The Twitter account of Hillary Clinton’s campaign chairman John Podesta was hacked on October 12. As usual, the breached Twitter account was used to send a joke-tweet about Podesta switching sides to Donald Trump.
The Twitter Hack – Details
As Donald Trump would put it, Hillary Clinton’s campaign chairman needs more “cyber.” The account was breached using information from recent emails published by WikiLeaks. The hacked account tweeted the following message:
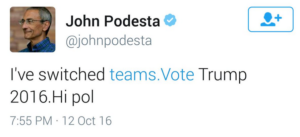
The “Hi pol” part of the tweet is speculated to be addressed towards the /pol/ section of 4chan dedicated to political incorrectness. This probably indicates that the hack was a mere prank, as a methodical hacker wouldn’t leave such an obvious trace.
The tweet was deleted soon after it was published. John Podesta’s iCloud account was also hijacked. The attackers may have wiped his data.
Hillary Clinton, Donald Trump, Security, Twitter, and Cyber
The hacking of Hillary Clinton’s campaign manager isn’t the most embarrassing cyber-security screw up by a politician this year. Back in September Owen Smith published his phone-bank account and password on Twitter. Luckily for him, no unauthorized party entered his account.
Celebrity hacks are piling up. The group OurMine has hacked a lot of It notables and like Jimmy Wales but the larger threat are the mass hacks that remain hidden for a long time. The Yahoo hacks from 2012 and 2014 remained unknown to the public until 2016. We can assume that the best hackers don’t get caught.
The whole of society seems keen on ignoring cyber-security. The debate between Donald Trump and Hillary Clinton proved that both candidates lack a coherent approach for cyber defense. The cyber-warfare between the USA, Russia, China, and other nations is a publicly kept secret. Since there’s no accountability for this type of hacking, most superpowers do it on a massive scale.
The future is very uncertain for the cyber security. The best approach for strengthening Internet safety would keep Web freedom intact. However, it seems more likely that we’ll either see a more restricted, less free Internet, or a wild-west style wasteland of data.



