A new iteration of the Cerber malware family known as the _README_{RAND}_ Cerber Ransomware has just been identified by malware researchers. Read our removal guide for further information.
| Name |
_README_{RAND}_ Cerber |
| File Extensions |
Randomly generated |
| Ransom |
Varies |
| Easy Solution |
You can skip all steps and remove _README_{RAND}_ Cerber ransomware with the help of an anti-malware tool. |
|
Manual Solution |
_README_{RAND}_ Cerber ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Spam email campaigns, malicious ads & etc. |
_README_{RAND}_ Cerber Ransomware Ransomware Description
Security researchers have identified a new Cerber malware family strain known as the _README_{RAND}_ Cerber Ransomware. This is a dangerous new ransomware that is currently under an active investigation.
Fortunately we have access to some of the technical details about the virus. Upon infection the ransomware uses a strong 523-bit cipher and encrypts the following file types:
.123, .1cd, .3dm, .3ds, .3fr, .3g2, .3gp, .3pr, .602, .7z, .7zip, .aac, .ab4, .abd, .acc, .accdb, .accde, .accdr, .accdt, .ach, .acr, .act, .adb, .adp, .ads, .aes, .agdl, .ai, .aiff, .ait, .al, .aoi, .apj, .apk, .arc, .arw, .ascx, .asx, .asm, .asp, .atb, .avi, .awg, .back, .backup, .backupdb, .bak, .bank, .bat, .bay,. bdb, .bgt, .bik, .bin, .bkp, .blend, .bmp, .bpw, .brd, .bsa, .bz2, .c, .cash, .cdb, .cdf, .cdr, .cdr3, .cd4, .cd5, .cd6, .cdrw, .cdx, .cel, .cel2, .cer, .cfg, .cgm, .cib, .class, .cls, .cmd, .cmt, .config, .cotact, .cpi, .cpp, .cr2, .craw, .crt, .crw, .cry, .cs, .csh, .csl, .csr, .css, .csv, .d3dbsp, .dac, .das, .dat, .db, .db3, .db_journal, .dbf, .dbx, .dc2, .dch, .dcr, .dcs, .ddd, .ddoc, .ddrw, .dds, .def, .des, .design, .dgc, .dgn, .dif, .dip, .dit, .djv, .djvu, .dng, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .drf, .drw, .dtd, .dwg, .dxb, .dxf, .dxg, .edb, .eml, .eps, .erbsql, .erf, .exf, .fdb, .ffd, .fff, .fh, .fhd, .fla, .flac, .flb, .flf, .flv, .forge, .fpx, .frm, .fxg, .gbr, .gho, .gif, .gpg, .gray, .grey, .groups, .gry, .gz, .h, .hbk, .hpp, .html, .hwp, .ibank, .ibd, .ibz, .idx, .iif, .iiq, .incpas, .indd, .info, .info_, .iwi, .jar, .java, .jnt, .jpe, .jpeg, .jpg, .js, .json, .k2p, .kc2, .kdbx, .kdc, .key, .kpdx, .kwm, .laccdb, .lay, .la6, .lbf, .lck, .ldf, .lit, .litemod, .litesql, .lock, ltx, .lua, .m, .m2ts, .m3u, .m4a, .m4p, .m4u, .m4v, .ma, .mab, .mapimail, .max, .mbx, .md, .mdb, .mdc, .mdf, .mef, .mfw, .mid, .mkv, .mlb, .mml, .mmw, .mny, .money, .moneywell, .mos, .mov, .mp3, .mp4, .mpeg, .mpg, .mrw, .ms11, .msf, .msg, .mts, .myd, .myi, .nd, .ndd, .ndf, .nef, .nk2, .nop, .nrw, .ns2, .ns3, .ns4, .nsd, .nsf, .nsg, .nshm, .nvram, .nwb, .nx2, .nx1, .nyf, .oab, .obj, .odb, .odc, .odf, .odg, .odm, .odp, .ods, .odt, .ogg, .oil, .omg, .one, .onenotec2, .orf, .ost, .otg, .oth, .otp, .otsm, .ott, .p12, .p7b, .p7c, .pab, .pages, .paq, .pas, .pat, .pbf, .pcd, .pct, .pdb, .pdd, .pdf, .pef, .pem, .pfx, .php, .pif, .pl, .plc, .plus_muhd, .pm, .pm!, .pmi, .pmj, .pmi, .pmm, .pmo, .pmr, .pnc, .pnd,.png, .pnx, .pot, .potm, .potx, .ppam, .pps, .ppsm, .ppt, .pptm, .pptx, .prf, .private, .ps, .psafe3, .ppsd, .pspimage, .pst, .ptx, .pub, .pwm, .py, .qba, .qbb, .qbm, .qbr, .qbw, .qbx, .qbx, .qby, .qcow, .qcow2, .qed, .qtb, .r3d, .raf, .rar, .rat, .raw, .rb, .rdb, .re4, .rm, .rtf, .rvt, .rw2, .rwl, .rwz, .s3db, .safe, .sas7bdat, .sav, .save, .say, .sch, .sd0, .sda, .sdb, .sbf, .secret, .sh, .sldm, .sldx, .slk, .slm, .sql ,.sqlite, .sqlite-shm, .sqlite-wal, .sqlite3, .sqlitedb, .sr2, .srb, .srf, .srs, .srt, .srw, .st4, .st5, .st6, .st7, .st8, .stc, .std, .sti, .stl, .stm, .stw, .stx, .svg, .swf, .sxc, .sxd, .sxg, .sxi, .sxm, .tar, .tax, .tbb, .tbk, .tbn, .tex, .tga, .tgz, .thm, .tif, .tiff, .tlg, .tlx, .txt, .uop, .opk, .usr, .vb, .vbox, .vbs, .vdi, .vhd, .vhdx, .vmdk, .vmsd, .vmx, .vmxf, .vob, .vpd, .vsd, .wab, .wallet, .war, .wav, .wb2, .wk1, .war, .wav, .wb2, .vk1, .wks, .wma, .wmf, .wmv, .wpd, .wps, .x11, .x3f, .xis, .xla, .xlam, .xlc , .xlk, .xlm, .xlr, .xls, .xlsb, .xlsm, .slt, .xltm, .xlw, .xml, .xps,
.xxx, .ycbcra, .uiv, .zip
The virus developers have used a global public key in the encryption module. The popular Cerber malware family uses the .hta extension with an unique ID code appended to the affected files.
Like other related threats it communicates with several remote malicious C&C servers. The captured strains were found to communicate with these addresses:
- 15.49.2.0/27
- 122.1.13.0/27
- 194.165.16.0/23
The connection to the remote servers is carried out via a network handshake carried out over port 6892 which is associated with the BitTorrent and Windows Live Messenger services.
The virus gathers important system information and sends it along with the private key used for decryption to the criminal operators of the ransomware.
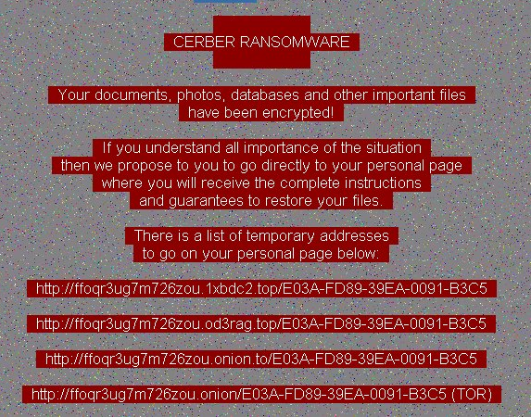
The ransomware note reads the following:
CERBER RANSOMWARE
Your documents, photos, databases and other important filesh have been encrypted! If you understand all importance of the situation then we propose to you to go directly to your personal page where you will receive the complete instructions and guarantees to restore your files. There is a list of temporary addresses to go on your personal page below:
http://{TOR}.{SITE_1}/{PC_ID}
http://{TOR}.{SITE_2}/{PC_ID}
http://{TOR}.{SITE_3}/{PC_ID}
http://{TOR}.onion/{PC_ID} (TOR)”
The ransomware also plays an audio record of the message.
Depending on the infected strain the TOR payment gateways may be different.
