The Lock2017 Ransomware is a new malware threat which encrypts target user files and renames them using two template extensions – [file_name.file_ext].id-[UserID][email protected][email protected] or [file_name.file_ext].id-[UserID]__contact_me_[ransom_email]. You can remove existing infections by following our in-depth removal guide below.
Lock2017 Ransomware Description
The Lock2017 ransomware is a newly discovered malware threat which can cause severe damage to any infected host. The virus has an encryption engine which affects the most popular user data files using a strong cipher, a combination of both the AES and RSA methods. As always the criminal operators extort the victims for a ransomware payment to restore access to the compromised data. Security experts strongly recommend that all victims use a quality anti-malware tool to remove infections, do not pay the ransom fee and do not contact the hackers. In many cases the criminals behind the viruses extort the victims and even if the requested sum is paid, they do not always fully decrypt the files or remove the malware completely. This particular threat is of unknown origin and it still under analysis. The malware researchers have discovered that upon infection it assigns an unique ID to each host. This is then used by the encryption engine which targets the most popular user data files and uses a strong cipher. Depending on the version of the threat and several variables the virus may use one of these two extensions:
- [file_name.file_ext].id-[UserID][email protected][email protected]
- [file_name.file_ext].id-[UserID]__contact_me_[ransom_email]
The encryption engine targets the most popular files – documents, databases, configuration files, photos, music, video and etc. The virus uses a combination of the AES and RSA ciphers.
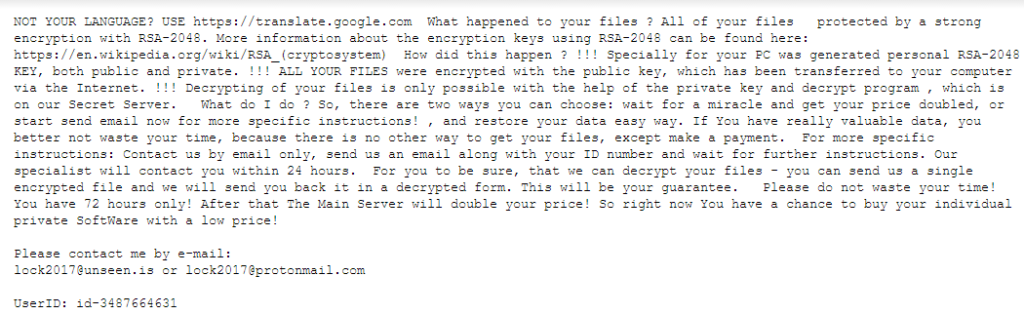
After the encryption process is complete a ransomware note is crafted in the file – README.TXT which has the following contents:
NOT YOUR LANGUAGE? USE https://translate.google.com
What happened to your files?
All of your files protected by a strong encryption with RSA-2048. More information about the encryption keys using RSA-2048 can be found here: https://en.wikipedia.org/wiki/RSA_(cryptosystem)
How did this happen?
!!! Specially for your PC was generated personal RSA-2048 KEY, both public and private.
!!! ALL YOUR FILES were encrypted with the public key, which has been transferred to your computer via the Internet.
!!! Decrypting of your files is only possible with the help of the private key and decrypt program, which is on our Secret Server.
What do I do ?
So, there are two ways you can choose: wait for a miracle and get your price doubled, or start send email now for more specific instructions! , and restore your data easy way. If You have really valuable data, you better not waste your time, because there is no other way to get your files, except make a payment. For more specific instructions:
Contact us by email only, send us an email along with your ID number and wait for further instructions. Our specialist will contact you within 24 hours.
For you to be sure, that we can decrypt your files – you can send us a single encrypted file and we will send you back it in a decrypted form. This will be your guarantee.
Please do not waste your time! You have 72 hours only! After that The Main Server will double your price! So right now You have a chance to buy your individual private SoftWare with a low price!
Please contact me by e-mail:
[email protected] or [email protected]
UserID: id-3487664600
As the in-depth analysis is not yet complete we do not have information if the virus engine contains additional modules. They may include one of the following:
- Payload Delivery – The virus may infect the hosts with additional threats such as banking trojans.
- Persistence – Viruses of this type have the ability to create a persistent environment upon infection. They modify the system so that they can run every time the computer boots and all security software is disabled. This makes manual removal methods useless.
- Computer Interaction Prohibition – Malware infections can prohibit user interaction with the computer by using screenlockers for example.
- System Damage – Viruses like the Lock2017 ransomware can impose dangerous system changes which can make the operating system unable to boot.
Lock2017 Ransomware Distribution
The virus was first identified in the beginning of March 2017. As the malware samples are still very limited the experts have not been able to deduce the main method of infection. However we presume that the criminals behind it utilize the most popular ones which include the following:
- Bulk Emails – Email messages that employ social engineering tricks (so called phishing scams) which design the emails in a way that resembles legitimate institutions.
- Download Sites and P2p Networks – The viruses can often be found masquerading as popular applications, games, updates or patches on download sites or P2P networks like BitTorrent trackers.
- Dangerous Scripts – Browser hijackers and malicious ad networks can often lead the victims into downloading virus samples. The ad networks are usually placed in hacked and hacker-controlled sites. Dangerous browser extensions can invade the privacy of the users by harvesting the stored accounts, passwords and history. They can also spy on the users activity and transmit information to the remote attackers. Most hijackers change the default search engine, new tabs page and homepage to hacker-controlled ones which distribute virus links.
- Exploit Kits – Automated attacks can cause the ransomware infection when a succesful intrusion has been made.
Summary of the Lock2017 Ransomware
| Name | Lock2017 Ransomware |
| File Extensions | Based on the following templates – [file_name.file_ext].id-[UserID][email protected][email protected] or [file_name.file_ext].id-[UserID]__contact_me_[ransom_email]. |
| Ransom | Varies |
| Easy Solution | You can skip all steps and remove Lock2017 Ransomware ransomware with the help of an anti-malware tool. |
| Manual Solution | Lock2017 Ransomware ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution | Spam Email Campaigns, malicious ads & etc. |
Lock2017 Ransomware Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
- 1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
- 1) Open My Computer/This PC
2) Windows 7
- – Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
- – Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
- 1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely Lock2017 Ransomware Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
- 1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Encrypted Files
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How To Restore RedAnts Files
- 1) Use present backups
- 2) Use professional data recovery software
- – Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
- – Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
- – Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



