Read our complete removal guide to learn about the new threat known as the Revenge ransomware which originates from the Cryptomix family.
Revenge Ransomware Description
Malware researchers discovered a new evolved strain of the Cryptomix ransomware known as the Revenge ransomware. It uses an encryption engine (using strong ciphers) which encrypts the user’s data. Like other similar viruses the files belonging to the virus are signed with a counterfeit copyright value which reads MicroWare Considine PLC.
As the virus is descendant from Cryptomix we suspect that many of its behaviour patterns are followed in this iteration. Upon infection the virus engine starts to infiltrate the target system. Depending on the configuration it may execute one of the following actions:
- Persistence – Evolved strains can create a persistent environment which can prevent the virus from being deleted by users who uuse manual removal methods. This may also include registry and system configuration modification, as well as process manipulation.
- Stealth Protection – Advanced ransomware can prevent detection by scanning for any installed security solutions, virtual machines or sandboxing environments. If they are detected the virus stops execution and deletes itself.
- Additional Payload Delivery – The virus may be used to deliver additional viruses to the target machines.
- Remote Control & Information Harvesting – Preconfigured versions of the virus can be modified to include a RAT (Remote Access Trojan) which can harvest sensitive information from the computers and trasmit it to to the hackers.
The researchers have uncovered that the majority of the samples follow a predefined behaviour pattern:
- Startup Modification – The virus changes key settings of the Windows operating system and adds itself to the bootup sequence. This ensures that it will always run when the computer is started.
- Privacy Intrusion – Upon infection the malicious engine harvest confidential data from the installed web browsers (Google Chrome, Mozilla Firefox, Internet Explorer). This includes browser history, stored account credentials, cookies and etc.
- Process Manipulation – The virus engine runs several processes which may use more system resources than other running applications.
- Shadow Volume Copies Deletion – All found shadow volume copies are deleted which prevents data recovery without the use of a professional-grade recovery solution.
The encryption engine uses a combination of the AES and RSA ciphers to affect a total of 453 extensions:
.1CD, .3DM, .3DS, .3FR, .3G2, .3GP, .3PR, .7Z, .7ZIP, .AAC, .AB4, .ABD, .ACC,.ACCDB, .ACCDE,
.ACCDR, .ACCDT, .ACH, .ACR, .ACT, .ADB, .ADP, .ADS, .AGDL, .AI, .AIFF, .AIT, .AL, .AOI, .APJ, .APK,
