An infection with the dangerous GandCrab 5.1.0 ransomware virus leads to serious security issues. With our removal guide, victims can try to restore and protect their computers.
Manual Removal Guide
Files Recovery Approaches
Skip all steps and download anti-malware tool that will safely scan and clean all harmful files it detects on your PC.
SpyHunter is a Windows application designed to scan for, identify, remove and block malware, potentially unwanted programs (PUPs) and other objects. By purchasing the full version, you will be able to remove detected malware instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Distribution of GandCrab 5.1.0 Ransomware Virus
GandCrab 5.1.0 virus is a new data locker ransomware that has been released in attack campaigns against computer users worldwide. The threat could be utilizing widely used tactics of distribution to infect computer systems.
The GandCrab 5.1.0 is a newly discovered strain of the malware family. It has been detected in a limited test release which probably signals that forthcoming infections are going to target specific countries. So far the acquired samples have been detected in a limited test run indicating the the real attacks might use different tactics.
A main method used by the malicious actor behind GandCrab 5.1.0 is the coordination of SPAM email messages — they are used to spread the threats by sending out messages that pose as legitimate notifications sent by popular Internet portals or services that the targets may use. The virus files can be either directly attached or linked in the body. They can also be uploaded to fake download sites which are designed to appear like any of the popular Internet portals or vendor download sites. The malicious actors may use similar sounding domain names, certificates and hijacked design and contents to coerce the victims into thinking that they are accessing the legitimate address.
Another way that the threat may spread is through infected payloads — the use of various files that are infected with virus code. A popular example is the malicious document which can take any form: presentations, rich text files, spreadsheets and databases. Once they are opened by the victims a notification message will pop-up asking the target users to enable the built-in scripts. If this is done the virus infection will follow. The other popular technique is the inclusion of the code in application installers. They are malicious copies of legitimate setup files of popular end user programs that have been modified with the GandCrab 5.1.0 ransomware code.
Ransomware files are also popularly spread by fake user profiles — they can post to community forums or social media accounts. The criminals can utilize both fake or stolen identities to increase the number of infected user.
In certain cases the criminals may also be distributed via malicious browser plugins — additions to the most popular web browsers that are advertised as useful. The plugins are uploaded to the official repositories and often make use of fake or hijacked user reviews and developer credentials. Once they are installed by the users they will execute their built-in instructions that in many cases leads to the GandCrab 5.1.0 ransomware virus infection in the end.
Impact of GandCrab 5.1.0 Ransomware Virus
The GandCrab 5.1.0 ransomware is a new sample originating from the GandCrab malware family. It follows the behavior patterns of the samples that we know so far. At the onset of delivery the GandCrab will start running its many modules, beginning with a persistent infiltration — its code will make the necessary changes to the Windows operating system that will make it very difficult to remove with manual recovery guides. The virus will modify various parts of the operating system such as boot options and configuration files in order to lead to this state. This is combined with the security bypass feature which is used to identify and block any installed security software or services that can stop the infection. This includes programs such as anti-virus engines, firewalls and even sandbox (debug) environments. The GandCrab ransomware family also performs environment checks to make sure that they are not running inside a virtual machine instance.
This module is combined with a data hijacking step which will make the engine harvest sensitive data from the infected machines. It can be used to directly reveal the identity of the machine users by searching for strings that can relate to their name, address, phone number, physical location and even their account credentials. This is done by scanning the contents of the local hard disk drive, memory and even the installed web browsers. The other type of collected information is categorized as “device metrics” and is used to construct an unique infection ID of each compromised host. It is made by an algorithm that computes the end string by taking information from the list of installed hardware components, user settings and operating system environment values.
Various system changes can occur as the GandCrab configuration files permit extensive modification:
- Windows Registry Changes — By changing values that are used by the operating system the virus can cause serious system stability problems. When third-party applications are affected then they may behave improperly or fail to start certain functions.
- Trojan Connection — The identified GandCrab 5.1.0 samples have been found to establish a connection to a hacker-controlled server over the TOR anonymous network. This enables the local clients to report the made infections to the hacker operators. This also allows them to take over control of the machines, steal user data before it is encrypted by the ransomware and deploy other threats as well.
Delivery of Other Threats — The GandCrab ransomware samples can serve as payload delivery mechanisms for other malware. They can be configured to serve all kinds of threats — from browser hijackers to cryptocurrency miners.
