The Vortex ransomware is a dangerous malware threat which uses the AES-256 cipher, you can remove it by following our complete removal guide.
Vortex Ransomware Description
Security experts have discovered the Vortex ransomware which is a new malware that is of unknown origin. To this date it has not been identified with a known malware family and according to the security analysis it is made by an unknown hacker or a collective.
The virus is also known under the alias of AESxWin. The virus follows the usual ransomware tactic of encrypting important user files with a strong cipher and then extorts the victims for a fee.
Vortex ransomware does not offer any advanced features. The fact that the initial security does not state that the virus is descendant from one of the famous malware families gives an indicaton that it most likely is an independent creation. Such viruses are often sold on underground hacker markets and further modifications can be made by experienced programmers. This means that evolved variants may pose a higher danger than the current iteration.
Upon infection it engages its encryption engine which targets the following file extensions:
.3g2, .3gp, .7z, .acc, .amr, .asf, .avi, .cpp, .cs, .css, .doc, .docx, .flv, .gzip, .html,
.java, .js, .mkv, .mov, .mp3, .mp4, .mpg, .ogg, .ogv, .pdf, .ppt, .pptx, .py, .rar, .rb, .rm,
.rmvb, .rtf, .swf, .tar, .txt, .vb, .vob, .wav, .wma, .wmv, .xls, .xlsx, .zip
They include some of the most popular archives, multimedia files, documents and other types of files. All affected files receive the .aes extension.
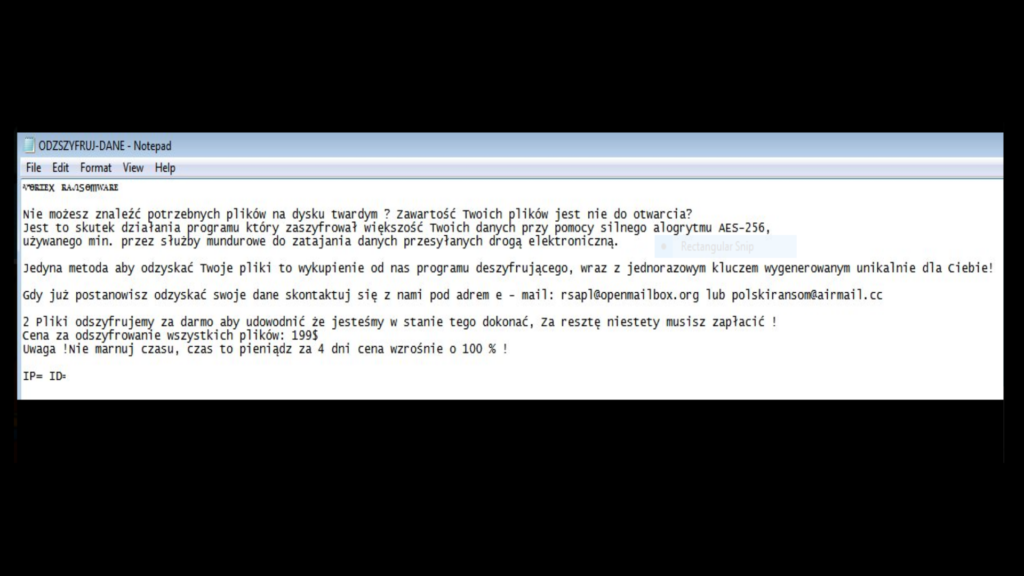
A ransomware note is created in a ODZSZYFRUJ-DANE.txt document which is written in Polish. A machine-translated version reads the following:
Vortex Ransomware
You can not find the necessary files on your hard drive? The contents of your files is not open?
This is a result of the program that encrypted the most of your data using strong alogrytmu aes-256, used min. the uniformed services for disguising data transmitted electronically.
The only way to recover your files are buying from us decryption program, with a single key generated uniquely for you!
Once you choose to recover your data, please contact us at ADREM e-mail: [email protected] or [email protected]
2 Files Decrypt free to prove that we are able to do so, for the rest, unfortunately, you have to pay!
Price for decrypt all files: $ 199
Warning! Do not waste your time, time is money for 4 days price will increase by 100%!
IP = ID =
The ransomware requests a payment of 199 US dollars from the victims.
In addition the virus performs the following actions on the infected computer:
- Computer Information Harvesting – The virus can extract all kinds of system information and send it to the computer operators. Data includes the name of the computer, it’s unique ID signature, running processes, language settings and etc.
- Registry Monitoring – The Vortex ransomware actively monitors for registry key changes. If the virus has a persistent setting, then such behavior is to be expected. Registry monitoring is one of the most basic methods of protecting the virus from being removed manually.
- Persistence – The ransomware creates a registry value for itself thereby creating an environment where manual removal may not be effective.
- Remote Connection – The virus initiates a network connection with the remote C&C servers. They can be used to transmit commands, spy on the users or distribute additional malware payloads.
Vortex Ransomware Distribution
The ransomware has been identified in the beginning of March 2017. It mainly targets Polish-speaking users and is distributed globally.
So far we have identified several malicious domains and email addresses that are connected with it. We suspect that the criminals behind it are using the most popular methods:
- Installers – Often viruses like the Vortex ransomware can be bundled with software installers found on various sites or P2P networks. Depending on the predefined variables set up by the hackers the users may have the option of disabling the installation of the virus by unticking checkboxes during the setup process.
- Download Sites and BitTorrent Trackers – The viruses can often be found on various unknown or hacker-controlled portals and sites. BitTorrent trackers are also a popular distribution source. In most of the cases the viuses resemble application installers for legitimate and well-known games, programs, utilities, patches or utilities. The ransomware can also be found with the following names – AESxWin.exe or polish.exe.
- Spam Messages – The hackers use email servers and accounts to prepare and send bulk messages that link the virus in the body of the text or send out infected files that lead to an infection. In recent times the most popular strategy is to construct efficient phishing messages which use Microsoft Office documents. Once they are opened the victims are presented with a prompt that asks them to enable dangerous macros. As the messages pose as being from a legitimate company or institution of user interest, the victims are very likely to interact with the document. This leads to the Vortex ransomwre infection.
- Browser Hijackers and Web Scripts – Malicious browser extensions (also known as hijackers) and web scripts (including dangerous ad networks) can deliver the virus threat as well. The browser hijackers modifies the default new tabs page, search engine and home page to point to the dangerous site. Dangerous ad networks can also lead to viruses as they often redirect the users to infected download sites.
Summary of the Vortex Ransomware
| Name |
Vortex Ransomware |
| File Extensions |
.aes |
| Ransom |
199 US Dollars in Bitcoins |
| Easy Solution |
You can skip all steps and remove Vortex Ransomware ransomware with the help of an anti-malware tool. |
|
Manual Solution |
Vortex Ransomware ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Spam Email Campaigns, malicious ads & etc. |
Vortex Ransomware Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely Vortex Ransomware Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Encrypted Files
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How To Restore Vortex Files
- 1) Use present backups
- 2) Use professional data recovery software
-
– Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



