Turkish FileEncryptor Ransomware is a new malware threat which encrypts only a limited set of user data, read our complete removal guide.
Turkish FileEncryptor Ransomware Description
Malware researchers discovered a new ransomware strain made by an unknown hacker or entity. It is also known under the alias ofFileEncryptor and does not seem to originate from a known family of viruses. The initial analysis does not show if any advanced features are available. Possibilities include the following:
- Additional Malware Infection – Viruses like this one are frequently used as a second-stage of infection that deliver more complex strains. This ensures that at least one infection remains active if the victims attempt to remove the malware from the machine.
- Remote Control & File Manipulation – Evolved varints of the ransomware can be used to remote control them or modify (access, change, rename or delete) essential system and user files.
- Persistence Environment – The ransomware can create an environment which automatically starts the virus code at computer boot or modify core settings of the operating system to prevent manual removal.
- Stealth Protection Measures – The hackers can include various features which can defend against discovery and removal by anti-virus and security solutions. Such options utilize process and registry monitoring as well as continous file operations.
Upon infection the encryption engine is started which targets the following file type extensions:
.bmp, .docx, .ini, .jpg
They represent some of the most commonly used files:
- BMP – This is one of the most popular raster image file formats.
- DOCX – A primary format for distributing rich text documents.
- INIT – Used primarily as configuration files for operating systems and user applications.
- JPG – A popular compressed image file format.
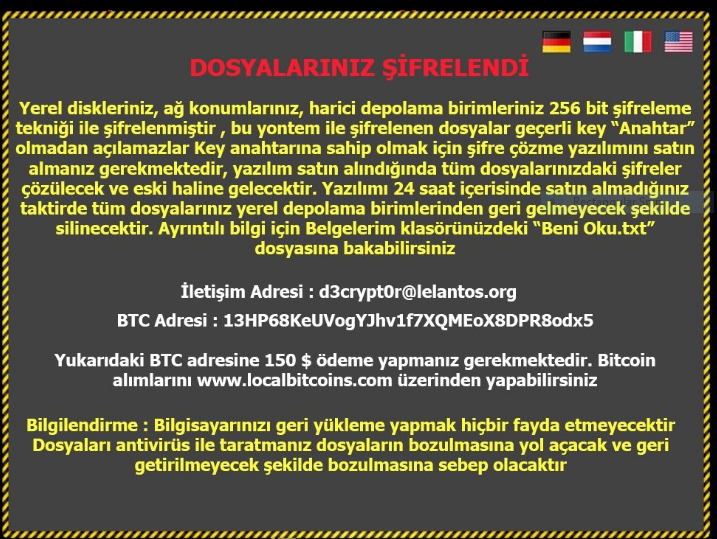
After the process is complete a ransomware note is crafted and shown to the user in the Turkish language. A machine-translated version if it in English reads the following:
LOCKED FILES
Your local disks, network locations, external storage 256-bit encryption
Encrypted with this method, the files encrypted with this method will be valid key “Key”
Purchase decryption software to have Key Key
You need to buy it, the passwords for all of your files when the software is purchased
It will be solved and it will become old. You did not purchase the software within 24 hours
If all your files will not come back from local storage
Will be deleted. For more information, see the “Read me.txt”
You can look at the file
Contact Address: [email protected]
BTC Address: 13HP68KeUVogYJhvlf7XQMEoX8DPR8odx5
You must pay $ 150 to the above BTC address. Bitcoin
You can make purchases through www.localbitcoins.com
Information: Restoring your computer will not help
Files with antivirus will lead to the corruption of your files and back
Will cause it to malfunction
To increase the infection ratio the hackers have enforced the use of a screenlocker which prohibits ordinary interaction with the computer until the virus is removed.
Turkish FileEncryptor Ransomware Distribution
The Turkish FileEncryptor Ransomware is primarily distributed as a malicious binary file. As the detected malware samples are small in number we do not have information about the preferred infection method. However as the ransomware note is written in Turkish we suspect that various popular sites and services used by Turkish-speaking users are a popular source of infections. The following methods are assumed:
- Download Sites, Portals & P2P Networks – Computer criminals frequently use hacker-controlled or compromised sites and portals to distribute the virus strains. As P2P networks are one of the primary download sources for a variety of content, the Turkish FileEncryptor Ransomware can also be found posing as legitimate software on BitTorrent trackers.
- Email Spam – Hackers utilize email messages which contain the virus as an attachment or link to infected files in the body of the message. There are different configurations, however one of the most popular ones employ infected Office documents that pose as being sent by a legitimate company or institution.
- Infected Software – The virus can be found in bundled software installers that pose as popular freeware and trial versions of well-known games, applications, utilities and patches.
Summary of the Turkish FileEncryptor Ransomware
| Name |
Turkish FileEncryptor Ransomware |
| File Extensions |
.encrypted |
| Ransom |
150 US Dollars |
| Easy Solution |
You can skip all steps and remove Turkish FileEncryptor Ransomware ransomware with the help of an anti-malware tool. |
|
Manual Solution |
Turkish FileEncryptor Ransomware ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Spam Email Campaigns, malicious ads & etc. |
Turkish FileEncryptor Ransomware Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely Turkish FileEncryptor Ransomware Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Turkish FileEncryptor Files
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How To Restore Turkish FileEncryptor Files
- 1) Use present backups
- 2) Use professional data recovery software
-
– Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



