. The operators use various tricks into making the users think that the messages originate from a trusted individual, famous company or a government institution. There are several different ways an infection can be triggered – hyperlinks that lead to the virus download hosted on a third-party server, directly attaching the file or making the user interact with an infected document. The last strategy has been a favorite of the hackers in the past few months as they embed dangerous macros. Upon interaction with them the Cerberos ransomware is installed to the host machine. Depending on the complexity of the script it may even subvert some of the running security solutions.
Hacked or hacker-controlled download sites are another popular source of all types of malware. The Cerberos ransomware can be found on portals, redirects, ad networks and P2P networks like BitTorrent. Dangerous browser extensions, also known as hijackers can distribute it as well. Upon installation they change the default home page, default search engine and new tabs page to redirect to hacker-controlled sites where the threat can be contacted.
Direct hacker attacks performed either manually or through the use of exploit kits can lead to a Cerberos ransomware infection. If used in conjunction with other viruses it can be installed on a victim machine as a secondary payload.
Summary of Cerberos Ransomware
| Name |
Cerberos Ransomware |
| File Extensions |
N/A |
| Ransom |
Varies |
| Easy Solution |
You can skip all steps and remove Cerberos Ransomware ransomware with the help of an anti-malware tool. |
|
Manual Solution |
Cerberos Ransomware ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Spam Email Campaigns, malicious ads & etc. |
Cerberos Ransomware Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely Cerberos Ransomware Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Cerberos Files
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How To Restore Cerberos Files
- 1) Use present backups
- 2) Use professional data recovery software
-
– Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



