The DarkLocker ransomware is a scareware malware virus which is also known under the alias of Monument ransomware, you can remove infections by reading our guide.
DarkLocker Ransomware Description
The DarkLocker ransomware is a new virus threat that belongs to the scareware group of malware. It is also known under the alias of Monument ransomware and it has been developed by an unknown hacker or collective.
Like other similar threats it attempts to scare its victims and make them pay a ransomware fee even though the virus does no harm to their data in the current iteration. The security analysis shows that the hacker(s) behind it has/have not included any dangerous modules which are found in advanced forms of ransomware. Examples include the following:
- Payload Downloader – The virus engine can be used to deliver other virus threats to infected host./span>
- Remote Control – Hackers can overtake remote control of the computers if the virus engine includes a Trojan component.
- Information Harvesting – The virus can extract and send arbitrary user data to the remote hackers, as well as system information and stored account credentials, web search history, cookies and other cache from the installed browsers and applications.
- Persistence Creation – The virus engine can setup a persistent state of infection which can prevent the malware from being removed by manual means. Such malware threats can only be removed using a quality anti-malware security solution.
- System Modification – In several cases the virus may opt to change important settings which may cause problems to the stability of the operating system, lower its performance or cause application errors.
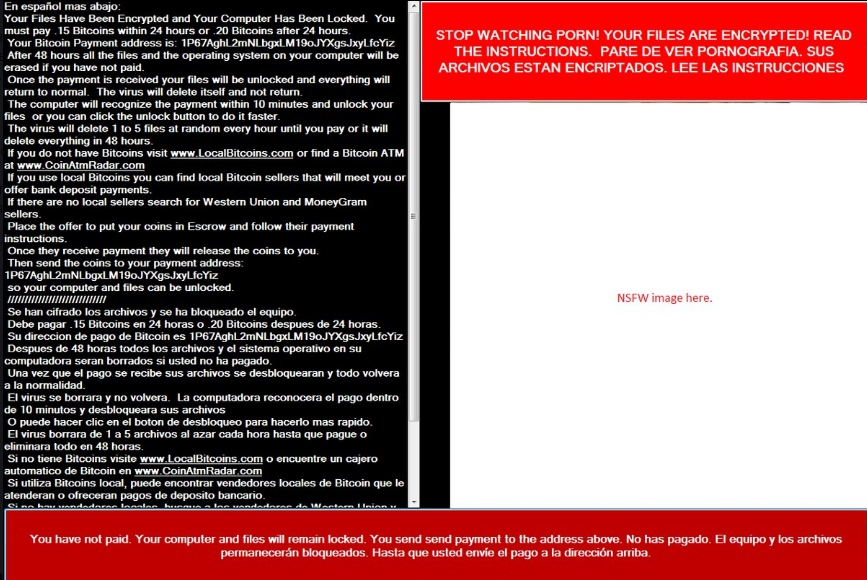
Upon infection the DarkLocker ransomware modifies key Windows settings which institute a screenlocker – a feature which prevents ordinary user interaction with the affected computer. The users can only restore access to the computer if the virus is removed. Due to the fact that Darklocker ransomware has caused system modification an efficient removal is possible only by using a quality anti-spyware solution. The following ransomware note is displayed to the victims:
STOP WATCHING PORN! YOUR FILES ARE ENCRYPTED! READ THE INSTRUCTIONS.
PARE DE VER PORNOGRAFIA. SUS ARCHIVOS ESTAN ENCRIPTADOS. LEE LAS INSTRUCCIONES
En espanol mas abajo:
Your Files Have Been Encrypted and Your Computer Has Been Locked. You must pay .15 Bitcoins within 24 hours or .20 Bitcoins after 24 hours.
Your Bitcoin Payment address is: 1 P67AghL2mNLbgxLM 19oJYXgsJxyLfcYiz
After 48 hours all the files and the operating system on your computer will be erased if you have not paid.
Once the payment is received your files will be unlocked and everything will return to normal. The virus will delete itself and not return.
The computer will recognize the payment within 10 minutes and unlock your files or you can click the unlock button to do it faster.
The virus will delete 1 to 5 files at random every hour until you pay or it will delete everything in 48 hours.
If you do not have Bitcoins visit www.LocalBitcoins.com or find a Bitcoin ATM at www.CoinAtmRadar.com
If you use local Bitcoins you can find local Bitcoin sellers that will meet you or offer bank deposit payments.
If there are no local sellers search for Western Union and MoneyGram sellers.
Place the offer to put your coins in Escrow and follow their payment instructions.
Once they receive payment they will release the coins to you.
Then send the coins to your payment address:
1P67AghL2mNLbgxLM 19oJYXgsJxyLfcYiz
so your computer and files can be unlocked.
//////////
Se han cifrado los archivos y se ha bloqueado el equipo.
Debe pagar .15 Bitcoins en 24 horas o .20 Bitcoins despues de 24 horas.
