Computer security experts discovered a new malware threat known as the Serpent ransomware, continue reading our removal guide to learn how to delete active infections.
Serpent Ransomware Description
The Serpent ransomware is a newly discovered malware threat which has just been reported by Proofpoint Security experts.
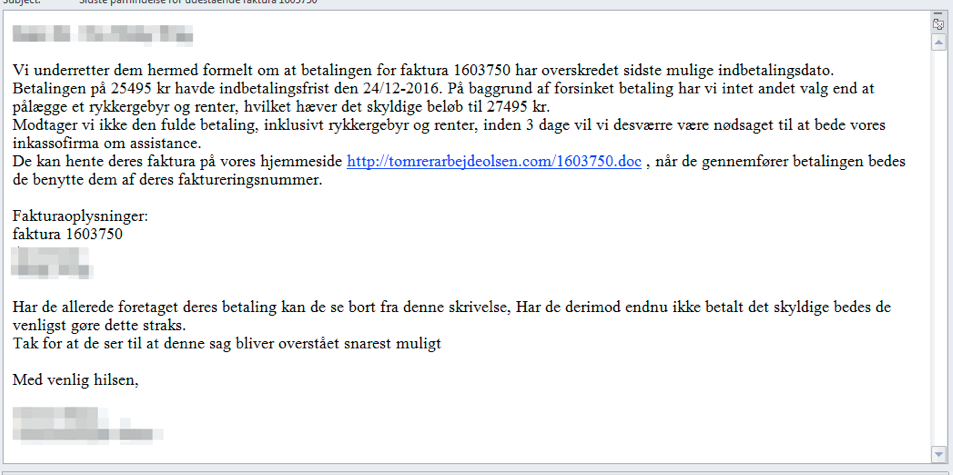
The Serpent ransomware is primarily distributed via spam email messages that contain malicious Microsoft Office documents. According to the experts it targets Danish-speaking users and the emails use the subject line “Sidste påmindelse for udestående faktura 1603750” which translates to “Last reminder for outstanding invoice 1603750”. The body of the messages contain a hyperlink which downloads a Microsoft Word document. As usual if the user interacts with the malicious embedded macro the ransomware is delivered.
The infection process starts afterwards. Once the macro is enabled the text is replaced with “FATAL ERROR”. The security researchers discovered that the virus engine executes several PowerShell commands.
- An executable is downloaded from a remote server and saved to the local machine as C:\Users\[user name]\AppData\Local\Temp\pyttyx86.exe.
- AN UAC bypass technique is employed which uses the eventvwr.exe system proess and a Windows Registry hack to run the Serpent ransomware with elevated privileges.
- An unique Hardware ID is used which follows a set pattern of “hwid=[A-F0-9]{8}-[A-F0-9]{8}-[A-F0-9]{8}-[A-F0-9]{8}”.
- The C&C servers supplies several variable which are used to generate the encryption key. In addition the Serpent ransomware does not begin encryption if the victim machine is not connected to the internet.
- Persistence is maintained by the addiition of a Windows registry key which runs the malware when the system boots.
- A mutually exclusive flag (MUTEX) is used to launch the malware process and exclude certain commands from executing while the encryption process is running.
- A remote connection the C&C servers is initiated to report of the infection.
The Ransomware targets the following file types and all affected data receive the .serpent extesion:
.2011,.2012,.2013,.2014,.2015,.2016,.2017,.7zip,.accd,.accdb,.accde,.accdr,.accdt,
.aepx,.agdl,.aiff,.aspx,.back,.backup,.backupdb,.bank,.blend,.btif,
.cdr3,.cdr4,.cdr5,.cdr6,.cdrw,.cfdi,.clas,.class,.cntk,.config,.craw,.db-journal,.db_journal,.ddoc,.ddrw,.defx,.design,.djvu,.docb,.docm,.docx,
.dotm,.dotx,.dtau,.efsl,.erbsql,.fcpa,.fcpr,.flac,.flvv,.gray,.grey,.groups,.html,
.iban,.ibank,.idml,.incpas,.indb,.indd,.indl,.indt,.int?,.intu,.java,.jpeg,.jsda,
.kdbx,.kpdx,.laccdb,.lay6,.m2ts,.m3u8,.mbsb,.meta,.mhtm,.mone,.moneywell,.mpeg,.ms11,
.myox,.nvram,.pages,.pcif,.php5,.phtml,.plus_muhd,.potm,.potx,.ppam,.ppsm,.ppsx,.pptm,.
