SadStory ransomware is a new malware threat which has a fully-functioning encryption engine which can be removed easily by following our complete guide.
SADStory Ransomware Description
Security specialists identified a new virus threat which has been dubbed as the SadStory ransomware. The initial security analysis shows that this is a dangerous strain which is descendant from the CRyPy family of viruses. Like other similar threats this one is written in the popular Python scripting language as it allows the hackers to create a modular base which can then be improved further.
The current iteration of the SadStory ransomware does not feature many built-in modules other than the encryption one. We suspect that the people behind it may opt to create evolved versions which might include dangerous improvements. These might include the development of a screenlocker version which can prohibit ordinary interaction with the computer unless the relevant unlock code is supplied.
Upon infection the virus starts the encryption engine which is programmed to target a predefined list of important user files which are processed through a strong algorithm of choice. At the moment the security analysists have not been able to extract the complete list of target user file extensions however we pressume that it includes the most commonly used videos, photos, music, documents, archives, databases and etc.
Some of the strains that are associated with the threat infect the following file type extensions:
txt, php, pl, 7z, rar, m4a, wma, avi, wmv, csv,
d3dbsp, sc2save, sie, sum, ibank, t13 t12, qdf, gdb, tax, pkpass,
bc6, bc7, bkp, qic, bkf, sidn, sidd, mddata, itl, itdb, icxs,
hvpl, hplg, hkdb, mdbackup, syncdb, gho, cas, svg, map, wmo, itm,
sb, fos, mcgame, vdf, ztmp, sis, sid, ncf, menu, layout, dmp,
rim, w3x, fsh, ntl, arch00, lvl, snx, cfr, ff, vpp_pc, lrf,
m2, mcmeta, vfs0, mpqge, kdb, db0, mp3, upx, rofl, hkx, bar,
upk, das, iwi, litemod, asset, forge, ltx, bsa, apk, re4, sav,
desc, py. m3u, flv, js, css, rb, png, jpeg, p7c, p7b, p12,
pfx, pem, crt, cer, der, x3f, srw, pef, ptx, r3d, rw2, rwl,
raw, raf, orf, nrw, mrwref, mef, erf, kdc, dcr, cr2, crw, bay,
sr2, srf, arw, 3fr, dng, jpeg, jpg, cdr, indd, ai, eps, pdf,
pdd, psd, dbfv, mdf, wb2, rtf, wpd, dxg, xf, dwg, pst, accdb,
mdb, pptm, pptx, ppt, xlk, xlsb, xlsm, xlsx, xls, wps, docm,
docx, doc, odb, odc, odm, odp, ods, odt, sql, zip, tar,
tar.gz, tgz, biz, ocx, html, htm, bat, 3gp, srt, cpp, mid,
mkv, mov, asf, mpeg, vob, mpg, fla, swf, wav, qcow2, vdi,
vmdk, vmx, gpg, aes, ARC, PAQ, tar.bz2, tbk, bak, djv, djvu,
bmp, cgm, tif, tiff, NEF, cmd, class, jar, java, asp, brd,
sc, dc, dip, vbs, asm, pas, ldf, ibd, myi, myd, frm, dbf,
SQLITEDB, SQLITE3, asc, lay6, lay, ms11 (Security copy), sldm ldx, ppsm,
ppsx, ppam, docb, mml, xm, tg, slk, xlw, slt, xlm, xlc, dif,
stc, sxc, ots, ods, hwp, dotm, dotx, docm, DOT, max, xml, uot,
stw, sxw, ott, csr, key, wallet.dat
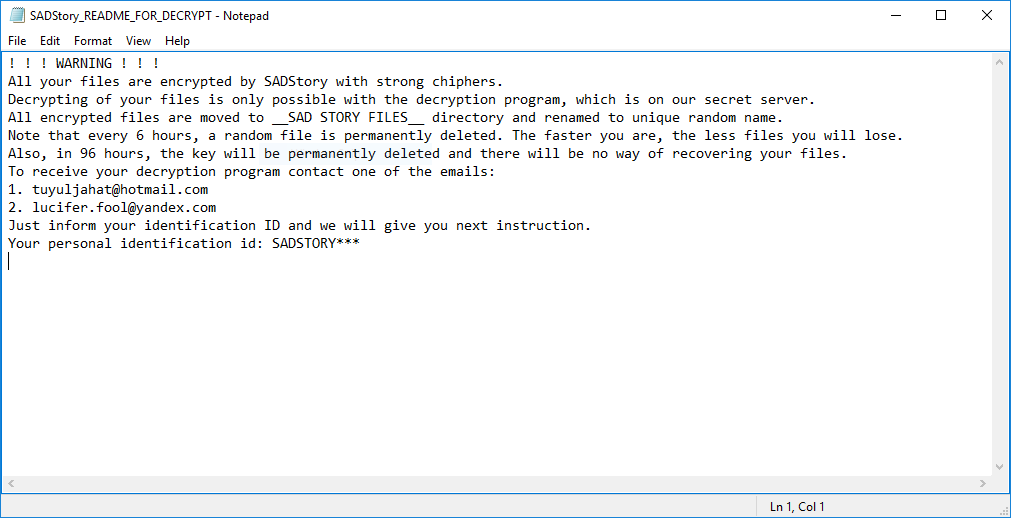
When this process is complete a ransomware note is created in a SADStory_README_FOR_DECRYPT.txt file which reads the following:
! ! ! WARNING ! ! !
All your files are encrypted by SADStory with strong chiphers.
Decrypting of your files is only possible with the decryption program, which is on our secret server.
All encrypted files are moved to __SAD STORY FILES__ directory and renamed to unique random name.
