Malware researchers spotted a Fake WindowsUpdater Ransomware in various sites, read our removal guide to learn more about it.
Fake WindowsUpdater Ransomware Description
A dangerous new malware has been found, security experts identified a new virus known as Fake WindowsUpdater Ransomware, another one of its aliases is the shortened FakeWU Ransomware. According to the initial analysis this is a newly created virus which does not use any source code from some of the already known strains and families. Unfortunately the researchers were not able to learn who is behind its development, we only know that the hacker goes under the alias of FathurFreakz and that the strain has been crafted using the Visual Studio 2010 environment.
It seems that the virus is a basic one which does not feature much advanced options. It is very likely that we will see future evolutions of it that are going to add modules that may include the following:
- Persistence – The virus engine can modify key Windows boot files, registry settings and other values to create an environment where the virus will always run and supress other applications. Such changes also prevent manual recovery, removal is only possible using a quality anti-spyware solution.
- Registry Modification – Modifications to the registry entries may create performance issues, misconfigure applications or render certain operating systems functions unusable.
- Stealth Protection – Evolved ransomware may feature a stealth protection module which can guard the malicious code from anti-spyware and anti-virus products. This is usually achieved either by disabling them via system modifications or bypassing their real-time protection.
- Remote Control – The inclusion of a Trojan component can allow the remote attackers access to the machine in every given moment.
- GIF – A popular raster image file format which supports animation.
- Information Harvest – Some ransomware strains can extract and remotely transmit sensitive information from the affected hosts. They include system information, user data and stored data in browsers and other programs.
- Screenlocker – Such additions prevent the ordinary interaction with the computer. The screenlocker is removed only after the virus has been erased completely from the machine.
The current iteration of the virus launches its built-in encryption engine when the infection has been imposed on the target hosts. The Fake WindowsUpdater Ransomware uses a strong cipher to encrypt a predefined list of file type extensions. At the moment the following ones have been identified as targets:
.#vc, .$ac, ._vc, .00c, .07g, .07i, .08i, .09i, .09t, .10t, .11t, .123, .13t, .1pa, .1pe, .2011, .2012, .2013, .2014, .2015, .2016, .2017, .210, .3dm,
.3ds, .3g2, .3gp, .3me, .3pe, .500, .7z, .aac, .aaf, .ab4, .ac2, .acc, .accd, .ach, .aci, .acm, .acr, .aep, .aepx, .aes, .aet, .afm, .ai, .aif, .amj, .as,
.as3, .asc, .asf, .asm, .asp, .asx, .ati, .avi, .back, .bak, .bat, .bay, .bc8, .bc9, .bd2, .bd3, .bgt, .bk2, .bkf, .bmp, .bpf, .bpw, .brd, .brw, .btif, .bz2,
.c, .cal, .cat, .cb, .cd, .cdf, .cdr, .cdt, .cdx, .cf8, .cf9, .cfdi, .cfp, .cgm, .cgn, .ch, .chg, .cht, .clas, .clk, .cmd, .cmx, .cnt, .cntk, .coa, .cpp, .cpt,
.cpw, .cpx, .crt, .cs, .csl, .csr, .css, .csv, .cur, .cus, .d07, .dac, .dat, .db, .dbf, .dch, .dcr, .ddd, .dds, .defx, .der, .des, .dgc, .dif, .dip, .djv, .djvu,
dng, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .drw, .ds4, .dsb, .dsf, .dtau, .dtd, .dtl, .dwg, .dxf, .dxi, .ebc, .ebd, .ebq, .ec8, .efs, .efsl, .efx, .emd,
