CryptoWall 5.1 appears to be the latest version of the CryptoWall virus, considered by many the most dangerous ransomware in the world. This new variant uses AES-256, one of the strongest decryption algorithms available. CryptoWall 5.1 encrypts your files and demands the sum of 250 euros for their decryption. The text “.locked” is added to the names of the encrypted files. If your computer has been infected with the virus, you should avoid paying the ransom. In this article, we offer information and alternate ways to restore your data.
| Name |
Cryptowall 5.1 Ransomware |
| File Extensions |
.locked |
| Ransom |
250 Euro |
| Solution #1 |
CRYPTOWALL 5.1 ransomware can be removed easily with the help of an anti-malware tool, a program that will clean your computer from the virus, remove any additional cyber-security threats, and protect you in the future. |
|
Solution #2 |
CRYPTOWALL 5.1 Ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
CryptoWall 5.1 uses many methods to spread. Most of them come down to tricking the user into clicking a malicious connection. |
How does CryptoWall 5.1 Virus infect computers?
CryptoWall 5.1 uses many methods to spread. Most of them come down to tricking the user into clicking a malicious connection. The largest number of infections happen through email spam. Previous CryptoWall versions are famous for their spam campaigns, and 5.1 may be no exception. The virus’s developers use fake emails, often mimicking those of Microsoft to trick people into clicking. These emails regularly employ JavaScripts and Exploit Kits stored in .zip attachments. Microsoft isn’t the only company that’s mimicked. You can get malicious e-mails from banks, e-commerce stores, social network sites, anything that would fool people into clicking. These emails often have an urgent sounding title like:
- “Your account has been compromised”
- “Your password was changed”
- “Your system is at risk”
Another popular way of spreading malware is through Internet ads: pop-ups, banners, and others. Never click on unclear web commercials, especially if they’re claiming that “Your system is infected” or that “Your system is at risk.” These ads are made to look like anti-virus software when in reality they’re exactly the opposite.
CryptoWall 5.1 – More Information
When the CryptoWall 5.1 ransomware virus breaches your system, it’ll start to make harmful modifications to it. The infection might create files in the following system folders
- C:\Users\[Windows username]\Appdata\Roaming
- C:\Users\[Windows username]\Appdata
- C:\Windows\Temp
- C:\Windows
- C:\User\[Windows username]\AppData\Local
After this is done, the ransomware will proceed to modify some registry keys, Run and RunOnce keys. That’s done so the virus can start when the systems boots up. The following keys are changed:
- HKCU\Software\Microsoft\Windows\CurrentVersion\Run
HKCU\Software\Microsoft\Windows\CurrentVersion\RunOnce- HKLM\Software\Microsoft\Windows\CurrentVersion\Run
- HKLM\Software\Microsoft\Windows\CurrentVersion\RunOnce
Before the encryption process beings, the virus scans for specific file extensions, photos, videos, music, databases, etc.

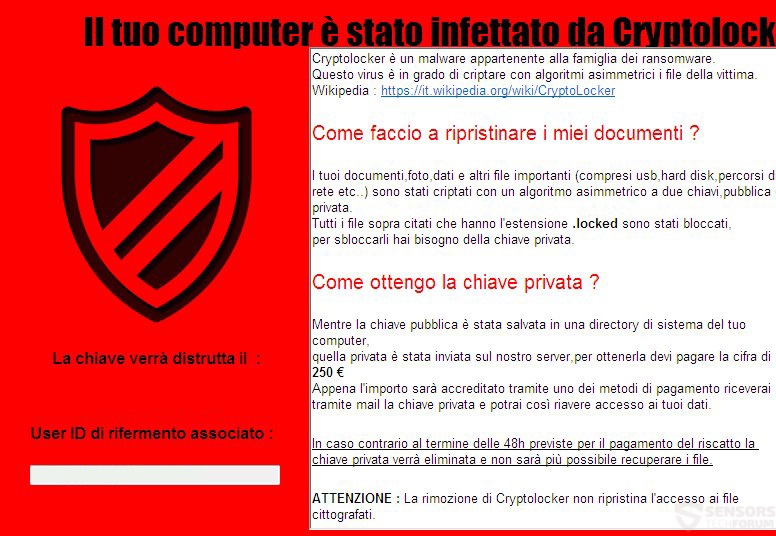
Once the encryption has finished, the infected PC’s files are locked and cannot be used until they’re decrypted. The virus uses the strong AES-256 encryption method. The ransomware gives a ransom note in Italian:
“Il tuo computer è stato infettato da Cryptolocker
Cryptolocker è un malware appartenente alla famiglia dei ransomware.