.ARW, .ASCX, .ASF, .ASM, .ASP, .ASPX, .ASSET, .ASX, .ATB, .AVI, .AWG, .BACK, .BACKUP, .BACKUPDB, .BAK,
.BANK, .BAY, .BDB, .BGT, .BIK, .BIN, .BKP, .BLEND, .BMP, .BPW, .BSA, .C, .CASH, .CDB, .CDF, .CDR, .CDR3,
.CDR4, .CDR5, .CDR6, .CDRW, .CDX, .CE1, .CE2, .CER, .CFG, .CFN, .CGM, .CIB, .CLASS, .CLS, .CMT, .CONFIG,
.CONTACT, .CPI, .CPP, .CR2, .CRAW, .CRT, .CRW, .CRY, .CS, .CSH, .CSL, .CSS, .CSV, .D3DBSP, .DAC, .DAS, .DAT,
.DB .DB_JOURNAL, .DB3, .DBF, .DBX, .DC2, .DCR, .DCS, .DDD, .DDOC, .DDRW, .DDS, .DEF, .DER, .DES, .DESIGN, .DGC,
.DGN, .DIT, .DJVU, .DNG, .DOC, .DOCM, .DOCX, .DOT, .DOTM, .DOTX, .DRF, .DRW, .DTD, .DWG, .DXB, .DXF, .DXG, .EDB,
.EML, .EPS, .ERBSQL, .ERF, .EXF, .FDB, .FFD, .FFF, .FH, .FHD, .FLA, .FLAC, .FLB, .FLF, .FLV, .FLVV, .FORGE, .FPX,
.FXG, .GBR, .GHO, .GIF, .GRAY, .GREY, .GROUPS, .GRY, .H, .HBK, .HDD, .HPP, .HTML, .IBANK, .IBD, .IBZ, .IDX, .IIF,
.IIQ, .INCPAS, .INDD, .INFO, .INFO_, .IWI, .JAR, .JAVA, .JNT, .JPE, .JPEG, .JPG, .JS, .JSON, .K2P, .KC2, .KDBX, .KDC,
.KEY, .KPDX, .KWM, .LACCDB, .LBF, .LCK, .LDF, .LIT, .LITEMOD, .LITESQL, .LOCK, .LTX, .LUA, .M, .M2TS, .M3U, .M4A, .M4P,
.M4V, .MA, .MAB, .MAPIMAIL, .MAX, .MBX, .MD, .MDB, .MDC, .MDF, .MEF, .MFW, .MID, .MKV, .MLB, .MMW, .MNY, .MONEY, .MONEYWELL,
.MOS, .MOV, .MP3, .MP4, .MPEG, .MPG, .MRW, .MSF, .MSG, .MTS, .MYD, .ND, .NDD, .NDF, .NEF, .NK2, .NOP, .NRW, .NS2, .NS3,
.NS4, .NSD, .NSF, .NSG, .NSH, .NVRAM, .NWB, .NX2, .NXL, .NYF, .OAB, .OBJ, .ODB, .ODC, .ODF, .ODG, .ODM, .ODP, .ODS, .ODT,
.OGG, .OIL, .OMG, .ONE, .ORF, .OST, .OTG, .OTH, .OTP, .OTS, .OTT, .P12, .P7B, .P7C, .PAB, .PAGES, .PAS, .PAT, .PBF, .PCD,
.PCT, .PDB, .PDD, .PDF, .PEF, .PFX, .PHP, .PIF, .PL, .PLC, .PLUS_MUHD, .PM!, .PM, .PMI, .PMJ, .PML, .PMM, .PMO, .PMR, .PNC,
.PND, .PNG, .PNX, .POT, .POTM, .POTX, .PPAM, .PPS, .PPSM, .PPSX, .PPT, .PPTM, .PPTX, .PRF, .PRIVATE, .PS, .PSAFE3, .PSD, .PSPIMAGE,
.PST, .PTX, .PUB, .PWM, .PY, .QBA, .QBB, .QBM, .QBR, .QBW, .QBX, .QBY, .QCOW, .QCOW2, .QED, .QTB, .R3D, .RAF, .RAR, .RAT, .RAW, .RDB,
.RE4, .RM, .RTF, .RVT, .RW2, .RWL, .RWZ, .S3DB, .SAFE, .SAS7BDAT, .SAV, .SAVE, .SAY, .SD0, .SDA, .SDB, .SDF, .SH, .SLDM, .SLDX, .SLM,
.SQL, .SQLITE, .SQLITE3, .SQLITEDB, .SQLITE-SHM, .SQLITE-WAL, .SR2, .SRB, .SRF, .SRS, .SRT, .SRW, .ST4, .ST5, .ST6, .ST7, .ST8, .STC,
.STD, .STI, .STL, .STM, .STW, .STX, .SVG, .SWF, .SXC, .SXD, .SXG, .SXI, .SXM, .SXW, .TAX, .TBB, .TBK, .TBN, .TEX, .TGA, .THM, .TIF,
.TIFF, .TLG, .TLX, .TXT, .UPK, .USR, .VBOX, .VDI, .VHD, .VHDX, .VMDK, .VMSD, .VMX, .VMXF, .VOB, .VPD, .VSD, .WAB, .WAD, .WALLET, .WAR,
.WAV, .WB2, .WMA, .WMF, .WMV, .WPD, .WPS, .X11, .X3F, .XIS, .XLA, .XLAM, .XLK, .XLM, .XLR, .XLS, .XLSB, .XLSM, .XLSX, .XLT, .XLTM, .XLTX,
.XLW, .XML, .XPS, .XXX, .YCBCRA, .YUV, .ZIP
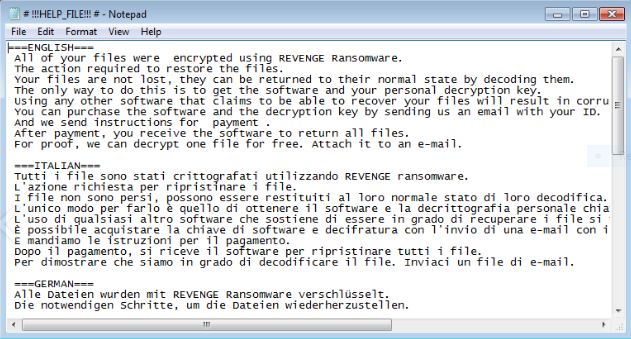
The following ransomware note (crafted in a # !!!HELP_FILE!!! #.TXT file) is shown to the victims when the process is complete:
