Salsa ransomware is a malware that penetrates the system to encrypt personal user data and allow hackers to blackmail victims for ransom. Once Salsa payloads land on the computer they activate the malicious executable files that are designed to perform various system modifications and malicious commands, create and download files, encrypt files and then append them the .salsa222 extension. The threat is likely to be spread almost worldwide as the ransom note READ TO UNLOCK FILES.salsa.[language].html is translated in 40 languages.
In this article, we will look closer at Salsa ransomware features and reveal consistent instructions on its removal. Furthermore, STEP VI: Recover Encrypted Files from the Salsa removal guide shows information on alternative .salsa222 data recovery approaches so don’t hurry with the ransom payment which is 0.124831 Bitcoins.
Salsa Ransomware in Detail
The infection process of Salsa crypto virus is triggered by an executable file that is most likely to be called SalsaDownload.exe. The file has strings that initiate the enforcement of various malicious actions.
The threat has the capability to carry out a scan of all computer drives to find all files set to its target list. Each time there is a file type match, Salsa ransomware utilizes strong encipher algorithm and encrypts the file. Afterward, the corrupted data receive the extension .salsa222 and becomes inaccessible without the unique decryption key. Let’s guess that there is a file analysis.doc stored on the desktop, after Salsa ransomware encryption the file will be renamed to analysis.doc.salsa222 and no program installed on the PC will be able to open it. The most commonly used file types on the Windows OS are likely to be encrypted:
.jpeg, .jpg, .mp3, .mp4, .pdf, .php, .ppt, .pptx, .rar, .rtf, .sql, .tiff, .txt, 7z, .bmp, .doc, .docm, .docx, .html, .xls, .xlsx, .zip
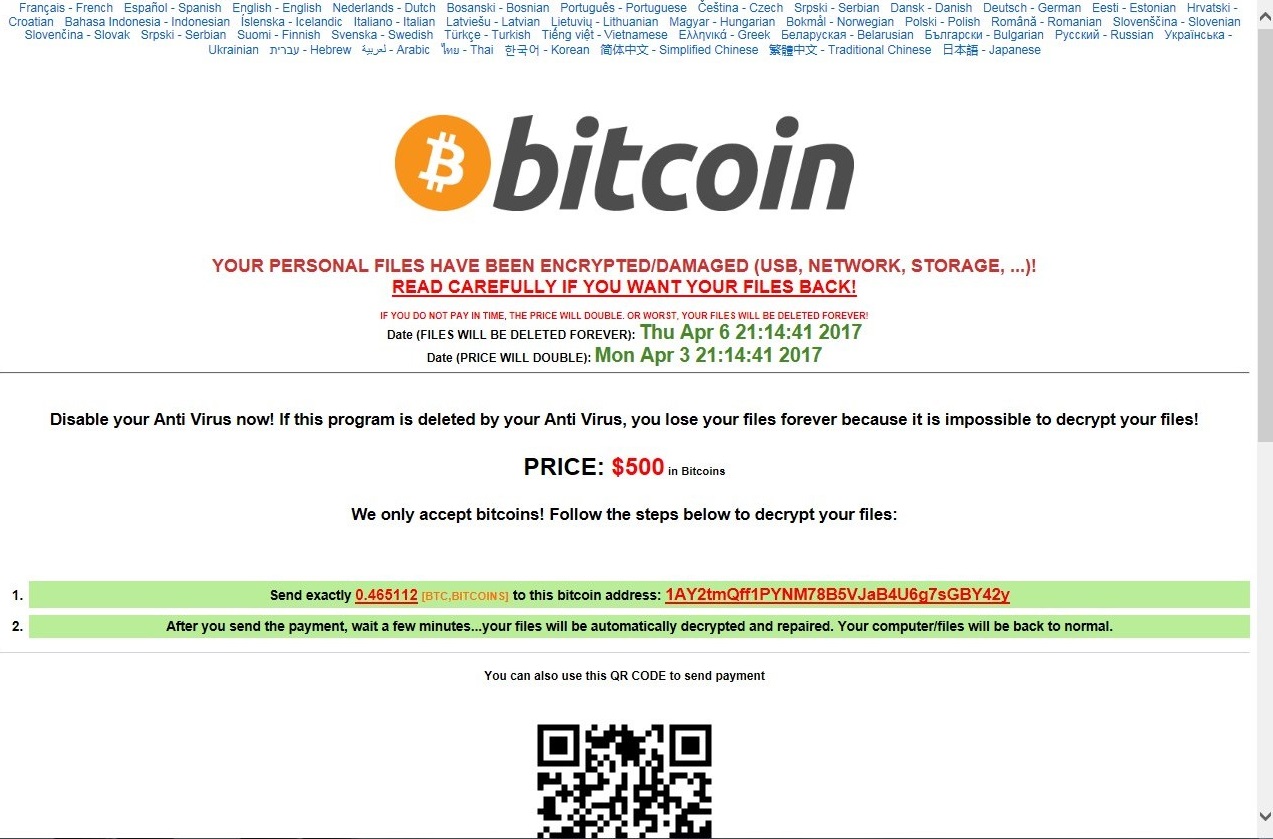
At this point, it is not clear whether Salsa is programmed to implement a symmetric or an asymmetric algorithm for data decryption. It is sure, however, that hackers store the decryption key on a remote server and extort victims for ransom. The ransom is $500 in Bitcoins (at this point the amount is 0.42059 BTC).
The message from hackers to victims is placed in a newly created folder Click here to Unlock your files Salsa222 under the name READ TO UNLOCK FILES.salsa.[language].html. The ransom note is translated into 40 languages, and all users who are from countries where these languages are spoken are likely Salsa ransomware targets. The list of all languages includes:
French; Spanish; English; Hindi; Dutch; Bosnian; Portuguese; Czech; Serbian; Danish; German; Bengali; Estonian; Croatian; Persian; Indonesian; Icelandic; Italian; Kannada; Norwegian; Tamil; Polish; Urdu; Romanian; Slovenian; Slovak; Malayalam; Finnish; Swedish; Marathi; Turkish; Gujarati; Arabic; Thai; Korean; Simplified Chinese; Traditional Chinese; Russian; Telugu; Ukrainian; Hebrew; Japanese; Javanese; ; Latvian; Lithuanian; Hungarian; Vietnamese; Greek; Belarusian; Bulgarian
All that it reads in English is:
YOUR PERSONAL FILES HAVE BEEN ENCRYPTED/DAMAGED (USB, NETWORK, STORAGE, …)!
READ CAREFULLY IF YOU WANT YOUR FILES BACK!
IF YOU DO NOT PAY IN TIME, THE PRICE WILL DOUBLE. OR WORST, YOUR FILES WILL BE DELETED FOREVER!
Date (FILES WILL BE DELETED FOREVER): Thu Apr 6 21:14:41 2017
Date (PRICE WILL DOUBLE): Mon Apr 3 21:14:41 2017
Disable your Anti Virus now! If this program is deleted by your Anti Virus, you lose your files forever because it is impossible to decrypt your files!
PRICE: $500 in Bitcoins
We only accept bitcoins! Follow the steps below to decrypt your files:
1.Send exactly 0.465112 [BTC,BITCOINS] to this bitcoin address: 1AY2tmQff1PYNM78B5VJaB4U6g7sGBY42y
2.After you send the payment, wait a few minutes…your files will be automatically decrypted and repaired. Your computer/files will be back to normal.
You can also use this QR CODE to send payment
How to Send Bitcoins?