.eml, .emp, .ens, .ent, .epa, .epb, .eps, .eqb, .ert, .esk, .ess, .esv, .etq, .ets, .exp, .fa1, .fa2, .fca, .fcpa, .fcpr, .fcr, .fef, .ffd, .fim, .fla, .flac, .flv, .fmv,
.fon, .fpx, .frm, .fx0, .fx1, .fxr, .fxw, .fyc, .gdb, .gem, .gfi, .gif, .gnc, .gpc, .gpg, .gsb, .gto, .gz, .h, .h10, .h11, .h12, .hbk, .hif, .hpp, .hsr, .html, .hts, .hwp,
.i2b, .iban, .ibd, .ico, .idml, .iff, .iif, .img, .imp, .indb, .indd, .indl, .indt, .ini, .int, .intu, .inv, .inx, .ipe, .ipg, .itf, .jar, .java, .jng, .jp2, .jpeg, .jpg,
.js, .jsd, .jsda, .jsp, .kb7, .kd3, .kdc, .key, .kmo, .kmy, .lay, .lay6, .lcd, .ldc, .ldf, .ldr, .let, .lgb, .lhr, .lid, .lin, .lld, .lmr, .log, .lua, .lz, .m, .m10, .m11,
.m12, .m14, .m15, .m16, .m3u, .m3u8, .m4a, .m4u, .m4v, .mac, .max, .mbsb, .md, .mda, .mdb, .mdf, .mef, .mem, .met, .meta, .mhtm, .mid, .mkv, .ml2, .ml9, .mlb, .mlc, .mmb,
.mml, .mmw, .mn1, .mn2, .mn3, .mn4, .mn5, .mn6, .mn7, .mn8, .mn9, .mne, .mnp, .mny, .mone, .mov, .mp2, .mp3, .mp4, .mpa, .mpe, .mpeg, .mpg, .mql, .mrq, .ms11, .msg, .mwi,
.mws, .mx0, .myd, .mye, .myi, .myox, .n43, .nap, .nd, .nef, .nl2, .nni, .npc, .nv, .nv2, .oab, .obi, .odb, .odc, .odg, .odm, .odp, .ods, .odt, .oet, .ofc, .ofx,
.old, .omf, .op, .orf, .ost, .otg, .otp, .ots, .ott, .p08, .p12, .p7b, .p7c, .paq, .pas, .pat, .pcd, .pcif, .pct, .pcx, .pd6, .pdb, .pdd, .pdf, .pem, .per, .pfb,
.pfd, .pfx, .pg, .php, .pic, .pl, .plb, .pls, .plt, .pma, .pmd, .png, .pns, .por, .pot, .potm, .potx, .pp4, .pp5, .ppam, .ppf, .ppj, .pps, .ppsm, .ppsx, .ppt, .pptx,
.pr0, .pr1, .pr2, .pr3, .pr4, .pr5, .prel, .prf, .prn, .prpr, .ps, .psd, .psp, .pst, .ptb, .ptdb, .ptk, .ptx, .pvc, .pxa, .py, .q00, .q01, .q06, .q07, .q08, .q09, .q43,
.q98, .qb1, .qb20, .qba, .qbb, .qbi, .qbk, .qbm, .qbmb, .qbmd, .qbo, .qbp, .qbr, .qbw, .qbx, .qby, .qbz, .qch, .qcow, .qdf, .qdfx, .qdt, .qel, .qem, .qfi, .qfx, .qif, .qix,
.qme, .qml, .qmt, .qmtf, .qnx, .qob, .qpb, .qpd, .qpg, .qph, .qpi, .qsd, .qsm, .qss, .qst, .qtx, .quic, .quo, .qw5, .qwc, .qwmo, .qxf, .r3d, .ra, .raf, .rar, .raw, .rb, .rcs,
.rda, .rdy, .reb, .rec, .resx, .rif, .rm, .rpf, .rsspptm, .rtf, .rtp, .rw2, .rwl, .rz, .s12, .s7z, .saf, .saj, .say, .sba, .sbc, .sbd, .sbf, .scd, .sch, .sct, .sdf, .sdy,
.seam, .ses, .set, .shw, .sic, .skg, .sldm, .sldx, .slk, .slp, .sql, .sqli, .sr2, .srf, .ssg, .stc, .std, .sti, .stm, .str, .stw, .svg, .swf, .sxc, .sxd, .sxi, .sxm, .sxw,
.t00, .t01, .t02, .t03, .t04, .t05, .t06, .t07, .t08, .t09, .t10, .t11, .t12, .t13, .t14, .t15, .t99, .ta1, .ta2, .ta4, .ta5, .ta6, .ta8, .ta9, .tar, .tax, .tax0, .tax1,
.tax2, .tb2, .tbk, .tbp, .tdr, .text, .tfx, .tga, .tgz, .tif, .tiff, .tkr, .tlg, .tom, .tpl, .trm, .trn, .tt10, .tt11, .tt12, .tt13, .tt14, .tt15, .tt20, .ttf, .txf, .txt,
.u08, .u10, .u11, .u12, .uop, .uot, .v30, .vb, .vbpf, .vbs, .vcf, .vdf, .vdi, .vmb, .vmdk, .vmx, .vnd, .vob, .vsd, .vyp, .vyr, .wac, .wav, .wb2, .wi, .wk1, .wk3, .wk4,
.wks, .wma, .wmf, .wmv, .wpd, .wpg, .wps, .x3f, .xaa, .xcf, .xeq, .xhtm, .xla, .xlam, .xlc, .xlk, .xll, .xlm, .xlr, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw,
.xml, .xpm, .xqx, .yuv, .zdb, .ziparc, .zipx, .zix, .zka
From the list we can assess that most popular user data file types are affected. Examples include the following:
- Images – Various types of graphic files which included both animated raster and vector images.
- Videos – Most of the widely used videos are included in the list.
