CryptoShield 2.0 Ransomware is the latest iteration of the CryptoShield family of viruses which is also known under the alias of Protected SoftWare, continue reading our removal guide to learn more about it.
CryptoShield 2.0 Ransomware Description
The CryptoShield 2.0 Ransomware is the latest evolution of the CryptoShield family of viruses. The malware is also known under the alias of Protected SoftWare.
Like its predecessors the virus uses the standard behavior patterns of related malware by encrypting target user data and then extorting the victims for a ransomware payment.
The affected files include the most common file types – documents, photos, music, videos, configuration files, backup images and etc. All of the affected data is renamed using a set pattern – .[[email protected]].ID[2D64A0776C78A9C3].CRYPTOSHIELD.
As well as affecting the user’s data the virus also modifies several system settings:
- The ransomware disables the Windows Recovery Options.
- The virus code deletes all Volume Shadow Copies found on the infected host. This makes data recovery difficult unless a professional solution is used.
- The virus disables Windows Error Recovery Mechanisms.
- The ransomware also sets up a persistent environment for itself by executing when the computer boots.
- The malware can kill other processes and manipulate various other system processes.
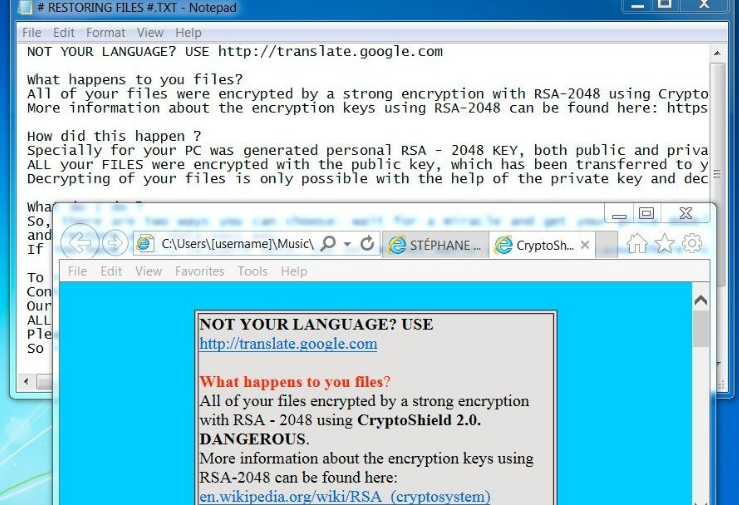
The CryptoShield 2.0 Ransomware’s encryption engine uses the AES cipher. When the encryption process is complete the following ransomware is shown to the user:
NOT YOUR LANGUAGE? USE http://translate.google.com
What happens to you files?
All of your files were encrypted by a strong encryption with RSA-2048 using CryptoShield 2.0. DANGEROUS.
More information about the encryption keys using RSA-2048 can be found here: https://en.wikipedia.org/wiki/RSA_(cryptosystem)
How did this happen ?
Specially for your PC was generated personal RSA – 2048 KEY, both public and private. ALL your FILES were encrypted with the public key, which has been transferred to your computer via the Internet. Decrypting of your files is only possible with the help of the private key and decrypt program , which is on our secret server.
What do I do ?
So, there are two ways you can choose: wait for a miracle and get your price doubled, or start send email now for more specific instructions, and restore your data easy way. If You have really valuable data, you better not waste your time, because there is no other way to get your files, except make payment.
To receive your private software:
Contact us by email , send us an email your (personal identification) ID number and wait for further instructions. Our specialist will contact you within 24 hours.
ALL YOUR FILES ARE ENCRYPTED AND LOCKED, YOU CAN NOT DELETE THEM, MOVE OR DO SOMETHING WITH THEM. HURRY TO GET BACK ACCESS FILES. Please do not waste your time! You have 72 hours only! After that The Main Server will double your price!
So right now You have a chance to buy your individual private SoftWare with a low price!
CONTACTS E-MAILS:
[email protected] – SUPPORT;
[email protected] – SUPPORT RESERVE FIRST;
[email protected] – SUPPORT RESERVE SECOND;
ID (PERSONAL IDENTIFICATION): 9694E***
CryptoShield 2.0 Ransomware Distribution
The CryptoShield 2.0 Ransomware is distributed mainly by exploit kits and spam messages. Infections have been detected as originating from fake messages and infected software bundles.
The criminals have also used other dangerous methods such as malicious JavaScript files and exploit kits (mainly RIG and ElTest). The virus can also be found on hacked sites and malicious ads.
A lot of infections have been made using the ElTest exploit kit which has compromised a large quantity of sites powered by content management systems such as WordPress and Joomla.
Summary
| Name |
CryptoShield 2.0 Ransomware |
| File Extensions |
.[[email protected]].ID[2D64A0776C78A9C3].CRYPTOSHIELD Pattern |
| Ransom |
Varies |
| Easy Solution |
You can skip all steps and remove CryptoShield 2.0 Ransomware ransomware with the help of an anti-malware tool. |
|
Manual Solution |
CryptoShield 2.0 Ransomware ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Spam Email Campaigns, malicious ads & etc. |
CryptoShield 2.0 Ransomware Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely CryptoShield 2.0 Ransomware Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Encrypted Files
-
1) Use present backups
2) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

STEP VII: Preventive Security Measures
-
1) Enable and properly configure your Firewall.
2) Install and maintain reliable anti-malware software.
3) Secure your web browser.
4) Check regularly for available software updates and apply them.
5) Disable macros in Office documents.
6) Use strong passwords.
7) Don’t open attachments or click on links unless you’re certain they’re safe.
8) Backup regularly your data.



