Security experts have detected a new type of security threat that is labeled as “video jacking” and it affects smart devices such as phones and tablets. The technique fools the users into hooking up their device to a fake USB charging port. The station is an eavesdropping machine that uses the connected cable to access the device’s display and record a video of the user interaction. A demonstration was presented at the annual DEF CON security conference in Las Vegas. Successful demonstrations were made with popular Android devices and the iPhone 6.
How Video Jacking works
A lot of Android users can fall victim to this attack if they do not distinguish between a typical charging station and a setup designed by malicious users. This can sometimes be really hard as custom electronics can be embedded in existing charging stations. The criminals devise a scenario where the connecting cable splits the phone’s display unit and records the user interaction.
Video Jacking is an extension to the “juice jacking” experiment carried out in 2011 in which user data was stolen via charging cables. The video jacking technique uses the HDMI and MHL embedded technologies that are available in most mid-range and high-end smartphones.
The problem with detecting video jacking malicious stations is that it is very difficult to distinguish a charging cable and a USB cable that carries the video signal. Android does not provide the users with a notification that the device’s video display is being cloned to another source.
Most devices that have these features turned on by default which leads to the successful exploitation of the issue. The researchers have noted that some of the tested devices produce a brief notification, but they are only a minor portion of the whole group.
Limited tests were produced on the latest Apple iPhone 6 where the security issues is also present.
How to Protect Yourself from Video Jacking
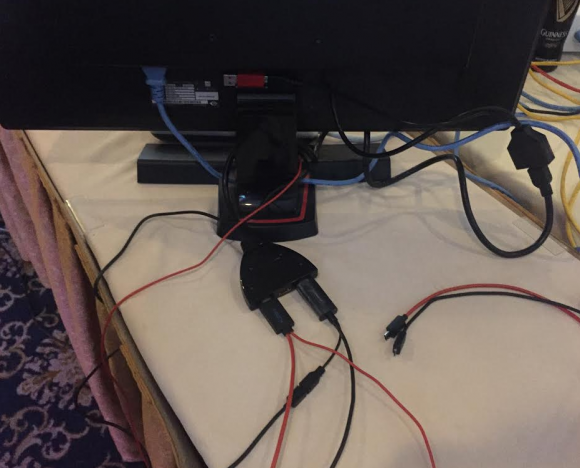
The demonstration at the DEF CON conference used cheap equipment available at every electronics store. A simple device pipes the video output to an HDMI splitter. The splitter connects to two micro USB ports. The cords are very similar to standard USB cables used for phone charging. The raw video files are then recorded on a small USB drive.
The proof of concept shows that this is an effective security threat that can be effectively used in places where a lot of places gather – airports, trade center, busy shops etc. Security experts advise the users to use their own charging cables when connecting to external power sources or carry mobile chargers.
To minimize the risks, device manufacturers can add a prompt notification when video output is being accessed.



