ArmaLocky ransomware virus imitates the infamous Locky ransomware. It takes control of valuable files stored on the infected PC and extorts ransom payment from victims. Hackers use a ransom note stored in an html file to communicate with infected users. Keep reading to find more information about the threat so you can easily remove it and recover .armadilo1 files.
Manual Removal Guide
Recover .armadilo1 Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
ArmaLocky Ransomware – Delivery Details
ArmaLocky ransomware is distributed in a single binary executable file that can be spread using different methods depending on the targets and the required scale:
- Spam email messages that carry out the malicious file in an attachment or promote a web link that navigates to corrupted web page set to download and install the ransomware automatically
- Fake notifications of software updates
- Hacked or hacker-controlled download sites and popular P2P networks like BitTorrent
- Installation set ups of free software that mimic legitimate applications
Infection Flow of ArmaLocky Ransomware
Once the ArmaLocky ransomware payload is running on the computer it starts the encryption engine automatically. The virus encrypts predefined list of target file type extensions using the AES cipher and then renames the files with .armadilo1 extension. The list can be customized according to the targets or individual networks. Similar malware like Locky’s imitator ArmaLocky usually attempt to corrupt as many different frequently used files as possible: documents, archives, databases, backups, text files, configuration files, music, photos, videos and etc. Furthermore, reports on some ArmaLocky ransomware samples reveal information about enforcement of various system modifications that grant the threat an administrator rights. Thus being able to write commands in the Command Prompt ArmaLocky uses the command vssadmin.exe delete shadows /all /Quiet and makes file recovery more difficult. This command helps the ransomware to delete all Shadow Volume copies stored by the OS. These files may serve as a backup option and that’s why ransomware authors set the virus to eliminate this option.
Once the attack is near its end ArmaLocky drops its crafted ransom note in a ” _Locky_HELP_.html” file that contains the following message:
!!! IMPORTANT INFORMATION !!!
All of your files are encrypted with RSA-4096 and AES-256 ciphers.
More information about the RSA and AES can be found here:
https://en.wikipedia.org/wiki/RSA_(cryptosystem)
https://en.wikipedia.org/wiki/Advanced_Encryption_Standard
Decrypting of your files is only possible with the private key and decrypt program, winch is on our secret server.
The sever will destroy the key within 72 hours after encryption completed. After that, nobody and never will be able to restore files.
To receive your private key follow these steps:
1. Download and install Tor Browser: https://www.torproject.org/download/download-easy.html.en
2. After a successful installation, run the browser and wait for initialization.
3. Type in the address bar: ***
4. Follow the instructions on the site.
!!! Your personal identification ID: !!!
zip password: Lky1234
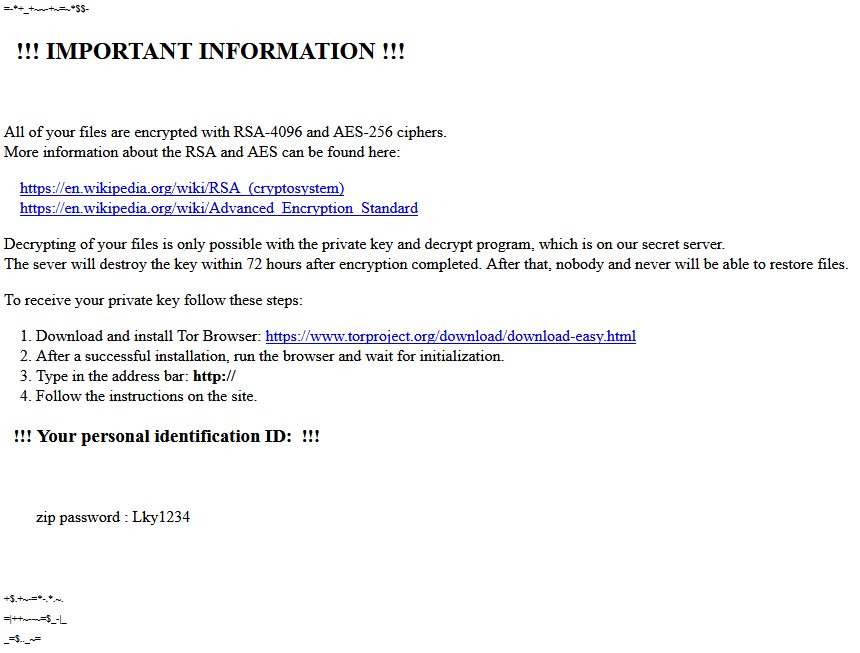
The ransom note resembles the one presented by Locky as it informs victims that RSA-4096 and AES-256 encryption was used to encode the files. However, security researchers who have investigated Armaocky samples believe that the ransomware is using only AES cipher for file encoding. Victims are expected to download the Tor browser and access a specific site to pay the ransom which should be in bitcoins. However, anyone who is infected with that ransomware is advised to proceed with ransomware removal and avoid ransom payment. The good news is some alternative data recovery approaches that may help for .armadilo1 files recovery and hopefully security researchers will be able to crack the code so they can release a freely available decryption tool soon.
Remove ArmaLocky Ransomware Virus and Restore Data
WARNING! Manual removal of ArmaLocky ransomware virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
ArmaLocky Ransomware Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover .armadilo1 Files
WARNING! All files and objects associated with ArmaLocky ransomware virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
DOWNLOAD ArmaLocky Removal ToolSpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



