The .diablo6 file virus is one of the newest active strains of the infamous Locky ransomware virus. The Locky ransomware family continues to evolve as new variants and attack campaigns continue to be launched at various targets. Computer security analysts have spotted a new malware threat that is believed to be a new iteration of the dangerous Locky ransomware family.
Manual Removal Guide
Recover .diablo6 Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How Does .diblo6 File Virus Infiltrate the System?
The .diablo6 file virus is distributed with the help of email spam letters, most likely sent with the help of Necurs, an infamous botnet. The Locky infected emails contain malicious .ZIP files. Spreading ransomware through archives is a staple of this type of malware. The ZIP file contains malicious VBS file that once opened triggers the Locky ransomware infection.
Major changes in the big ransomware families occur with new naming schemes. Locky is a reference to Loki, the Norse Trickster God and Aesir is one of the two main groups of Deities in the Norse Pantheon.
Infection Flow of .Diablo6 File Virus
Malware researchers have just uncovered a new variant of the Locky malware family called .diablo6 file virus. The new strain uses the malicious .diablo6 extension to label the compromised files.
According to the initial analysis, it has already been used in live attack campaigns against various users. Some of the code has also been modified to avoid detection by security software.
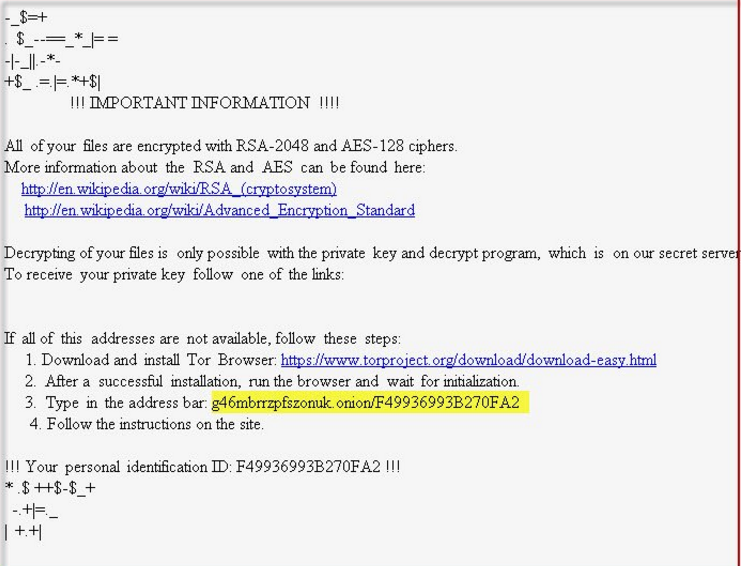
The ransom note shows the following message to the victims:
*+=$.$|| _.
+*++\=$_*
+=$++ |*|$+ $|*
!!! IMPORTANT INFORMATION !!!All of your files are encrypted with RSA-2048 and AES-128 ciphers.
More information about the RSA and AES can be found here:
http://en.wikipedia.org/wiki/RSA_(cryptosystem)
http://en.wikipedia.org/wiki/Advanced_Encryption_StandardDecrypting of your files is only possible with the private key and decrypt program, which is on our secret server
To receive your private key follow one of the links:If all of this addresses are not available, follow these steps:
