Malware researchers have discovered the Popcorn Time ransomware which is still under development by its creators. To learn more about the threat and how to remove existing infections read our removal guide.
| Name |
Popcorn Time |
| File Extensions |
Unknown |
| Ransom |
Varies |
| Solution #1 |
You can skip all steps and remove Popcorn Time with the help of an anti-malware tool. |
|
Solution #2 |
Popcorn Time ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Spam Email Campaigns, malicious ads & etc. |
Popcorn Time Ransomware Description
A new malware threat has been uncovered bearing the name Popcorn Time ransomware. The virus is still under development and we haven’t seen it in any large-scale attacks for that reason. However updated versions of it may be coming soon and that is the reason why anti-virus and anti-spyware vendors are already adding it to their updated definition sets.
Upon infection it displays a Windows update-like lockscreen while the encryption engine is running. At the moment we do know which specific file type extensions it targets, however it would be very likely that it includes the most popular ones used by audio, video, documents and other types of files. When the encryption is complete a ransomware message is displayed which displays the following contents:
Warning Message!!
We are sorry to say that your computer and your files have been encrypted,
but wait, don’t worry. There is a way that you can restore your computer and all of your files06 Days 23:59:09 Hours
When countdown ends your files will be lost foreverYou must send at least [BAMOUNT] Bitcoin to our wallet and you will get your files back
Your personal unique ID: [UID] Send [BAMOUNT] BTC to this address: [WADDRESSS]
After you’ve made the payment, you will get a code, please insert it here:
……………… [Decrypt]
Another malware sample includes a different ransom note with the following contents:
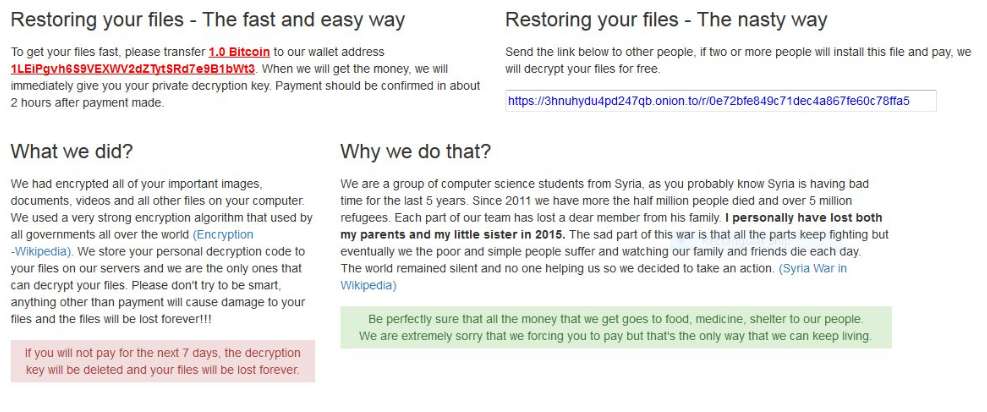
Restoring your files – The fast and easy way
To get your files fast, please transfer 1.0 Bitcoin to our wallet address
1LeiPgvh6S9VEXWV2dZTytSRd7e9B1bWt3. When we will get the money, we will
immediately give you your private decryption key. Payment should be confirmed in about
2 hours after payment made.What we did?
We had encrypted all of your important images,
documents, videos and all other files on your computer.
We used a very strong encryption algorithm that used by
all governments all over the world (Encryption – Wikipedia).
We store your personal decryption code to
your files on our servers and we are the only ones that
can decrypt your files. Please don’t try to be smart,
anything other than payment will cause damage to your
files and the files will be lost forever!!!If you will not pay for the next 7 days, the decryption
key will be deleted and your files will be lost forever.Restoring your files – The nasty way
Send the link below to other people, if two or more people will install this file and pay, we
will decrypt your files for free.https://3hnuhydu4pd247qb.onion.to/r/0e72bfe849c71dec4a867fe60c78ffa5
Why we do that?
We are a group of computer science students from Syria, as you probably know Syria is having bad
time for the last 5 years. Since 2011 we have more the half million people died and over 5 million
refugees. Each part of our team has lost a dear member from his family. I personally have lost both
my parents and my little sister in 2015. The sad part of this war is that all the parts keep fighting but
eventually we the poor and simple people suffer and watching our family and friends die each day.
The world remained silent and no one helping us so we decided to take an action. (Syria War in
Wikipedia)Be perfectly sure that all the money that we get goes to food, medicine, shelter to our people.
We are extremely sorry that we forcing you to pay but that’s the only way that we can keep living.
Popcorn Time Ransomware Distribution
The Popcorn Time Ransomware is still under development and as such we have not witnessed it in any large-scale attack campaigns. However the primary infection sources include spam email campaigns, browser hijackers, exploit kits and etc.
Popcorn Time Ransomware Removal
For a faster solution, you can run a scan with an advanced malware removal tool and delete Popcorn Time completely with a few mouse clicks.
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely Popcorn Time Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Encrypted Files
-
1) Use present backups
2) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

STEP VII: Preventive Security Measures
-
1) Enable and properly configure your Firewall.
2) Install and maintain reliable anti-malware software.
3) Secure your web browser.
4) Check regularly for available software updates and apply them.
5) Disable macros in Office documents.
6) Use strong passwords.
7) Don’t open attachments or click on links unless you’re certain they’re safe.
8) Backup regularly your data.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