Questo virus è in grado di criptare con algoritmi asimmetrici i file della vittima.
Wikipedia: https://it.wikipedia.org/wiki/CryptoLocker
Come faccio a ripristinare i miei documenti?
I tuoi documenti, foto, dati e altri file importanti (compresi usb, hard disk, percorsi di rete etc. ) sono stati criptati con un algoritmo asimmetrico a due chiavi, pubblica e privata.
Tutti i file sopra citati che hanno l’estensione .locked sono stati bloccati, per sbloccarli hai bisogno della chiave privata.
Come ottengo la chiave privata?
Mentre la chiave pubblica и stata salvata in una directory di sistema del tuo computer, quella privata и stata inviata sul nostro server, per ottenerla devi pagare la cifra di 250 €.
Appena l’importo sarà accreditato tramite uno dei metodi di pagamento riceverai tramite mail la chiave privata e potrai cosм riavere accesso ai tuoi dati
In caso contrario al termine delle 48h previste per il pagamento del riscatto la chiave privata verrà eliminata e non sarà più possibile recuperare i file.
ATTENZIONE: La rimozione di Cryptolocker non ripristina l’accesso ai file cittografati.
Contaсt: [email protected]”
English Translation:
Your computer is infected with cryptolocker
Cryptolocker is a malware belonging to the family of Ransomware.
This virus can encrypt the victim’s files with asymmetric algorithms
Wikipedia: https://it.wikipedia.org/wiki/CryptoLocker
How do I restore my files?
Your documents, photos, data and other important files (including USB, hard drives, network locations, etc.) have been encrypted with an asymmetric algorithm to two keys, public and private.
All files mentioned above having the .locked extension have been blocked; you need to unlock the private key.
How do I get the private key?
While the public key и been saved in a directory of your computer system, the private и been sent to our server, to get it you have to pay the amount of 250 €.
As soon as the amount is credited with one of the payment methods, you will receive by mail the private key, and regain access to your data.
Otherwise, at the end of 48h provided for the payment of the ransom, the private key will be deleted and it will no longer be possible to recover files.
CAUTION: Removing cryptolocker will not restore access to encrypted files.
Contaсt: [email protected]
A public key should be saved on the infected user’s computer, while the private key would be saved on the server of the cyber-crooks. They give a deadline of 48 hours. After that, they threaten to delete the private key.
CryptoWall 5.1 Ransomware Virus – Summary and Removal
Most experts would advise against paying the ransom, as you’ll be giving your money to criminals, who don’t deserve it. Not only that, you have no guarantee they’ll keep their word and restore your files after you’ve said goodbye to your 250 euros.
You top priority now should be to remove the virus from your computer. You can try to do that by manual deletion of all the virus files. You can also use an anti-malware tool that would delete the virus and keep your system safe from this type of attacks in the future.
You should also wait for a decryptor to be released. If that happens, we’ll update this article to let you know, so keep an eye out.
Cryptowall 5.1 Ransomware Removal
For a faster solution, you can run a scan with an advanced malware removal tool and delete Cryptowall 5.1 completely with a few mouse clicks.
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely Cryptowall 5.1 Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Encrypted Files
-
1) Use present backups
2) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

STEP VII: Preventive Security Measures
-
1) Enable and properly configure your Firewall.
2) Install and maintain reliable anti-malware software.
3) Secure your web browser.
4) Check regularly for available software updates and apply them.
5) Disable macros in Office documents.
6) Use strong passwords.
7) Don’t open attachments or click on links unless you’re certain they’re safe.
8) Backup regularly your data.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter