The MasterBuster ransomware is the latest offspring of the open-source HiddenTear ransomware family that compromises user data and appends the HCKED extension. Learn more about the virus and how to remove it in our article below.
| Name |
MasterBuster |
| File Extensions |
HCKED |
| Ransom |
3500 – 10000 rupees |
| Solution #1 |
MasterBuster Ransomware can be removed easily with the help of an anti-malware tool, a program that will clean your computer from the virus, remove any additional cyber-security threats, and protect you in the future. |
|
Solution #2 |
MasterBuster Ransomware can be removed manually, though it can be very hard for most home users. See the guide below. |
| Distribution |
Phishing links, click bait ads, email spam, and others. |
MasterBuster Ransomware Description
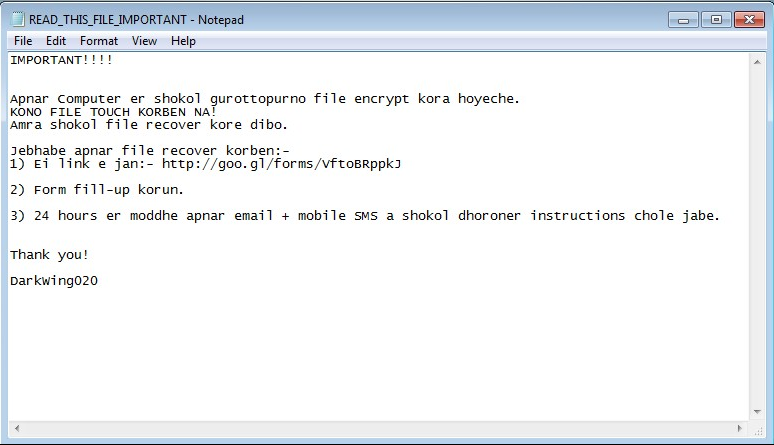
The MasterBuster ransomware is new variant of the open-source ransomware project Hiddentear. The first malware samples were discovered this month (October 2016) being delivered with a Bengali ransom note which means that the operators of the code are probably from Asia.
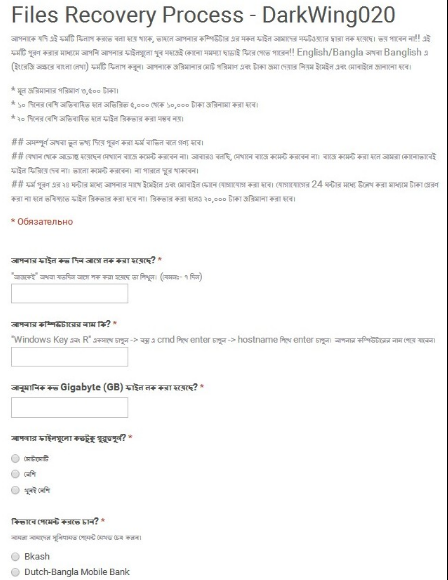
Upon infection the virus encrypts target user data with a strong cipher and appends the HCKED extension. The interesting thing in this iteration of HiddenTear is that the hackers request the users to fill out a form in Google Sheets as part of the ransom sum payment process. The request sum is 3500 ruppees, if the user delays payment for more than 10 days then it is increased to 5000 to 10000 rupees.
The ransomware operators also allow payment via various options – Bkash, Dutch-Bangla Mobile Dank and others.
The following sites are related to the MasterBuster ransomware distribution and control processes:
- http://decrypt.ez.lv/
- decrypt.ez.lv/ddrt/write.php?info=
- http://goo.gl/forms/VftpBRppkJ
- docs.google.com/forms/d/1dUrtnhlouJBZKyJjPU4x_nvbXO2jkd8vf7nkI_7DOl0/viewform
The ransomwre variant has already been added to most definitions list of the major anti-spyware and anti-virus vendors.
MasterBuster Ransomware Distribution
The MasterBuster ransomware is distributed mainly through email spam messages and malware programs. In many cases the virus is spread as fake documents bearing popular file types (PDF and Microsoft Word documents).
Some of the malware samples have also been spotted in adware-infected software installers downloaded from untrusted download sites and P2P networks like BitTorrent.
MasterBuster Ransomware Removal
For a faster solution, you can run a scan with an advanced malware removal tool and delete MasterBuster completely with a few mouse clicks.
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely MasterBuster Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Encrypted Files
-
1) Use present backups
2) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

STEP VII: Preventive Security Measures
-
1) Enable and properly configure your Firewall.
2) Install and maintain reliable anti-malware software.
3) Secure your web browser.
4) Check regularly for available software updates and apply them.
5) Disable macros in Office documents.
6) Use strong passwords.
7) Don’t open attachments or click on links unless you’re certain they’re safe.
8) Backup regularly your data.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