The ransomware will use a built-in list of target file type extensions that will be encrypted with a strong cipher. An example one will find the following:
- Databases
- Backups
- Archives
- Music
- Videos
- Images
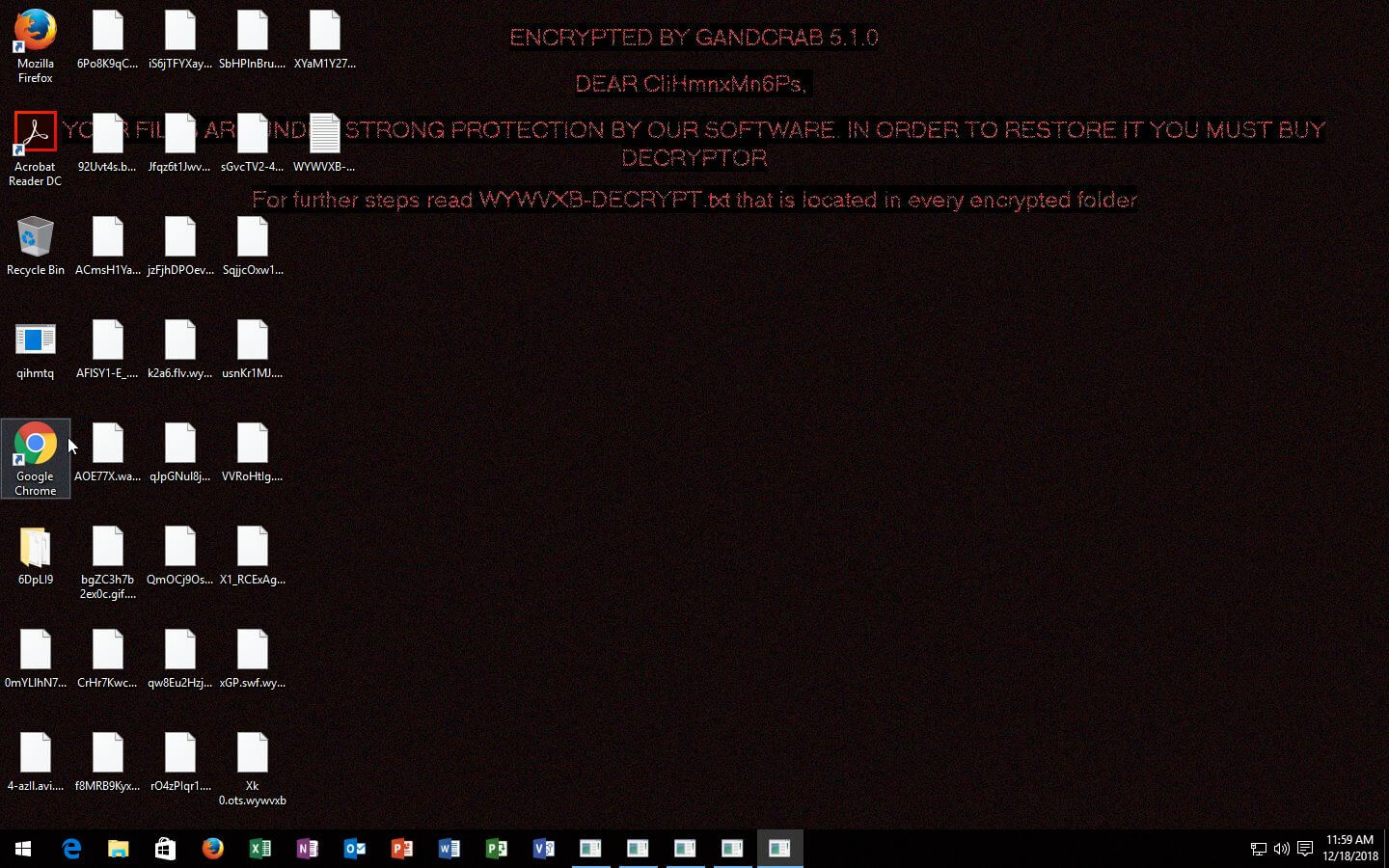
The processed files will receive a randomly generated 6-character extension. The ransomware note will be created in multiple text files and also designate itself as the desktop wallpaper.
Remove GandCrab 5.1.0 Ransomware Virus and Restore PC
Please note that paying the requested ransom fee to cyber criminals does not really solve your problem with GandCrab 5.1.0 crypto virus. In fact, you only encourage hackers to continue spreading ransomware of this kind. Instead, you must remove the threat immediately, and only then look for optional ways to recover your data.
WARNING! Manual removal of GandCrab 5.1.0 ransomware virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
DOWNLOAD SpyHunter Anti-Malware ToolGandCrab 5.1.0 Ransomware Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps below are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover .id.ransomed@india(.)com Files
WARNING! All files and objects associated with GandCrab 5.1.0 ransomware virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
SpyHunter is a Windows application designed to scan for, identify, remove and block malware, potentially unwanted programs (PUPs) and other objects. By purchasing the full version, you will be able to remove detected malware instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