1. Download and install Tor Browser: https://www.torproject.org/download/download-easy.html
2. After a succesful installation, run the browser and wait for initialization.
3. Type in the address bar: g46mbrrzpfszonuk.onion/{ID}
4. Follow the instructions on the site.!!! Your personal identification ID: {ID}
*|*=$=+$ $*.*|$=
_$=$ $|+
*=*=++ -|-_*-.-
+=__.-+$ $-+
When victims enter the Locky decryptor page via the TOR browser they can see the following:
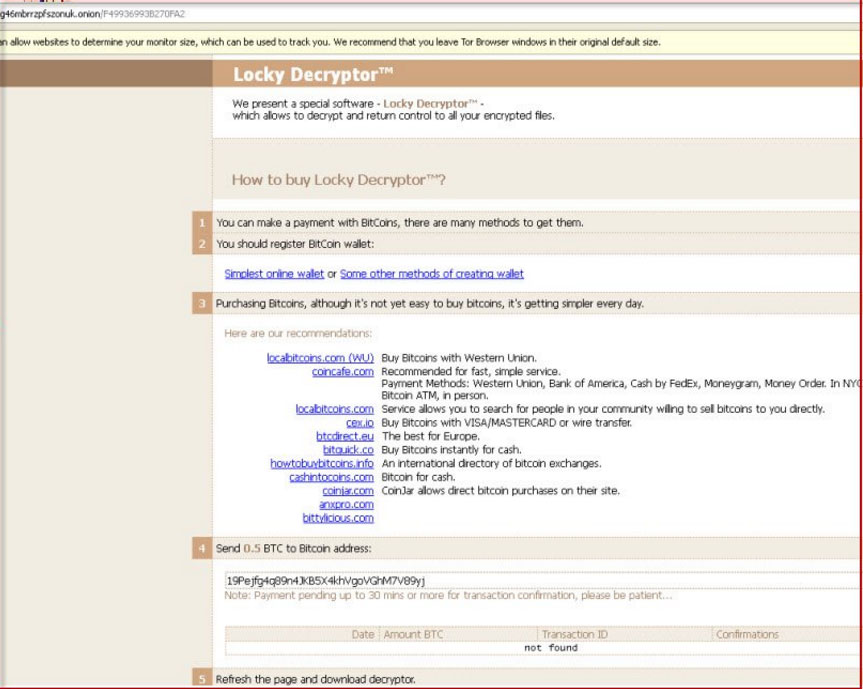
It is known that the ransomware authors want a payment of 0.5 Bitcoin, which equals to nearly 1650 US dollars at the moment of writing this article. It is likely to target the following list of file extensions:
.js, .iwi, .cer, .der, .x3f, .srw, .pef, .ptx, .r3d, .rw2, .rwl, .raw, .raf, .orf, .nrw, .mrwref, .mef, .erf, .kdc, .dcr, .cr2, .crw, .sr2, .srf, .bay, .arw, .3fr, .dng, .jpe, .jpg, .cdr, .indd, .ai, .eps, .pdf, .pdd, .pptx, .psd, .dbf, .mdf, .wb2, .rtf, .wpd, .dxg, .xf, .dwg, .pst, .accdb, .mdb, .pptm, .ppt, .xlk, .p7b, .xlsm, .xlsb, .xlsx, .xls, .wps, .docm, .docx, .doc, .odb, .odc, .odm, .odp, .ods, .odt. .kdb, .db0, .dba, .rofl, .hkx, .upk, .das, .litemod, .asset, .ltx, .apk, .re4, .sav, .lbf, .slm, .bik, .epk, .rgss3a, .pak, .big, wallet, .wotreplay, .xxx, .py, .m3u, .flv, .css, .rb, .png, .jpeg, .txt, .p7c, .p12, .pfx, .pem, .crt, .sql, .7z, .rar, .m4a, .wma, .avi, .wmv, .csv, .d3dbsp, .zip, .sie, .sum, .t13, .t12, .qdf, .gdb, .pkpass, .bc6, .bc7, .bkp, .qic, .bkf, .sidn, .mddata, .itl, .itdb, .icxs, .hvpl, .hplg, .hkdb, .mdbackup, .bar, .ibank, .desc.
The .diablo6 file virus a.k.a Locky ransomware encrypts data by utilizing combination of two strong cipher algorithms RSA and AES. All corrupted files reveive the maliciou sextension .diablo6 and become completely inaccessible after encryption.
Remove .diblo6 File Virus and Restore Data
WARNING! Manual removal of .diblo6 File Virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
.diblo6 File Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover .diblo6 Files
WARNING! All files and objects associated with .diblo6 File Virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
DOWNLOAD .diblo6 File Virus Removal ToolSpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



