Freshdesk Virus Description
The limited number of detected samples indicates that the Freshdesk ransomware is probably a testing version still in development. The initial security analysis does not show any correlation between the Freshdesk ransomware and the famous malware families, this means that it is an independent creation. We suspect that it may be a single hacker who is still not experienced enough. This is proven by the fact that Freshdesk virus does not contain any advanced code or features other than the encryption engine.
Upon infection the engine automatically starts the encryption process which targets the most commonly used user data. Freshdesk virus uses a predefined list of file type extensions. At the moment we don’t have a copy of it. However we presume that it processes the most popular data: photos, music, videos, configuration files, backups, archives and etc. Once this is complete a ransomware note is created in a restore_files.html file:
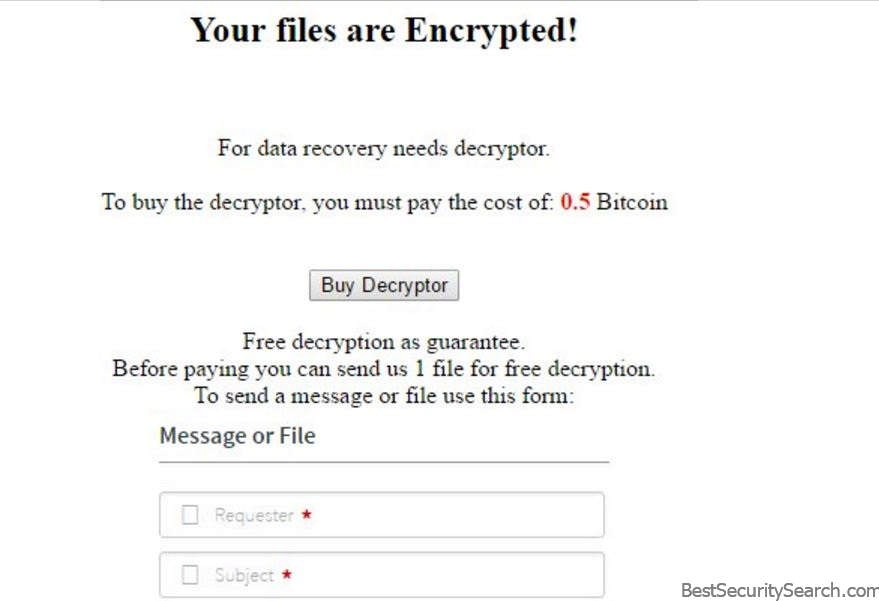
It reads the following message:
Your files are Encrypted!
For data recovery needs decryptor.
To buy the decryptor, you must pay the cost of: 0.5 Bitcoin
button [Buy Decryptor] Free decryption as guarantee.
Before paying you can send us 1 file for free decryption.
To send a message or file use this form:
*****
Freshdesk form
The ransomware message features a short description that explains to the victims that their data has been compromised. The hackers promise them a decryptor which is able to recover their data in return of a payment in the Bitcoin digital currency. The requested sum of 0.5 Bitcoins is the equivalent of about roughly 750 US Dollars. The hackers use a social engineering trick by providing a free decryption in an attempt to gain the victims trust. A support contact form is included directly in the page. This hides their contact address from the victims which masquerades the hackers identity.
We expect to see updated versions of Freshdesk ransomware that may include advanced features such as various surveillance modules that may capture keystrokes (built-in keylogger) or directly remote control the infected computers.
The appearance of Freshdesk virus proves once again that ransomware attacks remain popular among hackers.
Freshdesk Ransomware Virus Distribution
The Freshdesk ransomware virus at the moment has been found in a very limited number of samples and they are randomly-named. As such it is very difficult to assess which is the primary method of distribution. We assume that the criminals behind the virus are using the most popular strategies.
One of them involves the creation and coordination of mass email spam campaigns. They use various social engineering strategies that attempt to make the targets infect themselves with the ransomware. Likewise infected office documents are also used to spread viruses of all types. To avoid detection the ransomware is being downloaded from a remote hacker-controlled server. If the targets enable the script execution then the virus is delivered to their machine and the infection process begins.
The other popular mechanism that can be employed to spread the Freshdesk ransomware is its inclusion in infected software bundles. They constitute software installers for popular applications, games, utilities, patches and etc. They have been modified to contain the dangerous code. The criminals distribute them on various hacker-controlled sites and P2P networks like BitTorrent. Various forms of browser hijackers, web script redirects and malicious ad networks can redirect or directly download the ransomware executable. They can potentially endanger the privacy of the users by harvesting the stored settings, cookies, bookmarks, account credentials and history.
In some cases the hackers can also resort to directly launch automated or manual vulnerability testing attacks.
Summary of the Freshdesk Ransomware Virus
| Name |
Freshdesk |
| File Extensions |
.www |
| Ransom |
0.5 Bitcoins |
| Easy Solution |
You can skip all steps and remove Freshdesk ransomware with the help of an anti-malware tool. |
|
Manual Solution |
Freshdesk ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Spam Email Campaigns, malicious ads & etc. |
Freshdesk Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely Freshdesk Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover .www Files
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How To Restore .www Files
- 1) Use present backups
- 2) Use professional data recovery software
-
– Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



