An infection with the dangerous GandCrab 5 ransomware virus leads to serious security issues. With our removal guide, victims can try to restore and protect their computers.
Manual Removal Guide
Files Recovery Approaches
Skip all steps and download anti-malware tool that will safely scan and clean all harmful files it detects on your PC.
SpyHunter is a Windows application designed to scan for, identify, remove and block malware, potentially unwanted programs (PUPs) and other objects. By purchasing the full version, you will be able to remove detected malware instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Distribution of GandCrab 5 Ransomware
The GandCrab 5 ransomware is an extremely dangerous infection which uses several main tactics in order to spread to the intended targets.
The ransomware samples typically use a bulk mechanism for spreading phishing messages such as the RIG exploit kit. The users will receive emails that are designed to appear like typical notifications sent by companies or services that they use. The GandCrab 5 ransomware samples can be directly attached or linked in the body.
To further increase the number of potential infections the criminal group behind the ongoing attacks can create and maintain websites that impersonate official vendor sites and download portals. They also use design elements, similar sounding domain names and even security certificates in order to fool the targets.
Other mechanisms include the inclusion of the GandCrab 5 virus installation code in infected payload carriers. This means that the malware code can be placed by using various files. A widely used mechanism is the creation of infected documents that can be of any of the popular file types: rich text documents, spreadsheets, presentations or databases. Once they are opened a notification prompt will appear asking them to enable the built-in scripts which will trigger the virus installation.
The other payload carrier is the malicious application installer — they criminals can take the legitimate setp file of popular end user programs and modify it with the virus files. This is usually done by taking them directly from the vendor download pages and embedding the relevant code into them. The hackers will primarily target those applications which are used by end users the most: creativity suites, productivity apps and system utilities.
In some cases the hackers can attempt to infect many users by using malicious browser extensions. They are created by the malicious operators in order to fool the users into thinking that they are installing an useful plugin. The various versions are made compatible with the most popular web browsers and uploaded to their respective repositories. Their descriptions often make use of fake developer credentials and user reviews, this is done in order to coerce the victims into installing them. After this is done the majority of the plugins will modify the default settings — home page, new tabs page and search engine. Following this the GandCrab 5 ransomware will be deployed.
According to a security report the ongoing GandCrab 5 ransomware strain may be part of a wider Ransomware-as-a-service model which allows many groups to launch virus attacks using the main virus sample.
Impact of GandCrab 5 Ransomware
The new version of the GandCrab ransomware family follows the behavior pattern set by the previous iterations. It may begin the infection by starting up an information harvesting which will scan the infected computers using an automated method. This component will scan the local computer for strings that are commonly grouped into two main categories:
- Campaign Metrics —This category provides sensitive information that can be used to optimize the ongoing attacks. The hackers will harvest strings such as user settings, operating system values and a report of the installed hardware components.
- Private Information — This part of the module hijacks data that can directly reveal the identity of the victims. An example list of the harvested strings includes their name, address, telephone number, location and any stored accounts.
The GandCrab 5 ransomware may then process the collected information further by initiating a stealth protection module. It will take the collected information and search for any applications or services that can interfere with the proper ransomware operations. Usually this includes all anti-virus engines, sandbox environments and virtual machine hosts. Following this step the virus will have full access to the system, allowing it to create its own processes, gain administrative privileges and etc. A summary of some of the possibilities includes the following:
- Windows Registry Changes — The malicious engine used by the GandCrab 5 ransomware can introduce changes to the Windows registry entries belonging both to the operating system itself or individual applications. This can cause overall performance issues or the inability to launch certain functions or services.
- Persistent Installation The GandCrab 5 ransomware can be set as a persistent threat by the underlying infection engine. This means that the virus infection will be automatically launched when the computer is powered on. This action will have its consequences on other processes and can even disable the recovery boot menu.