Su dirección de pago de Bitcoin es 1P67AghL2mNLbgxLM19oJYXgsJxyLfcYiz
Despues de 48 horas todos los archivos y el sistema operativo en su computadora serán borrados si usted no ha pagado.
Una vez que el pago se recibe sus archivos se desbloquearan y todo volverá a la normalidad.
El virus se borrara y no volverá. La computadora reconocerá el pago dentro de 10 minutos y desbloqueara sus archivos.
O puede hacer dic en el boton de desbloqueo para hacerlo mas rápido.
El virus borrara de 1 a 5 archivos al azar cada hora hasta que pague o eliminara todo en 48 horas.
Si no tiene Bitcoins visite vyww.LocalBitcoins.com o encuentre un cajero automático de Bitcoin en www CoinAtmRadar.com
Si utiliza Bitcoins local, puede encontrar vendedores locales de Bitcoin que le atenderan o ofrecerán pagos de deposito bancarío…
—–
You have not paid. Your computer and files will remain locked. You send send payment to the address above No has pagado. El equipo y los archivos
permanecerán bloqueados Hasta que usted envíe el pago a la dirección arriba.Перевод текста на русский язык:
ПЕРЕСТАНЬТЕ СМОТРЕТЬ ПОРНО! ВАШИ ФАЙЛЫ ЗАШИФРОВАНЫ! ЧИТАЙТЕ ИНСТРУКЦИИ.
Ваши файлы были зашифрованы, а ваш компьютер заблокирован. Вы должны заплатить 0.15 биткоинов за 24 часа или 0.20 биткойнов через 24 часа.
Ваш биткойн-адрес для оплаты: 1P67AghL2mNLbgxLM 19oJYXgsJxyLfcYiz
Через 48 часов все файлы и операционная система на вашем компьютере будут удалены, если вы не заплатили.
Как только платеж будет получен, ваши файлы будут разблокированы, и все вернется к норме. Вирус удалит себя и не вернется.
Компьютер распознает платеж в течение 10 минут и разблокирует ваши файлы, или вы можете нажать кнопку разблокировки, чтобы сделать это быстрее.
Вирус удаляет от 1 до 5 файлов наугад каждый час, пока вы не заплатите, или он удалит все за 48 часов.
Если у вас нет биткоинов, посетите www.LocalBitcoins.com или найдите биткойн-банкомат на сайте www.CoinAtmRadar.com
Если вы используете локальные биткоины, вы можете найти местных продавцов биткоинов, которые будут вам предлагать банковские депозитные платежи.
Если местные продавцы не ищут продавцов Western Union и MoneyGram.
Разместите оферту, чтобы положить ваши монеты в Escrow и следовать их платежным инструкциям.
Как только они получат оплату, они выпустят вам монеты.
Затем отправьте монеты на свой платежный адрес:
1P67AghL2mNLbgxLM 19oJYXgsJxyLfcYiz
После этого ваш компьютер и файлы могут быть разблокированы.
—–
Вы не заплатили. Ваш компьютер и файлы останутся заблокированными. Отправьте платеж по указанному выше адресу.
The note is written in several languages which means that the hackers behind the threat distribute it globally around the world and seek to have a large infection ratio. The displayed message uses a widely used social engneering trick which scares the users into thinking that they have come in contact with the infection after interacting with adult content. To increase pressure on them the hackers state that they are going to delete random files at a set period of time until the ransomware fee is paid.
DarkLocker Ransomware Distribution
The DarkLocker ransomware is distributed mainly through several binary executable files. At this moment there are only a very limited number of samples available and most of them carry the virus load in a RTInstaller.exe file. As the malware is distributed globally we suspect that the following infection strategies are employed:
- Download Sites And P2P Networks – The virus files are distributed on various hacked or hacker-controlled download portals and on P2P networks like BitTorrent where they pose as installers for well-known applications such as programs, games, utilities and etc.
- Email Spam – Bulk email spam waves can be used to link to the hacker-controlled sites or attach the binaries directly to the messages. As always various phishing strategies are the most commonly used tactics. The hackers can also use infected Office documents which contain malicious macros that lead to the infection.
- Exploit Kits & Direct Attacks – Automated vulnerability testing made by exploit kits and direct hacker attacks can also lead to an infection with the Darklocker ransomware.
Summary of DarkLocker Ransomware
| Name |
DarkLocker Ransomware |
| File Extensions |
Does not affect files |
| Ransom |
0.15-0.20 Bitcoins |
| Easy Solution |
You can skip all steps and remove DarkLocker Ransomware ransomware with the help of an anti-malware tool. |
|
Manual Solution |
DarkLocker Ransomware ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Spam Email Campaigns, malicious ads & etc. |
DarkLocker Ransomware Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely DarkLocker Ransomware Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover DarkLocker Files
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How To Restore DarkLocker Files
- 1) Use present backups
- 2) Use professional data recovery software
-
– Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