The _README_{RAND}_ Cerber Ransomware also works features a white list of folders and locations:
- \\documents and settings\\all users\\documents\\
- \\appdata\\roaming\\microsoft\\office\\
- \\excel\
- \\microsoft sql server\\
- \\onenote\\
- \\outlook\\
- \\powerpoint\\
- \\steam\\
- \\the bat!\\
- \\thunderbird\\
The blacklist of target files include the following:
- bootsect.bak
- iconcache.db
- ntuser.dat
- thumbs.db
- :\\$recycle.bin\\
- :\\$windows.~bt\\
- :\\boot\\
- :\\documents and settings\\all users\\
- :\\documents and settings\\default user\\
- :\\documents and settings\\localservice\\
- :\\documents and settings\\networkservice\\
- :\\program files\\
- :\\program files (x86)\\
- :\\programdata\\
- :\\recovery\\
- :\\recycler\\
- :\\users\\all users\\
- :\\windows\\
- :\\windows.old\\
- \\appdata\\local\\
- \\appdata\\locallow\\
- \\appdata\\roaming\\adobe\\flash player\\
- \\appData\\roaming\\apple computer\\safari\\
- \\appdata\\roaming\\ati\\
- \\appdata\\roaming\\intel\\
- \\appdata\\roaming\\intel corporation\\
- \\appdata\\roaming\\google\\
- \\appdata\\roaming\\macromedia\\flash player\\
- \\appdata\\roaming\\mozilla\\
- \\appdata\\roaming\\nvidia\\
- \\appdata\\roaming\\opera\\
- \\appdata\\roaming\\opera\\
- \\appdata\\roaming\\microsoft\\internet explorer\\
- \\appdata\\roaming\\microsoft\\windows\\
- \\application data\\microsoft\\
- \\local settings\\
- \\public\\music\\sample music\\
- \\public\\pictures\\sample pictures\\
- \\public\\videos\\sample videos\\
- \\tor browser\\
The following locale settings and languages are supported by the virus – Russian, Ukrainian, Belarusian, Tajik, Armenian, Azeri – Latin, Georgian, Kazakh, Kyrgyz – Cyrillic, Turkmen, Uzbek – Latin, Tatar, Romanian – Moldova, Russian – Moldova, Azeri – Cyrillic, Uzbek – Cyrillic.
If they are identified on the host computers then the virus proceeds to shut down all available database servers including the following:
- msftesql.exe
- sqlagent.exe
- sqlbrowser.exe
- sqlservr.exe
- sqlwriter.exe
- oracle.exe
- ocssd.exe
- dbsnmp.exe
- synctime.exe
- mydesktopqos.exe
- agntsvc.exeisqlplussvc.exe
- xfssvccon.exe
- mydesktopservice.exe
- ocautoupds.exe
- agntsvc.exeagntsvc.exe
- agntsvc.exeencsvc.exe
- firefoxconfig.exe
- tbirdconfig.exe
- ocomm.exe
- mysqld.exe
- mysqld-nt.exe
- mysqld-opt.exe
- dbeng50.exe
- sqbcoreservice.exe
_README_{RAND}_ Cerber Ransomware Distribution
Current _README_{RAND}_ Cerber Ransomware samples have identified as being distributed over the TOR anonymous network as svchost32.exe. Other methods of distribution include exploit kits (particularly RIG), malicious ads and infected software installation packages and updates.
How To Protect My PC From _README_{RAND}_ Cerber Virus
The Cerber family is very active, and if you got infected once, chances are that your computer will be targeted again. Here are a few tips on how you can prevent another infection:
- Don’t Open Spam Emails
- Don’t Download malicious email attachment, especially ZIP archives
- Never give your email to suspicious places like torrent or porn sites
Differentiation between a malicious link and a legit link can be very hard, especially if you’re a regular user. There are so many links, connections, and emails that pop-up in our inboxes daily, that it’s hard to make out the good from the bad. That’s why it’s best to have special malware protection.
Click here to download an anti-malware solution. This software will scan your system for free and pinpoint the exact location the virus.
_README_{RAND}_ Cerber Removal Guide
Manual removal of _README_{RAND}_ Cerber requires being familiar with system files and registries. Removal of any important data can lead to permanent system damage. You could prevent this troublesome effect and delete _README_{RAND}_ Cerber browser hijacker with SpyHunter malware removal tool.
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely _README_{RAND}_ Cerber Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Encrypted Files
-
1) Use present backups
2) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

STEP VII: Preventive Security Measures
-
1) Enable and properly configure your Firewall.
2) Install and maintain reliable anti-malware software.
3) Secure your web browser.
4) Check regularly for available software updates and apply them.
5) Disable macros in Office documents.
6) Use strong passwords.
7) Don’t open attachments or click on links unless you’re certain they’re safe.
8) Backup regularly your data.