- Files Manipulation — The GandCrab 5 ransomware like other popular virus samples may delete the Shadow Volume Copies and System Restore Points created by the operating system. This will make recovery very difficult
Other modules can be called and retrieved by request. When all of then have completed execution the encryption module will be started. It will use a strong cipher in order to target a built-in list of target file type extensions. A typical set of the affected files is the following:
- Archives
- Databases
- Backups
- Images
- Music
- Videos
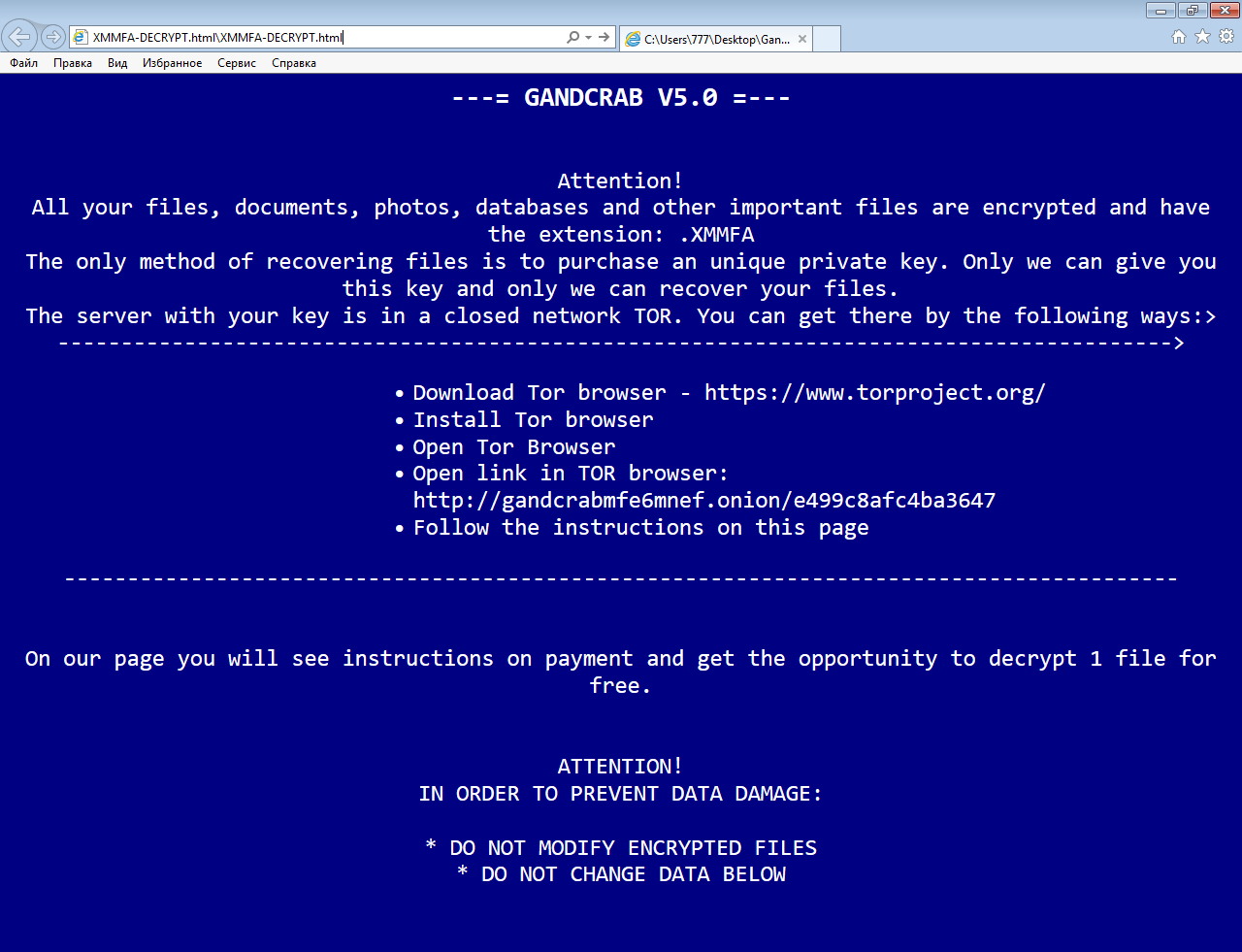
One of the major differences between previous iterations of GandCrab is that the GandCrab 5 ransomware version will append a 5-characters long random extension. The corresponding ransomware note will be crafted using the following formula: [EXTENSION-ID]-DECRYPT.html. One of the prominent feature is that the language of the ransomare note is set to the one used by the users. This mechanism shows that the data obtained obtained during the initial infection is being used throughout all phases of infection.
A sample message contents read the following:
—= GANDCRAB V5.0 =—
Attention! All your files, documents, photos, databases and other important files are encrypted and have the extension: .XMMFA The only method of recovering files is to purchase an unique private key. Only we can give you this key and only we can recover your files. The server with your key is in a closed network TOR. You can get there by the following ways:>
• Download Tor browser – https://www.torproject.org/ • Install Tor browser • Open Tor Browser • Open link in TOR browser: http://gandcrabmfe6mnef.onion/e499c8afc4ba3647 • Follow the instructions on this page
On our page you will see instructions on payment and get the opportunity to decrypt 1 file for free.
ATTENTION! IN ORDER TO PREVENT DATA DAMAGE:
* DO NOT MODIFY ENCRYPTED FILES * DO NOT CHANGE DATA BELOW
Remove GandCrab 5 Ransomware Virus and Restore PC
Please note that paying the requested ransom fee to cyber criminals does not really solve your problem with GandCrab 5 crypto virus. In fact, you only encourage hackers to continue spreading ransomware of this kind. Instead, you must remove the threat immediately, and only then look for optional ways to recover your data.
WARNING! Manual removal of GandCrab 5 ransomware virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
DOWNLOAD SpyHunter Anti-Malware ToolGandCrab 5 Ransomware Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps below are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
- – Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
- – Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover .id.ransomed@india(.)com Files
WARNING! All files and objects associated with GandCrab 5 ransomware virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
SpyHunter is a Windows application designed to scan for, identify, remove and block malware, potentially unwanted programs (PUPs) and other objects. By purchasing the full version, you will be able to remove detected malware instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
- – Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
- – Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