===ENGLISH===
All of your files were encrypted using REVENGE Ransomware.
The action required to restore the files.
Your files are not lost, they can be returned to their normal state by decoding them.
The only way to do this is to get the software and your personal decryption key.
Using any other software that claims to be able to recover your files will result in corrupted or destroyed files.
You can purchase the software and the decryption key by sending us an email with your ID.
And we send instructions for payment.
After payment, you receive the software to return all files.
For proof, we can decrypt one file for free. Attach it to an e-mail.===ITALIAN===
Tutti i file sono stati crittografati utilizzando REVENGE ransomware.
L’azione richiesta per ripristinare i file.
I file non sono persi, possono essere restituiti al loro normale stato di loro decodifica.
L’unico modo per farlo è quello di ottenere il software e la decrittografia personale chiave.
L’uso di qualsiasi altro software che sostiene di essere in grado di recuperare i file si tradurrà in file danneggiati o distrutti.
È possibile acquistare la chiave di software e decifratura con l’invio di una e-mail con il tuo ID.
E mandiamo le istruzioni per il pagamento.
Dopo il pagamento, si riceve il software per ripristinare tutti i file.
Per dimostrare che siamo in grado di decodificare il file. Inviaci un file di e-mail.===GERMAN===
Alle Dateien wurden mit REVENGE Ransomware verschlüsselt.
Die notwendigen Schritte, um die Dateien wiederherzustellen.
Die Dateien werden nicht verloren, können sie dekodiert werden.
Der einzige Weg, zu tun ist, um die Software zu erhalten, und den privaten Schlüssel zu entschlüsseln.
Mit Software, die auf Ihre Dateien zu können behauptet, bewegen als Folge von beschädigten oder zerstörten Dateien wiederhergestellt werden.
Sie können die Software und Entschlüsselungsschlüssel erwerben, indem Sie uns per E-Mail Ihre ID senden.
Und wir werden Anweisungen für die Zahlung senden.
Nach der Bezahlung werden Sie eine Rückkehr von Software erhalten, die alle Dateien wiederherstellen würde.
Um zu beweisen, dass wir eine Datei kostenlos entschlüsseln kann. Anhängen einer Datei an eine E-Mail.===POLISH===
Wszystkie pliki zostały zaszyfrowane przy użyciu REVENGE szkodnika.
Konieczne działania w celu przywrócenia plików.
Pliki nie są tracone, mogą one zostać zwrócone do swojego normalnego stanu poprzez ich dekodowania.
Jedynym sposobem na to jest, aby oprogramowanie i swój osobisty klucz deszyfrowania.
Korzystanie z innego oprogramowania, które twierdzi, że jest w stanie odzyskać pliki spowoduje uszkodzonych lub zniszczonych plików.
Można kupić oprogramowanie i klucz deszyfrowania wysyłając do nas e-maila z ID.