Note that every 6 hours, a random file is permanently deleted. The faster you are, the less files you will lose.
Also, in 96 hours, the key will be permanently deleted and there will be no way of recovering your files.
To receive your decryption program contact one of the emails:
1. [email protected]
2. [email protected]
Just inform your identification ID and we will give you next instruction.
Your personal identification id: SADSTORY***
All of the affected data are renamed using the .sad extension, consequently the hackers request a ransomware fee to delete the virus. The exact amount is not specified which is a popular extortion trick.
In addition the virus has been found to extract detailed information about the infected machine which is sent to the attackers during the network report. The analysis shows that once the virus has succesfully penetrated the security of the local machine it starts to monitor several registry entries for any changes. This along with other identified methods like volume information extraction and machine time query are used to counter the effects of any running sandbox environments, honeypots, virtual machines and debuggers.
SADStory Ransomware Distribution
The current attack wave that spreads the SadStory ransomware is distributed all over the world. The hacker operators endorse various techniques and channels to try and infect as many computer users as possible.
One of the primary causes are linked to the spread of double extension files – the hackers generate virus files that appear to be ordinary documents, while at the same time being executable files. This is done by masking the primary extension (such as DOC or PDF) with a double extension (usually EXE) which some users confuse. Various randomly named executables are also in use by the distributors.
A primary infection source is the use of hacker-controlled or hacked download sites where the viruses are either distributed alone or bundled with software installers of popular freeware or trial versions of applications, games, patches and utilities. In recent times BitTorrent trackers have become a widely used place for spreading ransomware strains as well.
The SadStory ransomware is also actively being promoted on various email spam campaigns which typically fall into two types:
- Sending messages with hyperlinks that lead to the hacker-controlled download sites from where the victims can download the binary file and infect themselves.
- Spreading the files as attachments which can be either infected documents, the virus strain itself or another payload downloader which requires a minimal amount of user interaction to execute its built-in processes.
Summary of SADStory Ransomware
| Name |
SADStory Ransomware |
| File Extensions |
.sad |
| Ransom |
Varies |
| Easy Solution |
You can skip all steps and remove SADStory Ransomware ransomware with the help of an anti-malware tool. |
|
Manual Solution |
SADStory Ransomware ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Spam Email Campaigns, malicious ads & etc. |
SADStory Ransomware Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely SADStory Ransomware Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover SADStory Files
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How To Restore SADStory Files
- 1) Use present backups
- 2) Use professional data recovery software
-
– Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



