EvilLock ransomware is a new version of Javascript Evil ransomware. The threat is of file-encrypting type and is designed to transform target files making them unable to be opened. It utilizes strong and unique AES algorithm for file encryption and the malicious file extension .evillocked as a sign of successfully encrypted file. The file HOW_TO_DECRYPT_YOUR_FILES.HTML serves as EvilLock ransom note.
The content in this article serves all victims of EvilLock ransomware by granting safe ways of its removal and reliable data recovery means.
| Name |
EvilLock Ransomware |
| File Extension |
.evillock |
Other associated extensions |
.file0locked |
| Ransom |
0.3 BTC |
| Solution #1 |
Use the help of an anti-malware tool to remove EvilLock ransomware and any additional cyber-security threats. |
|
Solution #2 |
EvilLock ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Malicious dropper, spam emails, malicious URLs, malicious attacments, exploit kits, freeware. |
Distribution of EvilLock Ransomware
EvilLock ransomware is possibly distributed via malicious dropper. This type of malware is developed to launch viruses by installing them on targeted computers. As a way of its distribution, it is most likely to be used spam emails that contain malicious web links, attachments or both. The email sender may pose as someone that belongs to the team of a legitimate service. The malicious intenders usually aim to provoke a feeling of emergency in the users in order to force them to interact with the content or the attachment.
Another distribution way may be freeware software that comes bundled with the malicious payloads of EvilLock ransomware.
In some cases, the crooks create a web page that contains the malicious payloads of EvilLock ransomware in its source code. Furthermore, they may compromise the code of official web pages transforming them into means of ransomware distribution. Via attack techniques, they set an automatic download process. Thus all malicious files could land on the computer after a single visit to such compromised website. Except in the text of an email, the malicious web links may be included in malicious advertising campaigns.
Exploit kits might also be used for the distribution of EvilLock ransomware.
- Use free online services like VirusTotal that scan and analyze suspicious files and URLs. They could efficiently detect all kinds of malware thanks to the access to the information gained by various antivirus engines, website scanners, file and URL analysis tools and user uploads.
- Search for the official website of the software you want to download. A download from legitimate source will guarantee the safety of your computer.
More About the EvilLock Crypto Virus Infection
EvilLock ransomware is a new version of Javascript Evil ransomware. It is a file-encrypting type of ransomware that utilizes powerful AES encipher algorithm that transforms particular files making them unusable. Each encrypted file gets the extension .evillock at the end of the original name.
The EvilLock crypto virus is designed to scan all disks and drives for specific file types that should be enciphered. So, the analyses of professional security engineers disclose the following file types as part of EvilLock’s target list:
.3fr, .accdb, .ai, .arw, .bay, .cdr, .cer, .certs, .cr2, .crt, .crw, .dbf, .dcr, .der, .dng, .doc, .dwg, .dxf, .dxg, .eps, .erf, .img, .indd, .jpg, .kdc, .mdb, .mdf, .mef, .mrw, .nef, .nrw, .odb, .odc, .odm, .odp, .ods, .odt, .orf, .p12, .p7b, .p7c, .pdd, .pef, .pem, .pfx, .ppt, .psd, .pst, .ptx, .pub, .r3d, .raf, .raw, .rtf, .rw2, .rwl, .sr2, .srf, .srw, .wb2, .wpd, .wps, .x3f, .xlk, .xls
Except the malicious extension .evillock as part of all encrypted data, EvilLock ransomware creates two files that contain a message from the attackers to the victims. The files are named HOW_TO_DECRYPT_YOUR_FILES.TXT and HOW_TO_DECRYPT_YOUR_FILES.HTML. Both files present identical text that’s only the file type that differs.