A my wyślemy instrukcje dotyczące płatności.
Po dokonaniu płatności otrzymasz oprogramowanie do zwrotu plików.
W celu udowodnienia, że możemy odszyfrować plik. Dołączyć go do wiadomości e-mail.===KOREAN===
모든 파일은 REVENGE Ransomware를 사용하여 암호화되었습니다.
파일을 복원하는 데 필요한 작업.
파일은 손실되지 않으며 디코딩하여 정상 상태로 되돌릴 수 있습니다.
이를 수행하는 유일한 방법은 소프트웨어와 개인 암호 해독 키를 얻는 것입니다.
파일을 복구 할 수 있다고 주장하는 다른 소프트웨어를 사용하면 파일이 손상되거나 파손됩니다.
신분증을 이메일로 보내 소프트웨어 및 암호 해독 키를 구입할 수 있습니다.
그리고 우리는 지불 지시를 보낸다.
지불 후 모든 파일을 반환하는 소프트웨어를 받게됩니다.
우리는 무료로 하나의 파일의 암호를 해독 할 수 있습니다. 전자 메일 파일을 보내 주시기 바랍니다.CONTACT E-MAILS:
EMAIL: [email protected]
EMAIL: [email protected]
EMAIL: [email protected]ID (PERSONAL IDENTIFICATION): *****
All affected files are encrypted using the following pattern: 16_hex_char_vicimt_id] [16_hex_char_encrypted_filename] [unknown_8_hex_char_string] [8_char_encrypted_filename].REVENGE.
By looking at the ransomware note we can conclude the following characteristics:
- Anonymous Hosting – It is relatively easy to register email accounts which are used by the hackers to operate the contact address.
- No Set Ransomware Fee – The victims need to contact the hackers to receive the exact ransomware sum. The operators typically employ this tactic to further extort a higher fee.
- Multi-language Delivery – The ransomware note is written in several of the most widely-spoken languages of the world which increases the ransomware’s effectivity.
Revenge Ransomware Distribution
The main delivery method is by using the RIG Exploit Kit using the EITEST attack campaign. This relies on a series of dangerous scripts embedded in various compromised sites and hacker-controlled ad networks. One of the most common sources of infection is an infected SWF file which is loaded by the Adobe Flash Player. The malicious code is executed via a software exploit available
The initial discovery of the malware samples was made in the beginning of March 2017 and due to its multi-language ransomware note the threat targets computers users from around the world.
Other delivery methods include the following:
- Email Spam Messages – They usually employ a social engineering trick to make the users interact with an infected file, script or download the virus from email attachments and inserted links in the body of the email. Recently the hackers have employed infectd Microsoft Office documents as one of the primary infection vectors which pose as files of user interest.
- Infected Installers – The viruses can be embedded in software installers that are distributed on various hacker-controlled download sites.
- Download Sites & P2P Networks – Computer hackers typically infect victims by placing dangerous files on various hacker-controlled or hacked download sites. BitTorrent trackers and other P2P networks are also a popular source, in most cases they pose as iliegal or freeware copies of well-known applications, games, utilities and patches.
- Direct Attacks – Automated vulnerability testing and other forms of direct intrusion attempts can deliver the Revenge ransomware.
Summary of the Revenge Ransomware
| Name |
Revenge Ransomware |
| File Extensions |
Pattern: 16_hex_char_vicimt_id] [16_hex_char_encrypted_filename] [unknown_8_hex_char_string] [8_char_encrypted_filename].REVENGE |
| Ransom |
Varies |
| Easy Solution |
You can skip all steps and remove Revenge Ransomware ransomware with the help of an anti-malware tool. |
|
Manual Solution |
Revenge Ransomware ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Spam Email Campaigns, malicious ads & etc. |
Revenge Ransomware Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely Revenge Ransomware Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Revenge Files
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How To Restore Revenge Files
- 1) Use present backups
- 2) Use professional data recovery software
-
– Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