Step 1
Click one of the following links to Register a Bitcoin Wallet: Blockchain.info, CoinBase.com, StrongCoin.com
Step 2
Click one of the following links to Purchase Bitcoins: LocalBitcoins.com (CASH, WESTERN UNION, PAYPAL, …), CoinATMRadar.com (CASH, ATM), CoinBase.com (BANK ACCOUNT, CREDIT CARD), CoinMama.com (CREDIT CARD, WESTERN UNION…)
Step 3
Send exactly 0.465112 [BTC,BITCOINS] to this bitcoin address: 1AY2tmQff1PYNM78B5VJaB4U6g7sGBY42y
Paid, and not seeing your files yet?
• Verify that you paid the correct amount
• Make sure your computer is connected to the internet
• Reconnect all infected drives/usb/devices to your computer
If nothing worked, restart your computer, disable your anti-virus and re-download the salsa decryptor from one of these links:
Download Server 1, Download Server 2, Download Server 3, Download Server 4, Download Server 5
The malicious file SalsaDownload.exe also has a strain that drops an image file bg222salsa.jpg. Via additional registry modifications bg222salsa.jpg file replaces the current desktop wallpaper and victim observes an image that depicts the following text:
SALSA
PERSONAL FILES ENCRYPTED
The analyses of the malicious executable file that infects users with Salsa ransomware reveal that the threat is designed in a way that grants it to make changes in Windows registry. So it creates new values in the following sub-key:
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
Changes in the RUN key grant the ransomware to auto-execute its malicious payloads on every Windows boot-up.
Furthermore, Salsa ransomware deletes the Shadow Volume Copies from the Windows Operating System by executing the following command:
vssadmin.exe delete shadows /all /Quiet
This command is initiated in order to eliminate one of the possible decryption ways.
Ransomware Intrusion Techniques
The most common social engineering trick used by the hackers is spreading of spammed emails. The senders may impersonate legitimate sources like your bank, your electricity provider, your colleague even a friend of yours. Always think twice before further actions with emails that contain links, buttons, attachments or a combination of these components. Usually, the crooks skillfully corrupt these components by injecting the malware code into them so once they receive access to the browser or computer the infection with Salsa ransomware starts unnoticeably.
Except emails, the social networks are yet another place where crooks may be spreading the malicious Salsa payloads. The threat may be hidden in links with clickbait content, a video thumbnail or even a compromised file send in a private message.
Remove Salsa Ransomware and Decrypt .Salsa222 Virus Files
Even if the insane ransom is paid, there is no guarantee that the extortionists will send the right decryption key that will restore encrypted data.
For the sake of your security, it’s better to avoid any negotiations with the criminals. However, there is no doubt that you should remove Salsa ransomware from the infected computer in order to continue its regular usage. If you skip the removal step, the malicious payloads of Salsa will be running on your system each time you start the PC. Thus all of your new files that are among ransomware target list will also be encrypted. Below you could find detailed removal guide and choose your way to remove the ransomware completely.
We also recommend you to make copies of all encrypted files and store them in a backup before you make any attempts to restore your data. So you can save them until a working decryption solution is available.
Summary of Salsa Ransomware
| Name | Salsa Ransomware |
| File Extension | .salsa222 |
| Ransom | $500 (0.124831 BTC) |
| Easy Solution | You can skip all steps and remove Salsa ransomware with the help of an anti-malware tool. |
| Manual Solution | Salsa ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution | Spam emails, malicious URLs, malicious attacments, exploit kits, freeware. |
Salsa Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
- 1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
- 1) Open My Computer/This PC
2) Windows 7
- – Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
- – Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
- 1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely Salsa Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
- 1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Encrypted Files
- 1) Use present backups
- 2) Use professional data recovery software
- – Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
- – Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
- – Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
STEP VII: Preventive Security Measures
- 1) Enable and properly configure your Firewall.
2) Install and maintain reliable anti-malware software.
3) Secure your web browser.
4) Check regularly for available software updates and apply them.
5) Disable macros in Office documents.
6) Use strong passwords.
7) Don’t open attachments or click on links unless you’re certain they’re safe.
8) Backup regularly your data.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



