Experts identified the Industroyer malware that causes damage to critical infrastructure. The virus has been found to be extremely sophisticated. The Industroyer malware is also dubbed “Crash Override” and its goal is to disrupt the industrial control systems. The in-depth security analysis made by numerous vendors and experts has consequently labelled it as Stuxnet’s successor due to its high impact and capabilities.
The Discovery of the Industroyer Malware
In the beginning of this month two anti-virus vendors discovered malware samples of a previously-unknown virus. Their reports produced a thorough analysis of the reported threat – the Industroyer Malware, also known as Crash Override. The most famous example of a threat targeting energy critical infrastructure is Stuxnet, the virus that was employed in the attacks against the Iranian plants. Subsequent evolution and spin-offs that used the same strategy were further developed in later campaigns that, depending on the case, were able to penetrate facilities worldwide. The most recent event was the Ukrainian power plant attack that took place in the days preceding Christmas 2015. Other related attacks include the PLC Blaster Worm incidents.
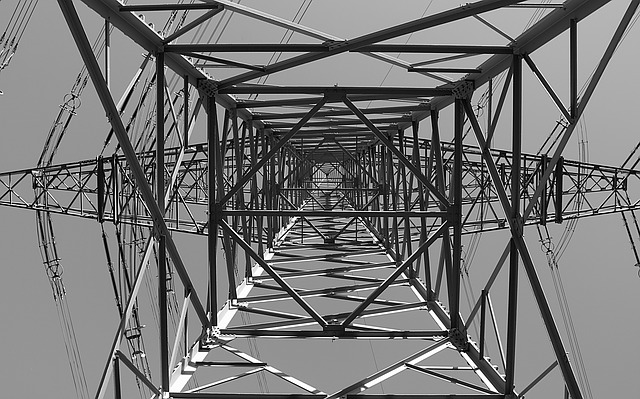
For the first time the criminal operators were able to effectively disrupt the electric grid operations thanks to an evolved malware called BLACKENERGY3. It allowed the hackers to gain access to the internal network of the power plant operators which relayed them to the grid operations themselves. Using a legitimate functionality they were able to disconnect the substations which caused a massive black down. The first instances of the Industroyer Malware were detected in a single substation in the Ukrainian power grid systems on December 17 2016. According to the reports the detected version back then was a proof of concept that can be scaled in future versions to even bigger targets. Industroyer Malware uses intelligent algorithms that perform automated reconnaissance of the networks after the successful infection. The virus code used the internal protocols to map the environment and select the appropriate target.
Capabilities of Industroyer Malware
The malware itself is composed of a modular framework that is made up of three main components:
-
The Initial Backdoor – The first stage of infection is started by this module. It is used to infiltrate the network and performs several actions: install additional backdoor components and tools if configured and to install and execute the loader. The backdoor is able to authenticate with a local proxy using internal network resources before the other components are started. A HTTP channel is created to relay criminal commands and take control over the compromised controllers and assets.
-
Loader Module – The component is able to load additional modules and starts additional functionality. Based on the samples it can execute the data wiper automatically or after the hackers customize its settings. The data wiper is able to delete registry entries, overwrite sensitive files and as a result render the victim devices and software completely unusable. Device specific modules are also loaded in the second stage infection. They manipulate sensitive industry protocols and masquerade as the legitimate owners. The hacker-provided instructions are responsible for all sabotage actions.
-
Payloads – They trigger hacker-specified attacks according to predefined scenarios. The captured Industroyer malware samples so far distribute four separate payload types that are used in different attack campaigns.
RELATED: Experts Devise Ransomware Attack Against Water Supply
Industroyer Malware Attacks
Crash Override can use its IEC 104 Module to kill a master process and ma square as the legitimate pattern. Such actions use the protocol implementation that is standard with industrial controllers. As a result the hackers can manipulate and sabotage the functionality of power plants and other infrastructure that rely on these standards. The malware also contains a IEC 61850 module that is able to subvert configuration files and scan the infected local network. When a potential infection candidate is identified as part of its attack pattern an intrusion attempt is executed. The virus code communicates with the target machine and determines if it is a circuit breaker switch. If the check is passed then Industroyer malware can manipulate the values thereby causing a sabotage.
An interesting addition is that the built-in OPC component does not require a predefined configuration file. Using smart algorithms the virus can overwrite sensitive settings that are used by critical infrastructure. Several different digital relay hardware components can be shut down by leveraging the SIPROTEC DOS (denial of service) module that uses a well-known vulnerability tracked in the CVE-2015-5374 security advisory.
The implications of a successful infection can lead into some of the most dangerous and deadly attacks as the virus is highly advanced. The threat can be updated to support new protocols and devices, the security analysis also revealed that once injected into the local network it can semi-autonomous cause different types of sabotage. Possible scenarios include the following:
-
Substation De-energization – The Crash Override malware is able gain control of closed breakers by creating a loop of operations. This results in an effective de-energization of the substation and actively prevents system operators from controlling the grid. Depending on the configuration of the infrastructure this can cause an outage.
-
Substation Isolation – The security experts are looking into a possible disruptive attack that is related to the configuration of the breakers position. The Industroyer malware can make the automated protective operations to isolate the substation by creating a continuous loop that constantly changes the status of the breakers.
-
Sequence Failures– Coordinated malware incidents can cause a sequence of failures.
-
Denial of Visibility – The hackers can use the advanced modules built into the Industroyer malware to make any control messages be ignored by the infected machines.
-
Protective Relays Bypass – By manipulating the automated protective systems with a Denial of Service (DOS) attack the Industroyer malware can effectively bypass the protective systems. This is done by using a vulnerability tracked in the CVE-2015-5374 advisory affecting the Siemens SIPROTEC relays. The company issued patches that amended the bug in July 2015 however not all infrastructure have implemented it yet.
Defend Against Industroyer Malware Intrusions
Critical infrastructure operators can protect themselves by employing the best security practices and take appropriate measures to protect against possible attacks. Specifically utility companies and critical facilities should enforce the standards when it comes to automated controllers. The security researchers advise engineers to perform daily backups of important data including project logic, IED configuration files and application installers. Such measures can prevent the dangerous impact of the file wiper component. Incident response plans and adequate protection should be employed at all times. According to the researchers passive defenses are not appropriate solutions. A well-prepared cyber security team can protect against threats of this type.



