A new version of the Shade ransomware has been identified. The variant not only encrypts the victim user’s files but also installs remote access tools. The malicious users can control and install additional malware and viruses on the target hosts as well as spy on the user activities. The Shade ransomware is high risk because it uses several layers of protection to disguise itself from security software and the victim users. The trojan is used to target banking and financial institutions in Russia and the CIS states.
| Name |
Shade Ransomware |
| File Extensions |
.shade or .no_more_ransom |
| Ransom |
Varies |
| Solution #1 |
Shade ransomware can be removed easily with the help of an anti-malware tool, a program that will clean your computer from the virus, remove any additional cyber-security threats, and protect you in the future. |
|
Solution #2 |
Shade Ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
The latest version of the Shade ransomware searches the compromised system for installed applications in accordance with a predefined list. |
Features of the New Shade Ransomware
The latest version of the Shade ransomware searches the compromised system for installed applications in accordance with a predefined list. The algorithm is specifically targeted against bank systems and financial companies. In Russia and the CIS states. The security researchers note that the malware searches for the strings “BUH”, “BUGAL”, “БУХ“, „БУГАЛ“ in the names and descriptions of the target hosts. All of these strings refer to accounting. If there is a positive match, Shade downloads and executes files from a predefined remote server.
The updated code encrypts the user data in exchange for money but installs additional malware threats. The behavior indicates a bot called Teamspy, which works with the legitimate TeamViewer application. The software is used for communication with the remote malicious command and control (C&C) server.
Teamspy also utilizes two plugins that are stored in an encrypted form. They are decrypted in real time by the ransomware and operate in RAM memory only. They hold the bot’s main module which provides real-time remote access to the infected targets through the RDP (Remote Desktop Protocol).
This variant is also known as Trojan-Ransom.Win32.Shade.yb (MD5 checksum: 21f4bbcd65d0bff651fa45d442e33877) and Trojan-Spy.Win32.Teamspy.gl (MD5 checksum: 4235f3730bbd303d9b3956f489ff240d).
Shade Ransomware Behavior
The two plugins that form the basis of the ransomware provide the remote control capabilities through the RDP protocol. They are the following:
- Installvpn.pg – the plugin covertly installs the TeamViewer VPN driver.
- Rdw.pg – the plugin covertly installs the “RDP Wrapper Library” application and applies modifications to the system settings to activate and maintain the RDP session.
The researchers have found out that the bot does not automatically start the VPN session. The specialists presume that the remote control capabilities are used only in special cases.
The Teamspy executable file is stored in a standard NSIS installer with the following contents:
- NSIS-script script.bin which controls the unpacking process
- NSIS plugins – nsExec.dll, StdUtils.dll and System.dll
- Legal utility NirCMDfile 6kzi6c94h2oeu4)
- Legal utility 7zip (file vuoup3teqcux6q)
- Image 2b6zfhf3ui7e03iv6.jpg
- Image 6nmxxselb250du8c.jpg with an embedded password-protected 7z archive
Once the installation process has been initialized it executes the script.bin file which calculates a hash checksum used for the password of 7z archive.
The protected archive extracts its contents to the hidden folder “%APPDATA%\DIV”. This contains the Teamviewer components and encrypted bot configuration files.
The installer starts the cfmon.exe upon unpacking which installs the avicap32.dll malicious library that holds the body of the Teamspy bot. The body of the bot is protected with a series of encryption layers and obfuscated to prevent complex analysis.
The avicap32.dll modifies the Teamviewer process running in the system background. It intercepts some of the system calls and internal procedures. The victim cannot view the graphical user interface and may not know that such a service is active unless he accesses the task managers and looks up the relevant application.
When a remote access session is active the bot transmits proof of it’s existence to the remote server. The following options are available to the criminal user:
- startaudio / stopaudio: start/stop of audio recording.
- startvideo / stopvideo: start/stop of video recording of the screen.
- lexec: download and execute a file from a URL provided by the C&C server.
- cmd: provide malicious users with the remote control console.
Other commands include the modification of system files, updating and deleting bot plugins and computer power controls (shutdown, restart, hibernation, etc.), restarting the bot and self-destruction.
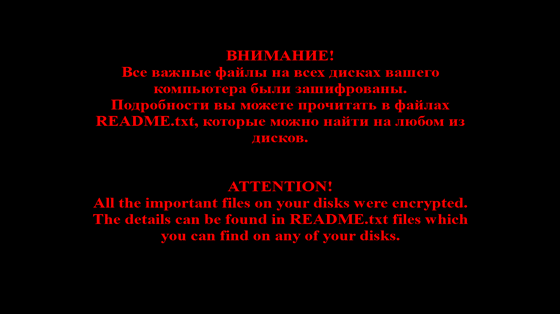
A newer Shade variant uses the no_more_ransom extension and the [email protected] email contact in the ransomware message.
Shade Ransomware Decryption
A Shade Decryptor is available at No More Ransomware. The utility is designed to recover the encrypted files.
1. Navigate to No More Ransomware’s list of decryptors.
2. Download the relevant decryptor from the website.
3. Extract and run the utility, make sure to allow the application to run if the UAC (User Account Control) pops up.
4. Select all connected drives in the dialog box of the utility and start the scan.
5. Wait for the application to complete scanning and specify the path to the encrypted files.
6. If the scan was unable to detect the encrypted files, then it will request the path to the readme.txt bundled with the ransomware.
Additional Tips
To prevent ransomware from accessing your sensitive data always have backups stored on secure locations – external hard drives, flash drives and secured cloud storage services. Always use updated security software and keep your definitions updated. Avoid risk online behavior like downloading and installing files from unknown sources.
Counterfeit emails and websites are also a major source of ransomware. Always make sure that you are accessing the official web pages of the services that you use.
For more information check the research report by security expert Fedor Sinitsyn.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



