Follow our complete removal guide to learn how to delete active infections of the TeamSpy virus which is targeting users worldwide in a new infection campaign.
The TeamSpy Virus Surfaced Again
Security specialists discovered that the infamous TeamSpy virus has surfaced once again in a new attack campaign. It was initially discovered in 2013 and rated as a potent information stealing Trojan. The fact that it integrates in itself the TeamViewer application makes it easily identifiable a quality anti-malware solution.
It uses the classic scheme of communication with a hacker-controlled C&C (command and control) server which is used to send commands to the infected hosts. It is also used to collect all kinds of data from the computers in an automated way. One of the major problems is that the TeamViewer application routes the traffic through its own VPN encrypted network. This makes it very difficult to detect infections using ordinary network analysis. The technique employed by the virus is DLL hijacking which tricks already installed applications into performing unauthorized actions. The hackers aim to gain full control of the host machines. The built-in module allows them to initiate surveillance at will as well as to infect the victims with additional malware.
TeamSpy Email Attack Campaign
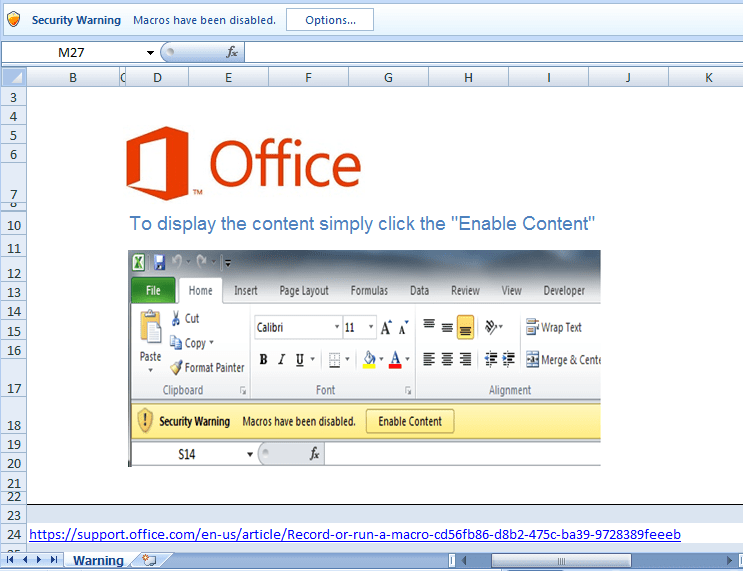
The attackers use various social engineering scams upon the targets. One of the primary methods is the use of email spam campaigns that are a clear example of a classic phishing attempt. The attackers attempt to lure the targets into infecting themselves by downloading or executing the virus.
The messages are made to look as being sent by a legitimate user, company or government institution. The ongoing campaign uses attachments – Office documents containing malicious scripts. When they are executed the virus payload is downloaded to the victim computers. The infection is carried out in the background. Some of the examples include counterfeit scanned documents, invoices or letters which attempt to capture the attention of the targets. Another option which has been identified is the use of infected software installers. They pose as authentic TeamViewer installation packages and are being distributed on hacker-controlled sites.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
TeamSpy Virus Capabilities
The virus engine includes the following options which are triggered when the installation has been initiated:
- The virus starts its payload installation process by launching a built-in BAT script.
- The virus checks if an active Internet connection is available.
- Several threads and tasks are killed to make sure that the virus is deployment without any problems.
- The malware is deployed to the system and additional components are dropped to various system folders.
- The remote C&C servers are contacted to report the infection.
The TeamSpy virus itself is made up of several modules – The VPN which routes all traffic through an encrypted channel, the payload preparation module which is responsible for the successful virus installation and the TeamViewer module which is used to remote control the infected hosts, as well as a keylogger part which can extract the keystrokes and user interaction of the users.
The TeamSpy Virus configuration file is stored in a tvr.cfg container. It is made up of several fields which contain important variables related to the encryption process, specifically the way the data is processed. Unlike other similar threats this malware uses a custom encryption algorithm that can be modified by the hacker operators at will.
Communication with the remote servers is done by transmitting strings associated with data according to a template system. The extracted information compromises of the following: Unique TeamViewer ID, timeout, idle time, operating system build and architecture, service pack version, TeamViewer client version, username, computer name, TeamViewer VPN status, detected anti-virus applications.
The hackers can use the TeamViewer application to connect to the hacked computers by using the unique IDs associated with each of them. Another option is to use short commands that allow for basic functions to be performed. Some of the including the following:
- Show the currently installed application.
- Initiate a Command Prompt.
- Shows the version of the TeamViewer Instance.
- Shows information about the operating system.
- Shows the VPN status information.
- Shows user-defined locale information.
- Time and Date Modification.
- Activates the webcam.
|
By using a quality anti-malware solution computer users can protect themselves from the TeamSpy Virus and remove active infections with a few mouse clicks. |
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