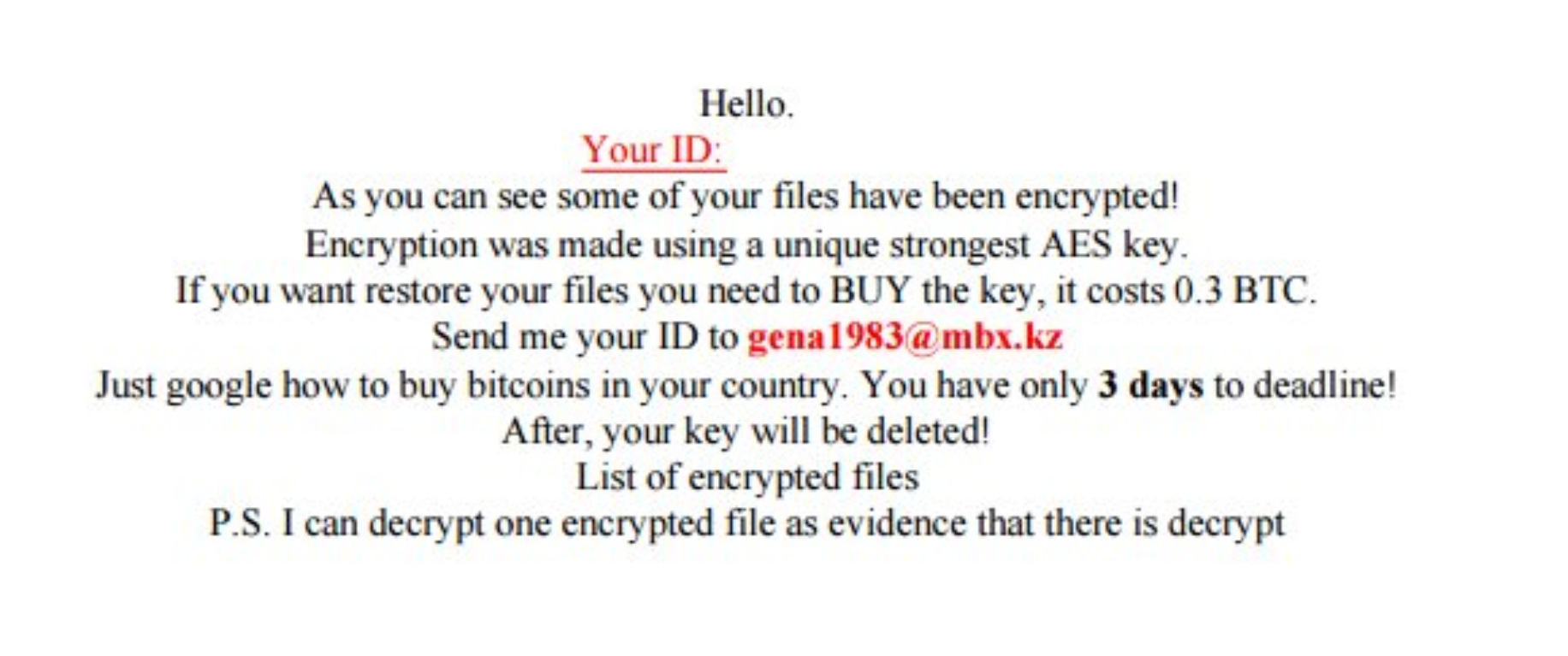
The text of EvilLocker ransom note reads:
“Hello.
Your UID: [Different for each victim] As you can see some of your files have been encrypted!
Encryption was made using a unique strongest AES key.
If you want restore your files you need to BUY the key, it costs 0.3 BTC.
Send me your ID to [email protected]
Just google how to buy bitcoins in your country. You have only 3 days to deadline!
After, your key will be deleted!
List of encrypted files
P.S. I can decrypt one encrypted file as evidence that there is decrypt”
The attackers urge all victims to contact them to [email protected] by sending an email with the ID code in order to provide further information about the decryption of .evillocked virus files. The ransom message indicates that a payment of 0.3 BTC (at the present moment it equals to $303.8) need to be paid for the unique key that will decrypt all enciphered files.
However, no matter that they give a word that the files will be decrypted after the payment, there is no guarantee this will happen. So, if you are a victim of EvilLock ransomware, it is better to avoid any negotiations with cyber criminals and make an effort to contend the infection by yourself using cyber security means.
- The recovery process should follow the fulfillment of some essential steps:
- Complete removal of EvilLocker ransomware from the computer.
- Available copies of all encrypted files – they do not contain malicious code and are safe.
EvilLock Ransomware Removal
Remove EvilLock ransomware with a few mouse clicks – run a scan with an advanced malware removal tool and delete EvilLock completely.
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely EvilLock Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Encrypted Files
- 1) Use present backups
- 2) Use professional data recovery software
-
– Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
STEP VII: Preventive Security Measures
-
1) Enable and properly configure your Firewall.
2) Install and maintain reliable anti-malware software.
3) Secure your web browser.
4) Check regularly for available software updates and apply them.
5) Disable macros in Office documents.
6) Use strong passwords.
7) Don’t open attachments or click on links unless you’re certain they’re safe.
8) Backup regularly your data.