- Configuration Files – Both system and application settings can be compromised by the encryption engine.
- Audio Files – Sound clips, music and all kinds of audio information are also affected.
- Archives –All widely used archives and compressed files are processed by the engine.
- Backups – Backup copies of important information are encrypted to prevent recovery.
- Documents – The list includes all popular formats used by Office software – rich text files, .
- TXT – Plain text files.
- WAV – An uncompressed audio file.
- XML – A markup document.
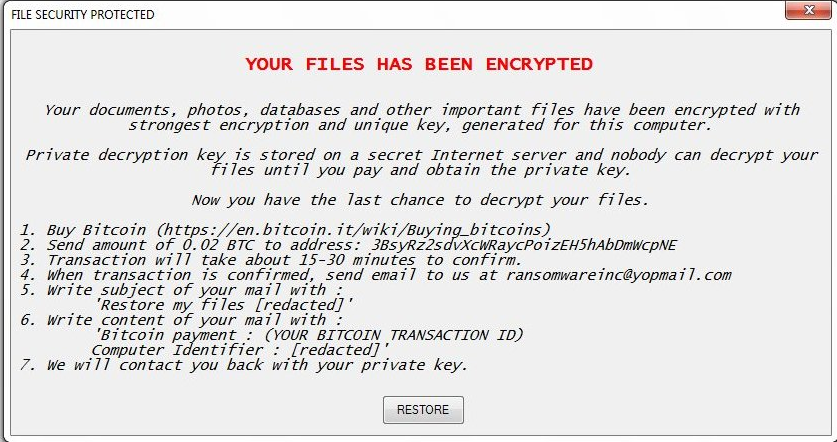
The encryption engine renames all affected data with the .encrypted extension. A ransomware note in an application window with the title “FILE SECURITY PROTECTED” is then displayed to the user:
YOUR FILES HAS BEEN ENCRYPTED
Your documents, photos, databases and other important files have been encrypted with strongest encryption and unique key, generated for this computer.
Private decryption key is stored on a secret Internet server and nobody can decrypt your files until you pay and obtain the private key.
Now you have the last chance to decrypt your files.
1. Buy Bitcoin (https://en.bitcoin.it/wiki/Buying_bitcoins)
2. Send amount of 0.02 BTC to address: 3BsyRz2scfvXcWRaycPoizEH5hAbDmWcpNE
3. Transaction will take about 15-30 minutes to confirm.
4. When transaction is confirmed, send email to us at [email protected]
5. Write subject of your mail with :
‘Restore my files ***’
6. Write content of your mail with :
‘Bitcoin payment : (YOUR BITCOIN TRANSACTION ID)
Computer Identifier : *** ‘
7. We will contact you back with your private key.
button [RESTORE]
This is a fairy standard message which requests a set amount of Bitcoins to be sent to the criminal operators. Unlike other more evolved viruses the Fake WindowsUpdater Ransomware does not feature a dedicated payment gateway. Instead the victims are given short directions on how to obtain the digital currency and how to send it to the hackers.
Its interesting to note that the person (or collective) behind it use the YOPmail email hosting solution which is unusual as most of the ransomware authors prefer to use the services of more popular ones. This service is a temporary one which keeps messages only for 8 days. Usually it is used to redirect the mail to other permanent inboxes and avoid detection.
Fake WindowsUpdater Ransomware Distribution
As it stems from the name of the ransomware the hackers usually distribute the virus as a counterfeit Windows update. Possible locations include hacked or hacker-controlled download sites and portals. The criminals usually use domain names or design that resembles Microsoft’s own sites to try and trick the victims into infecting themselves.
Other sources might include infected installers found on BitTorrent trackers where users can get a variety of different applications, most commonly pirate copies of famous programs. We suspect that the criminals may also use other distribution techniques such as email spam campaigns and scripts redirects through ad networks and browser hijackers.
Summary of the Fake WindowsUpdater Ransomware
| Name | Fake WindowsUpdater Ransomware |
| File Extensions | .encrypted |
| Ransom | 0.02 Bitcoins |
| Easy Solution | You can skip all steps and remove Fake WindowsUpdater Ransomware ransomware with the help of an anti-malware tool. |
| Manual Solution | Fake WindowsUpdater Ransomware ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution | Spam Email Campaigns, malicious ads & etc. |
Fake WindowsUpdater Ransomware Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
- 1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
- 1) Open My Computer/This PC
2) Windows 7
- – Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
- – Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
- 1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely Fake WindowsUpdater Ransomware Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
- 1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Fake WindowsUpdater Ransomware Files
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How To Restore Fake WindowsUpdater Ransomware Files
- 1) Use present backups
- 2) Use professional data recovery software
- – Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
- – Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
- – Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



