This Ransomware is a newly discovered malware threat which is still under development and it can be removed easily by following our removal guide.
This Ransomware Description
Security experts have alerted us of the discovery of a new virus called This ransomware which is made by an unknown hacker or a criminal collective. At the moment the initial security analysis is not yet complete and we do not have any detailed information about similarities with some of the malware families.
As the ransomware is still under development we have no idea of what the final version might contain. We suspect that the developers behind it can integrate modules such as:
- Additional Payload Delivery – This ransomware can be used to deliver additional viruses to the infected computer host by downloading them from remote C&C servers.
- System Modification – The virus engine can engage in dangerous system changes which can render the infected host slow or even unusable. This is done by usually modifying the Windows registry, boot settings, configuration settings and other variables which can impact the computer’s ordinary functions, capabilities and performance.
- Persistence Setup – This ransomware can create conditions that prohibit manual removal by creating an environment which automatically starts the malicious process and protects (usually by replicating) the main binary and all related options.
- Information Harvesting – The virus engine may be able to steal important user data or harvest stored session cookies, account credentials, passwords and other related information from logged in services, browsers and applications.
- Process Manipulation – The virus engine may modify, kill or start new processes which can prevent its discovery by security solutions.
- Shadow Volume Copy Deletion – This ransomware may include a Shadow Volume Copy deletion function which prevents data recovery if a quality data recovery solution is not used.
Upon infection it starts its encryption engine which should target sensitive user files and extorts them for a ransomware fee payment. As the ransomware is still under development this module is still not complete and not configured properly. If this were a working strain then this engine would use a strong cipher (such as AES-256) to target specific file type extensions and use a ransomware extension to mark the affected files. Possible targets include archives, music, photos, videos, configuration files and etc.
A string which contains the ransomware note has been extracted from the available malware samples and it reads the following:
SURPRISE! THIS IS ENCRYPTING RANSOMWARE YOU ARE FUCKED!
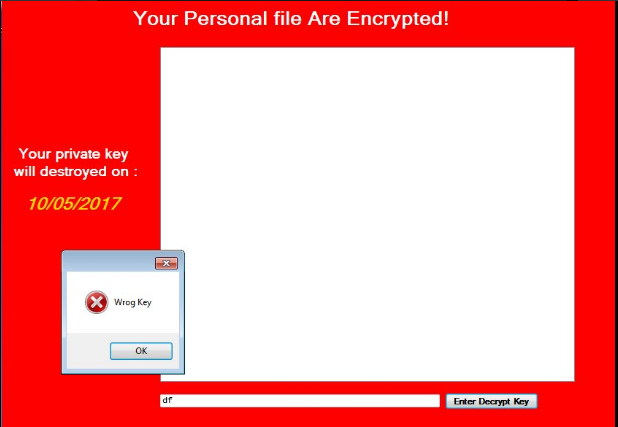
When the encryption process is complete a screenlocker is instituted on the victim machine. It prevents any ordinary computer interacion with the computer unless the victm pays the restore fee. The screen is changed to display white text on a red background which reads the following:
Your Personal file Are Encrypted!
Your private key will be destroyed on:
XX/XX/XXXX
From this we can deduce that the virus engine calculates a unique victim ID code that is associated with every infected machine. Usually this ID is made up of a few local variables such as hardware components, current date and time (at the time of infection) and related data.
This Ransomware Distribution
As the virus is still under development there are only a limited set of malware samples available. They target English-speaking users globally and are delivered as single binary files bearing the name test.exe.
Possible infection routes include the following:
- Email Spam Messages – They usually employ a social engineering trick to make the users interact with an infected file, script or download the virus from email attachments and inserted links in the body of the email. Recently the hackers have employed infectd Microsoft Office documents as one of the primary infection vectors which pose as files of user interest.
- Infected Installers – The viruses can be embedded in software installers that are distributed on various hacker-controlled download sites.
- Download Sites & P2P Networks – Computer hackers typically infect victims by placing dangerous files on various hacker-controlled or hacked download sites. BitTorrent trackers and other P2P networks are also a popular source, in most cases they pose as iliegal or freeware copies of well-known applications, games, utilities and patches.
- Direct Attacks – Automated vulnerability testing and other forms of direct intrusion attempts can deliver This ransomware.
Summary of This Ransomware
| Name |
|
| File Extensions |
N/A |
| Ransom |
Varies |
| Easy Solution |
You can skip all steps and remove ransomware with the help of an anti-malware tool. |
|
Manual Solution |
ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Spam Email Campaigns, malicious ads & etc. |
Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover This Files
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How To Restore This Files
- 1) Use present backups
- 2) Use professional data recovery software
-
– Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