pptx,.prel,.prpr,.psafe3,.pspimage,.ptdb,.qb20,.qbmb,.qbmd,.qcow,.qcow2,.qdfx,
.qmtf,.quic,.qwmo,.resx,.s3db,.safe,.sas7bdat,.save,.seam,.sldm,.sldx,.sqli,
.sqlite,.sqlitedb,.tax0,.tax1,.tax2,.text,.tiff,.tt10,.tt11,.tt12,.tt13,.tt14,
.tt15,.tt20,.vbox,.vbpf,.vhdx,.vmdk,.vmsd,.vmxf,.wallet,.xhtm,.xlam,.xlsb,.xlsb,3dm,
.xlsm,.xlsx,.xltm,.xltx,.ycbcra,.zipx
A ransomware is crated in the Documents, Desktop and Pictures folder in two formats – txt and html bearing the name “HOW_TO_DECRYPT_YOUR_FILES_[A-Za-z0-9]{3}” . They contain the following text:
==== NEED HELP WITH TRANSLATE? USE https://translate.google.com ====
================ PLEASE READ THIS MESSAGE CAREFULLY ================Your documents, photos, videos, databases and other important files have been encrypted!
The files have been encrypted using AES256 and RSA2048 encryption (unbreakable)To decrypt your files you need to buy the special software ‘Serpent Decrypter’.
You can buy this software on one of the websites below.http://vdpbkmwbnp[.]pw/00000000-00000000-00000000-00000000
http://hnxrvobhgm[.]pw/00000000-00000000-00000000-00000000If the websites above do not work you can use a special website on the TOR network. Follow the steps below
1. Download the TOR browser https://www.torproject.org/projects/torbrowser.html.en#downloads
2. Inside the TOR browser brower navigate to : 3o4kqe6khkfgx25g[.]onion/00000000-00000000-00000000-00000000
3. Follow the instructions to buy ‘Serpent Decrypter’================ PLEASE READ THIS MESSAGE CAREFULLY ================
Serpent Ransomware Distribution
The primary method of infection employed by the Serpent ransomware is through email spam messages. Other strategies include the following:
- Browser Hijackers – Installed browser hijackers can redirect the victim into downloading malware samples through various search queries or popup messages.
- Malicious Redirects – All kinds of dangerous redirects can lead to a Serpent ransomware infections. This includes all types of malicious ads and other similar content found on hacked or untrusted sites.
Serpent Ransomware – How To Remove it and Prevent It From Coming Back
There are two ways of removal:
- With an anti-malware tool – this will also help prevention
- Manually – using the instructions below
Summary of GC47 Ransomware
| Name |
Serpent Ransomware Ransomware |
| File Extension |
.serpent |
| Ransom |
0.75 BTC |
| Easy Solution |
You can skip all steps and remove Serpent Ransomware ransomware with the help of an anti-malware tool. |
| Manual Solution |
Serpent Ransomware ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Spam emails, malicious URLs, malicious attacments, exploit kits, freeware. |
Serpent Ransomware Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely Serpent Ransomware Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Encrypted Files
- 1) Use present backups
- 2) Use professional data recovery software
-
– Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
STEP VII: Preventive Security Measures
-
1) Enable and properly configure your Firewall.
2) Install and maintain reliable anti-malware software.
3) Secure your web browser.
4) Check regularly for available software updates and apply them.
5) Disable macros in Office documents.
6) Use strong passwords.
7) Don’t open attachments or click on links unless you’re certain they’re safe.
8) Backup regularly your data.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



