A new virus named AES-NI started infecting users in mid-April 2017. The virus encrypts your files and adds the .aes_ni, .aes_ni_gov, .lock, .aes256, and most recently the .aes_ni_0day extensions. The virus can be removed. Just follow the guide below. Most PC operating systems are at danger.
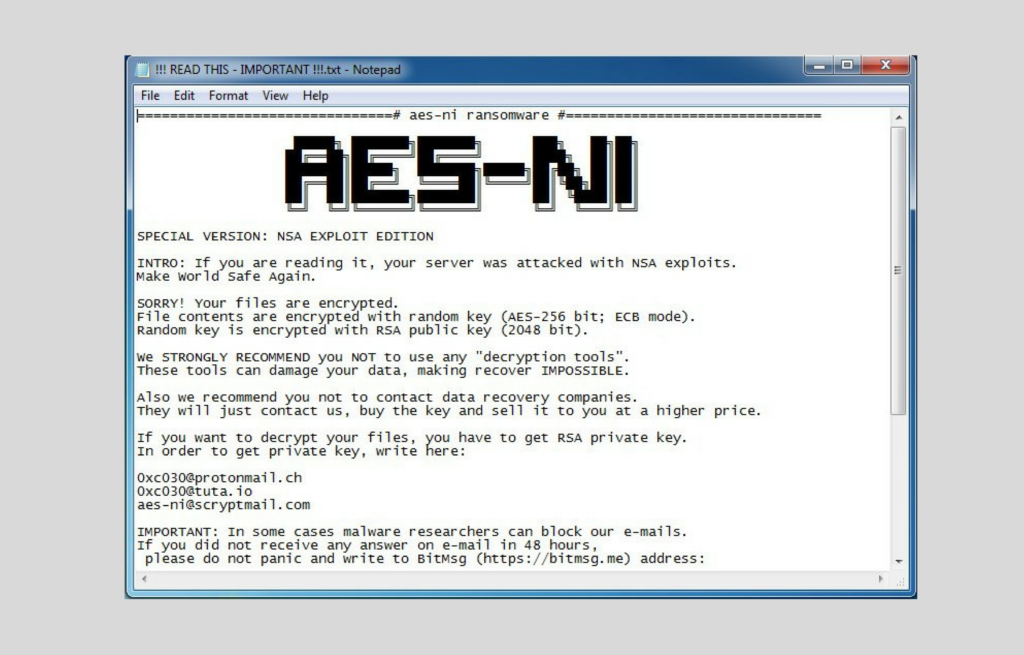
Screenshot from the ransom note of AES-ni:
AES-NI Ransomware Virus – How Did It Infect Me?
The virus will drop its infectious content in one of the following ways:
- Emails Spam – The crooks send out legit-looking emails that mask themselves as real companies – PayPal, FedEx, Microsoft, and others. In those letters hides an attachment. This attachment will infect your PC if you download and open it.
- Clickbait scamming – some sites will include weird advertisements that may be tempting for some users to open. Once you click on them, the files carrying the AES-NI ransomware virus will be dropped onto your PC. If that happens, delete them ASAP, preferably with the help of an anti-malware tool.
AES-NI Ransomware Virus Infection – How Does It Work?
The AES-NI virus will encrypt your files using the AES encryption algorithm. This will effectively lock your files. To unlock them, you’ll need a key that’s located in the “C:\ProgramData” folder of your computer.
The virus will drop this ransom message file – “!!! READ THIS – IMPORTANT !!!.txt”
Here’s the note’s content:
“SPECIAL VERSION: NSA EXPLOIT EDITION
INTRO – If you are reading it, your server was attacked with NSA exploits.
Make World Safe Again.
SORRY! Your files are encrypted.
File contents are encrypted with random key (AES-256 bit; ECB mode).
Random key is encrypted with RSA public key (2048 bit).
We STRONGLY RECOMMEND you not use any “decryption tools”.
These tools can damage your data, making recover IMPOSSIBLE.
Also we recommend you not to contact data recovery companies.
They will just contact us, buy the key and sell it to you at a higher price.
If you want to decrypt your files, you have to get RSA private key.
In order to get private key, write here:
[addresses] IMPORTANT: In some cases malware researchers can block our emails.
If you did not receive any answer on email in 48 hours ,
Please do not panic and write to [address]. „
The ransomware scammers are lying – recovery companies are unlikely to contact the scammers and sell you the key at a higher price. It’s best to avoid contacting the scammers and delete the virus by other means.
AES-NI Ransomware Virus Deletion – How To Remove?
The virus can be removed by hand, or with the help of an anti-malware tool. The first option is tricky, as malicious files from AES-NI may linger in your computer. This is why it’s best to:
- Download the Tool:
- Scan your system.
- Remove The Virus.
AES-NI Ransomware Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely AES-NI Ransomware Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Encrypted Files
- 1) Use present backups
- 2) Use professional data recovery software
-
– Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
STEP VII: Preventive Security Measures
-
1) Enable and properly configure your Firewall.
2) Install and maintain reliable anti-malware software.
3) Secure your web browser.
4) Check regularly for available software updates and apply them.
5) Disable macros in Office documents.
6) Use strong passwords.
7) Don’t open attachments or click on links unless you’re certain they’re safe.
8) Backup regularly your data.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



